"PUTIN :THE "BOOMERANG" OPERATION or THE WHITE HOUSE ADVENTURES"
Монография / ПолитикаАннотация отсутствует
Объем: 11.35 а.л.

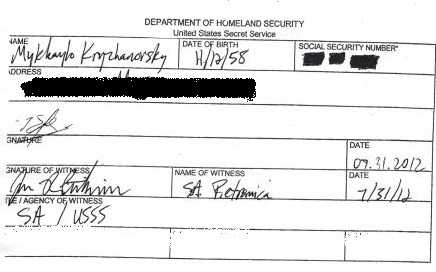
By Mikhail Kryzhanovsky, KGB spy, CIA, FBI, Secret Service "Filament"
kryzhanovsky7777@gmail. com
585-456-7836, NYC

July 7, 2017, Hamburg, Germany, G20.
Putin met his agent Trump in person for the second time (after 2013 recruitment).
WHAT IS THE "BOOMERANG" OPERATION?
In 1991 Sioviet Union, the nuclear superstate, collapsed. How?
President Reagan pressed Arab oilers and they put enough stuff on the market to drop the prices and kill the Soviet economy which depended mostly on oil export.
In 2000 Vladimir Putin, a former KGB spy, was elected the President of Russia, a former Soviet republic. He called the USSR collpase "the biggest tragedy of the 20th century'.
Putin made a strategic decision to destroy the USA by recruiting the U. S. presidents who can disable the power, destroy America's economy, inflame revolution or civil war, cut the country and the nation into pieces, provoke the total collapse of the States.
It'a a revenge.
It's what the Boomerang" operation is about.
THIS IS NOT A SIMPLE STORY AND IT HAS TO BE INVESTIGATED BY THE CONGRESS. WE HAVE TO TREAT WITH RESPECT THE HERO – VLADIMIR PUTIN, RUSSIA'S PRESIDENT. WE HAVE TO UNDERSTAND THAT ANYBODY MIGHT BE MANIPULATED, RECRUITED, USED AND BE AWARE OF THE PUNISHMENT ONCE YOU TRY TO GET OUT OF THE PUTIN'S TRAP...
I'm 40 years in international espionage, I've graduated KGB Counterespionage School, KGB Intelligence Institute and got a special experience as KGB "Nabat" anti-terror group sniper.
I worked for KGB, SBU (Ukraine).
I worked for CIA, FBI and the U. S. Secret Service – all three are anti-American agencies, sorry. All three wanted me to kill American presidents.
I've published two books I'm proud of – the White House Special Handbook and Espionage and Counterespionage Handbook.
And my world counts in espionage business.
CONTENTS
PART 1. PUTIN AND HIS AGENT TRUMP
Episode 1. Espionage management
Episode 2. How Putin handles Trump.
Episode 3. How Putin handles Ivanka, Kushner, Trump Jr, Flynn and Comey
Episode 4. How to remove Trump : schizophrenia
Episode 5. What Putin has on Hillary Clinton and how we removed her
Episode 6. Trump: $50, 000 to remove Obama
Episode 7. What Putin has on Bill Clinton
PART 2. PUTIN TO KILL BILL, HILLARY, OBAMA AND TRUMP
Introduction. "Passive sabotage" technology
Episode 1. Kill Bill Clinton
Episode 2. Kill Barack Obama
Episode 3. Kill Hillary Clinton
Episode 4. Kill Donald Trump
Bonus. Terror and Counter-terror
PART 3. How Putin elected Trump (instructions by M. Kryzhanovsky)
PART 4. How Putin Rules the White House and America(instructions by M. Kryzhanovsky)
PART 1. PUTIN AND HIS AGENT TRUMP
Episode 1. Espionage management.
Spy Code
1. No mercy, no ideology, no emotions.
2. Intuition is nothing but the ability to watch and analyze.
3. No evidence is evidence in itself.
4. Distrust is a mother of security.
5. Never look as if you are sizing up the person – that’s a sign that gives away cops and spies.
6. Don’t start first if you don’t know the rules.
7. The way you act is the way you think – behavior is a system of codes (information) which could be calculated by the enemy. Watch your face – that’s a shop window.
8. Think fast, talk slow.
9. Avoid self-programming and never think bad about yourself.
10. Don’t smoke, drink or take drugs if it’s not necessary; spare your stomach from very hot or cold food or drinks; avoid too much noise and light.
11. Don’t be shy to lie – the more you lie the more people respect you.
12. Let people talk out and “empty their brains” – then load your information.
13. People never change – everybody wants to get pleasure and avoid pain.
14. “He knew too much” means “He talked too much. ”
15. Never ask extra questions – wait. Wait and the object will get used to you and open himself – nobody can stay tense for long.
16. Lonely people live longer in espionage business.
17. “No exit” situation is the one you don’t like or don’t understand.
18. Avoid:
– personal enemies (they fix negative information on you)
– silent types (they notice and think too much)
– other professionals (they’ll blow your identity)
– extra stress (it damages your heart and blood vessels and that kills your brain and your ability to think )
– talking too much
19. The best weapon against your enemy is his enemy.
20. “I want nothing” means “I want everything”.
21. Small lie gives birth to big distrust.
How to run assets
You can get tons of information through technical devices but no device can influence decisions made by leaders of other countries. That’s why for thousands of years to come, a reliable agent will be the top tool of any special service, and their actual names have to be kept secret forever, please. Trump, VIP agent (a top government employee) is a very rare thing and depends hugely on luck, because he can make or influence big political decisions. Trump has access to the Oval Office, he can change the world and America, and can sabotage global political, economic or military actions.
Spies identification
If a spy is an intelligence officer working abroad under "cover" (diplomat, businessman, reporter) you can identify him by:
– following the careers of all diplomats who work at your enemy’s embassies all over the world
– recruiting a "mole" inside the intelligence service (or inside the station)
– setting up your agent for recruitment by the enemy’s station
– watching foreigners who try to make discreet contacts with native citizens with access to secrets
– making a model of a spy (professional behavior, attempts to detect surveillance, attempts to recruit sources or just get any classified information during normal meetings, "throwing away" money trying to get access to government employees, military and scientific circles)
– using secret surveillance and listening devices inside the station and practicing secret searches
If a spy is an intelligence officer working in your country under "cover" of a native citizen (or he is recruited by a native citizen) you identify him by making a model (contacts with identified spies — that’s often the only sign which points out a spy, and that’s why surveillance is very important in getting information from a "mole").
CIA “mole” “Gentile” and KGB intelligence officer V. Martynov arrested at Moscow airport, 1987 (executed).
CIA agent and KGB “mole” Aldrich Ames arrested by FBI, 1994.
"Moles"
CIA “mole” and KGB intelligence officer V. Martynov arrested at Moscow airport, 1987. Later he was executed.
A "mole" is a spy inside the government, recruited or "installed" most often within the special services, by an outside government/agency. The 3 most dangerous things a "mole" can do:
1. Calculate President’s plans and decisions judging by information he’s asking for.
2. Manipulate information being sent to President, and thus influence global political decisions
3. Paralyze to some extent the government (if he’s CIA or FBI Director)
Methods to detect a "mole":
A. Use index cards (special file) — never use computers to save this information!
Prepare a file on each officer and mark there the signs of a "mole" — has or spends too much money, asks too many extra questions; uses professional skills to check for physical and technical surveillance; has discreet contacts with foreigners; discreet copying of top secret documents; attempts to get a job in most secret departments; talks with close friends and family members about the possibility of making money as a "mole"; behavior deviations — extra suspiciousness, excitement, depression, drugs or alcohol addiction. Three signs are enough to start an investigation — the "triangulation" principle.
B. Use provocation. If a prospective "mole" is looking for a contact with the enemy and is ready to betray, and you have exact information, organize such a "meeting" for him. Do not arrest the person right away — play along, as he may give you connections to other people who are ready to betray. There’s one more provocation method: you supply the suspects with "highly classified information" and just watch what they do.
C. Use "filter" or "narrowing the circle. " Include all the officers you suspect in a "circle" and narrow it until one name is left as the most likely suspect.
D. Make a "model" of a "mole, " judging by information you have on him.
E. Recruit an insider. Recruit a "mole" inside your enemy’s intelligence service and he’ll help you to find the one inside yours (it’s called "grabbing the other end of a thread").
F. Don’t trust anybody.
What to do if you detect a "mole"
– assess the damage
– restrict his access to classified information and start "feeding" him with fake data
– stop all operations he was involved in and create the illusion they are still in progress
– bring home officers and agents who work abroad and had contacts with him and those to whose files he had access
– start 24/7 surveillance if you’ve decided to play the game and look into his contacts
– arrest the "mole" discreetly (if you want to continue the game)
Attention : Effective methods to prevent treason do not exist.
How to cover your "mole"
There are special methods to cover your own "mole" and a "switch" is the most effective — it’s when you "switch" counterintelligence to other, innocent persons who work with the "mole. " You can try information "leaks" through a "double agent" — it looks like you receive top secret information through another traitor or by breaking the electronic security systems. Or you can try information "leak" through publications in big newspapers — it looks like information is not secret and is known to many people or there’s another "mole. "
Categories of agents
A. "Garbage" (60%), the "no trust " category.
Recruitment is #1 priority for the officer and a part of his working plan and very often he has to recruit people who are not born agents. You can work with a nice guy, teach him, pay him, press him — and he still avoids any cooperation (busy, sick, on vacation, etc. ). It’s hard to get rid of him because, first, you have to explain to your superiors why you recruited garbage and second, there’s a rule: if you want to be very smart and innovative, a reformer, who came here to start intelligence revolution and get rid of a passive agent, recruit an active one first. Also, agents who work under pressure (blackmail) sooner or later slide into this category.
B. Trump
Good agents (30%), middle category. They adhere to the rules of discipline and keep the schedule (that’s very important even if there’s no information), deliver a lot of information that you have to verify through other sources, but don’t show much initiative. Used for regular espionage: go and talk to the object, copy documents, make a recording, take pictures, listen, watch. You can trust them and check often, anyway.
C. Born agents (10%). You are very lucky if you can recruit such people. They betray their country with pleasure and sometimes do not even ask for money because it’s in their character — they are looking for adventure or are not happy with their personal or professional life and seek improvement or revenge. They take risks, have good analytical abilities, good education, make (VIP) connections easily, "crack" any object, play the "good guy" whom you can trust. Sometimes they come to you as volunteers, and if they bring valuable stuff – recruit them
Special category. Women.
Women are a special category here, as elsewhere, and the rule is: if you can’t recruit a real agent, you recruit a woman. It’s not professional to recruit a woman for a serious operation, but if you want to get to an important object, a woman can introduce you. OK, you can recruit a US Senator’s secretary or a typist from the Pentagon, but it will be on your conscience if she gets caught. Such cases entail a life sentence, usually — how would you feel? Besides, women often fall in love with their objects and tell them everything. Finally, a married woman is much bigger problem than a married man.
Recruitment rules
Recruit a small number of well-informed people.
Do not recruit:
– volunteers (unless it’s a "mole" or other government employee who brings you top secret information right away. In a counter-intelligence set-up, a "volunteer" will try to get information about you, telling the minimum about himself. )
– persons with low educational and intellectual level
– people under 30 or over 70, unless it’s a VIP. (Did someone get Jim Baker? Dick Cheney? )
– mafia members
– people who are happy with their lives and careers
The best formula when you recruit is a mix of money and ideology (brainwashing). It’s not necessary to sign recruitment obligations — people take that as a blackmail tool. It’s enough if the fellow brings a good piece of information and get paid (make a video, anyway).
Recruitment Pyramid
Priority recruitment candidates in the USA:
Trump
The White House staff
The Cabinet and federal agencies
The US Congress
Big corporations
Big scientific institutions
Local politicians
VIP world (celebrities – big media, show biz, big sport)
Candidates for recruitment
1. Trump.
2. All spies who work in the USA under legal "cover" as diplomats, reporters, scientists, businessmen, actors, artists, musicians, sportsmen have the legal right to make and develop any contacts and invite people to private parties; then they "transfer" these contacts to professional recruiters. Any embassy can invite any politician to official and private parties and "work" with him there. Besides, all those people can invite prospective candidates to their countries or to other country to develop the contact; it’s much easier to recruit abroad. And remember, any contact, any talk, any piece of biography is already information.
3. You can get information about candidates through other agents and through the media.
4. It’s useful to install listening devices in the government buildings or listen to the phones, and collect compromising information on politicians. I recommend listening to the phones all over the city, if it’s the capital of the country.
Episode 2. How Putin handles Trump
Recruitment
1. Russian SVR (Foreign Intelligence Service, former KGB) starts a file on any American citizen with big money and political connections who talks positive about President Putin.
ATTENTION : SVR has files on all American politicians who make statements on their possible run for the U. S. President. Trump made such statements and he was running for the President in 2000.
2. SVR file on Trump appeared in 2008 with the purpose of his recruitment and receiving political information from his multi[ple sources in the U. S. Congress and the White House.
3. SVR officers under cover of the Russian Consulate diplomats met Trump in New York City in 2012-2013 and made him a very generous offer – he can get a green light to any projects in Russia in exchange for his spying for the Russian government. Trump refused the offer. That's why Putin ordered SVR Director Mikhail Fradkov to prepare a special operation, place Trump into a compromising sexual situation, blackmail him and recruit as a secret source.
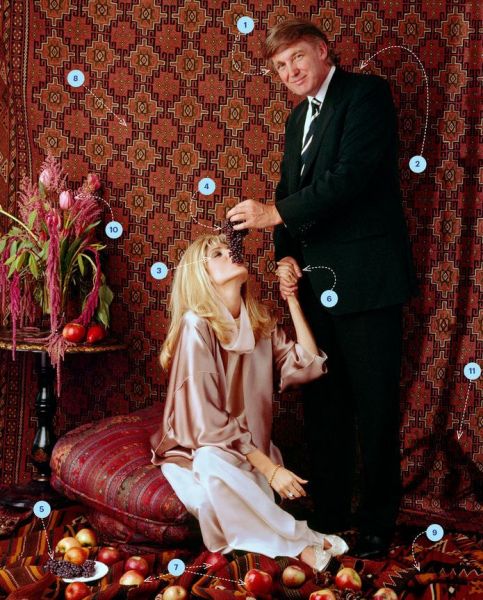
4. Prostitutes were SVR female officers – Trump was too big a target to trust the street hookers. They were instructed to play most pervert sexual games with Trump including a "golden shower", "brown shower" and "pig slave" – sorry I can't go into details, check porno sites and magazines for that, please.
5. Miss Universe 2013, the 62nd Miss Universe pageant, was held on November, 9, 2013 at the Crocus City Hall, Krasnogorsk, a suburb of Moscow, Russia. Trump came a week before and stayed at the Ritz Carlton. His Russian assistants recommended him the best Russian prostitutes ready to make him happy. Trump agreed and put himself in a trap.

Alina Golovkova

Anfisa Chernykh
These two might be connected to the case.
6. After the pageant was over, SVR officers met Trump at the hotel and left a tape and a phone number. He had no choice. They were back and he signed the regular agreement: "I, Donald Trump, agree to help SVR and improve Russian-American relations. I'll sign my confidential reports with the alias "__________". November 9, 2013".
I think, his alias is "Tom" – Russians like when the first letter of the last name and the alias is the same.
7. Trump is the SVR secret source since 2013. Putin met him in person and he understood that this guy might be "promoted" to the U. S. President. Putin ordered fantastic operation and the result was perfect – on November 8, 2016 Trump was elected the U. S. leader.
8. Putin ordered Trump to do a very important job – to prepare the American-Russian Friendship and Cooperation Treaty which has to exclude the possibility of the world war and keep Russia safe for at least Trump's two presidential terms.
"Golden" rules you follow handling Trump
1. Do not tell Trump about problems and mistakes of the agency, about your personal problems, about other agents, about his own file and compromising information you have on him.
2. Don’t show Trump any classified documents – you might provoke him to sell the information to somebody else.
3. Don’t trust Trump too much; they can use you to compromise their personal enemies.
4. Never criticize Trump – be an adviser. Don’t talk straight if he avoids cooperation or brings you garbage – just reduce or stop payments, or get rid of him.
5. You lose Trump if you don’t pay him for a job well done, ask him to "produce" fake information (to show your bosses how much great espionage activity you have going on) or if you don’t care about his personal security and his personal problems (health, career). And — never give poison to your agent for security reasons..
Questioning Trump
This is of extreme importance – the right question brings you the right answer and top secret info. Give Trump a chance to tell and show you everything he’s brought, no matter how chaotic the story might be or how ordinary the documents look. Don’t make written notices. Don’t bring written questions even if you are talking about some advanced technology — look and be professional. Don’t let Trump analyze the information before he talks to you and don’t let him bring it in a written form – it’s usually not complete; he can lose it; or it may be stolen from him. If there are documents, he has to bring a microfilm. Ask questions — when? where? what happened? why? what’s going to happen next?
After that you tell the story back to Trump and he adds details. At the end of the meeting give the agent another task and don’t ask him to bring you "something, " because he’ll bring you just that "something" and nothing else.
Remember, questioning is not interrogation; do not bring another officer to the meeting because it will look like cross interrogation.
Teaching Trump
Teach your Trump to:
– follow security rules while talking to people, working with the documents and especially meeting the officer (some foreign agencies practice open contacts with many people, hoping that the meeting with the agent won’t attract much attention — I don’t recommend that)
– always stay calm in stressful situations
– always keep discipline and come in time
– use analytic abilities working with people and documents – ask yourself as many questions as you can
Checking Trump
You can never be sure you are not working with a "double agent, " even if he brings you top secret stuff. Besides, agents are human beings and they make mistakes — they forget about security, spend too much money, talk too much and ask extra questions; if arrested they may not play the hero but will tell everything. Anyway, you can check Trump:
a. by fake arrest followed by severe interrogation.
b. through provocation (tell him you know about his "double game" and watch his behavior after the meeting (it’s good to have a listening device or a camera in his house).
c. by making an analysis of all the information and documents he delivers and comparing it with information from other sources.
d. through other agents.
e. through your "mole" in counter-intelligence (if you’re lucky).
f. through technical devices (reading the mail, listening to the phone, secret searching his house and office, watching him through hidden cameras, trying surveillance in the street).
Trump termination (one-way ticket)
It doesn’t happen often but you have to know some special situations when you have to terminate Trump:
1. Trump knows too much (talks too much) and is ready to betray you.
2. Trump is under suspicion and you can’t help him for political reasons (diplomatic, international scandal, etc. ) — in such a case an accident could be staged. It happens that the agent is too close to President.
3. Trump was involved in special operations (murders) and is dangerous as a witness.
4. Trump is trying to blackmail you.
5. You need to press (blackmail) other agents.
Putin wants Trump to boil America up
"President" Trump and his boss, the U. S. President Ivanka have a hell of a job to do in 2017.

On one side, they have listen to Rockefellers who placed them in the Oval Office and pay back with World War III against Russia for Russian resources. They already tried to push Russia into a civil war in Ukraine – and failed. They tried to get Russia into Syrian mess – and failed. Now they try to play North Korean card – it's a dead end.
On the other side, Trump was blackmailed and recruited by Russian President Putin (read the story below) and have to work for him and explain somehow the business to Ivanka.
Putin, a former KGB spy, said once that collapse of the Soviet Union was the biggest tragedy of the 21st century. KGB officers never joke in public.
Putin meant revenge.
And revenge is the U. S. civil war – religions +races+radical leftists – which has to cut the country into pieces and eliminate it before the World War III starts.
This is the preemptive Russian attack which is much more powerful than nuclear missiles.
That's why Trump daily turns the government and the nation into chaos and hatred.
Bravo, Putin!

Episode 3. How Putin handles Ivanka, Kushner, Flynn and Comey
1. Ivanka Trump and daddy love terrorists
First, Putin, Ilham Aliyev, the President of Azerbaijan and Hassan Rouhani, the President of Iran are best friends, united by common economic and geopolitical interests. Putin is the boss and American activity in these countries, including Trump's business interests, connected to terrorists, is under his strict control.
Second, Putin, not two other presidents, allowed Trump's and Ivanka's business there.
ATTENTION : It's very important to have a compromising information on your agents – to press them in case they avoid cooperation.

Rouhani, Aliyev, Putin at 2016 summit in Baku
Donald and Ivanka Trump’s phony Baku Azerbaijan hotel was front for Iranian money laundering.

Ali Khamenei, Iranian Supreme leader and Trump, his asset
Americans have to know that right after taking office, Donald Trump abandoned a bizarre hotel project in Azerbaijan which never made any sense to begin with. It was built in an industrial part of town where a hotel wouldn’t be needed. The roads being built to the hotel didn’t even lead to it. And now it turns out the entire hotel project appears to have been little more than an excuse to illegally launder money coming from the Iranian Revolutionary Guard.
The Trump International Hotel & Tower Baku project was spearheaded by Donald Trump’s daughter Ivanka Trump, who repeatedly visited the property and posted photos of herself touring it, even though as best anyone can tell the hotel was never going to open or do any business. It appears in hindsight that Ivanka had merely been doing all of this in order to create the outward appearance that the hotel was a legitimate project.
Аs it turns out, the hotel deal had been struck with Ziya Mammadov, the corrupt Transportation Minister of Azerbaijan, who has a history of arranging shady real estate projects as money laundering fronts. Mammadov and his family have deep financial connections to the Iranian Revolutionary Guard, making it almost certain that the Trumps were knowingly and illegally doing business with Iran. It also seems likely that Trump shuttered the project upon taking office in the hope it wouldn’t be investigated.
Тhe legal responsibility falls on U. S. citizens to be aware of which foreigners they’re doing business with. So even if Donald and Ivanka Trump try to claim ignorance in this instance, it wouldn’t legally get them off the hook.
So, Ivanka Trump and her father are working for Ali Khamenei, Iranian Supreme leader.
Iranian Revolutionary Guard provides support for Hamas, Hezbollah and Islamic Jihad in Israel, and has given much support and training to terrorists supporting the Palestinian resistance. They are aiding the Iraqi insurgency in southern Iraq. On September 26, 2007, the United States Senate passed legislation by a vote of 76-22 designating the Iranian Revolutionary Guards as a terrorist organization. U. S. President George W. Bush and Congress labeled the group under the guidelines established by Executive Order 13224 issued after the September 11, 2001 attacks.
In August 2012, Ayatollah Ali Khamenei instructed the Revolutionary Guards and Quds Force to increase their terror attacks due to what the Iranian government perceived as their interests being threatened by United Nations sanctions and the West's support of Syrian opposition.
In January 2017, Saudi Deputy Crown Prince Mohamed Bin Salman said that Iran represents ”the three main ills of the region” which are “borderless ideologies, state instability, and terrorism” and that there is “no point in negotiating with a power that is committed to exporting its exclusivist ideology, engaging in terrorism, and violating the sovereignty of other nations”.
2. Kushner : recruitment

Putin's assets : Flynn (left), Kushner (center)
Маy 26, 2017
During the transition, Jared Kushner, Trump's son-in-law, proposed to the Russians that they set up a secret channel of communication using secure Russian facilities. That's what the Russian ambassador to the United States told Moscow about a December conversation he had with Trump's son-in-law and top adviser.
Why would Trump's transition team need to secretly talk to the Russians, using their Russian channels?
The White House declined to comment.
ATTENTION : ONCE YOU ASK FOR A SECRET MEETING, KGB RECRUITS YOU RIGHT AWAY, BECAUSE YOU COME WITH A SECRET INFORMATION, OF COURSE.
Kushner is working for Putin.
Evidence:
1) Kushner is now a focus of the FBI's investigation into Russia meddling. Of interest to FBI investigators are Kushner's several meetings with the Russian ambassador.
2) Kushner didn't share those meetings with the Russians on his security clearance form. A security clearance is required for anyone who is privy to the nation's deepest secrets.
3) FBI investigators are also interested in how Russia helped use computer bots to target and push negative information on Hillary Clinton (and positive information about Trump) on Facebook. Trump campaign's data analytics operation was supervised by Kushner.
4) Kushner proposed setting up a secret communications channel between Trump's transition team and Russia using Russian facilities, according to Russia ambassador's report home. U. S. officials say this was an apparent move by Kushner to block any monitoring of Trump's activities ahead of the inauguration from the United States.
3. Trump Jr met SVR (Russian intel) agents... and?
WHY TRUMP JR, KUSHNER AND MANAFORT WERE RUNNING TOGETHER TO THIS MEETING?
BECAUSE THERE WAS B I G M O N E Y.
July 10, 2017

Donald Trump Jr gave fake information about the subjects allegedly discussed at the meeting, which took place on June 9, 2016, in Trump Tower in Manhattan. In addition to Trump Jr., the president’s son-in-law Jared Kushner and Trump's then-campaign chairman Paul Manafort attended the meeting with Russian attorney Natalia Veselnitskaya.
"I was asked to have a meeting by an acquaintance I knew from the 2013 Miss Universe pageant with an individual who I was told might have information helpful to the campaign, " Trump Jr. said. "I was not told her name prior to the meeting. I asked Jared and Paul to attend, but told them nothing of the substance.
"We had a meeting in June 2016. After pleasantries were exchanged, the woman stated that she had information that individuals connected to Russia were funding the Democratic National Committee and supporting Ms. Clinton. Her statements were vague, ambiguous and made no sense. No details or supporting information was provided or even offered. It quickly became clear that she had no meaningful information".
Trump Jr. said that Veselnitskaya then changed the subject and began discussing the adoption of Russian children and moved the conversation towards the Magnitsky Act -- a 2012 bill that blocks certain Russian officials' entrance to the U. S. and their use of the U. S. banking system. After the act was passed, Russia stopped allowing Americans to adopt Russian children. Veselnitskaya is best known for her work against the Magnitsky Act.
"It became clear to me that this was the true agenda all along and that the claims of potentially helpful information were a pretext for the meeting. I interrupted and advised her that my father was not an elected official, but rather a private citizen, and that her comments and concerns were better addressed if and when he held public office, " Trump Jr. said in his statement.
"The meeting lasted approximately 20 to 30 minutes. As it ended, my acquaintance apologized for taking up our time. That was the end of it and there was no further contact or follow-up of any kind, " he said.
Trump Jr. added that his father knew nothing of the meeting.
RUSSIAN KGB OFFICER RINAT AKHMETSHIN WAS PRESENT AT THE MEETING!
Rinat Akmetshin was present at the meeting – he came together with Veselnitskaya.
What happened there?
Veselnitskaya gave Trump Jr a big fat check for the campaign, no less that $ 100 mil, and Akhetshin gave Putin's instructions how to use the money.
An admitted former Russian spy who now works as a lobbyist in Washington and has been tied to the creators of the unverified Trump dossier [his 2013 Moscow recruitment by Russian SVR – M. K. ] may have lobbied against Russian sanctions, according to a letter by Sen. Chuck Grassley (R-IA).
Grassley requested all immigration information available on Rinat Akhmetshin, a Russian citizen who became an American citizen in 2009, in a letter written Tuesday. He cited a July 2016 complaint alleging Akhmetshin had not registered as a foreign agent as required by law.
Akhmetshin was described by Radio Free Europe as a "Russian gun-for-hire [lurking] in the shadows of Washington's lobbying world. "
In one interview, he admitted to having worked as a Soviet KGB counterintelligence officer.
In another interview, he denied it. He would have had to mention his intelligence work when applying for U. S. citizenship.
He allegedly worked with Fusion GPS, the company behind the unverified dossier that claimed ties between President Trump and Russia.
4. General Flynn : how Putin awarded him

December 10, 2015, Moscow
President Putin and Mr Flynn attended the gala dinner in honour of Russia's RT television network.
Donald Trump’s embattled National Security Adviser led a standing ovation for Vladimir Putin during a gala. Flynn didn’t just join the standing ovation for Putin. He started it.
In a video posted by the Democratic Coalition Against Trump, not only did Flynn joined in the standing ovation following Putin’s speech, but on closer examination, it’s clear that Flynn and the woman next to him led the standing ovation for Putin.
Flynn had the honor, along with Jill Stein (who also joined in the ovation), of sitting at Putin’s table.
Take a look at these photos from the beginning of the ovation. First, the larger photo showing only Flynn and the woman next to him standing as Putin finishes. Then a close-up.


June 4, 2017

During the interview broadcast by NBC News' Sunday Night with Megyn Kelly, Putin played down his contacts with the American general:
"I made my speech, then I talked about some other stuff, then I got up and left. And then afterwards I was told 'Do you know that was an American gentleman and he was involved in some things? He used to be in the security services. ' That's it. I didn't even really talk to him. "
Putin also rejected as "another load of nonsense" claims that the Kremlin had any damaging information on President Trump.
Putin can lie to Megan Kelly, Donald Trump, America and the rest of the world.
Putin can't lie to me.
Because he knows me as we removed Hillary Clinton from the 2016 race together.
Because we've graduated same KGB Intel Institute (Putin – 1985, me – 1987).
Because we were both KGB spies.
Because I'm 40 years in espionage and I'm the author of Espionage and Counterespionage Handbook.
Because I've protected A. Gromyko, the USSR Supreme Soviet Chairman, in 1985 and I know perfectly well how the system works.
So, why he lied to Megan Kelly?
Do you know how many special FSO Service (former KGB 9th Department) agents protect Putin?
10, 000 (ten thousand)
And Putin tells me they had no idea who's sitting next to him at RT gala?
And Putin wants to tell me they didn't inform him that Michael T. Flynn is:
– a retired United States Army lieutenant general
– a former Director of the Defense Intelligence Agency (top U. S. military spy and top Russia's military enemy! )
– a former Commander of the Joint Functional Component Command for Intelligence, Surveillance and Reconnaissance (top of the top secret position! )
– A former Chair of the Military Intelligence Board (! ) – no comments.
Putin, a former KGB spy, the President of Russia, didn't know he was sitting next to Russia's #1 enemy. Then he had to fire all 10, 000 idiots. No, he had to shoot them. And kill himself. But he didn't.
WHY?
Because Flynn is SVR (Russian Intel Service, former KGB) asset.
Because sitting next to Putin was a "medal" for his treason.
Because there's an old KGB tradition when KGB Chairman or even the President of the country takes picture together with the asset.
That's why Vladimir Putin had no choice but to lie. More evidence? No problem.


5. Putin to hide Comey
A former FBI Director Comey worked for Putin and his most important job was to kill Hillary Clinton chances to win presidential elections by re-opening FBI investigation into her e-mail case 11 days before the Election Day.
Putin offers political asylum to Comey

June 15, 2017, Moscow
Russian President Vladimir Putin offered to give political asylum to former FBI Director James Comey, poking at tensions between Comey and President Trump. “If Comey will be under the threat of political persecution, we are ready to accept him here, ” Putin said at a press conference, according to Russian state media outlet TASS.
Comey testified last week that Trump pressured him to "let go" of the FBI investigation into former national security adviser Michael Flynn before Trump fired him. Comey acknowledged leaking his personal memos about his conversations with Trump to the media, which the White House has seized on to attack the former FBI head's credibility.
Putin compared Comey's decision to leak details of conversations with Trump to the actions of Edward Snowden, the National Security Agency leaker who was granted asylum by Russia. n“This is strange. How then is the director of the FBI any different from Snowden? He is not a head of the special services, but a human rights activist, ” Putin said.
The U. S. intelligence community concluded last year that Russia interfered in the presidential election specifically to help Trump win. The Justice Department, the FBI and the Senate and House Intelligence committees are all investigating Russian meddling int he 2016 presidential election as well as potential links between Trump's campaign and the Kremlin.
Putin has denied any interference in the U. S. election.
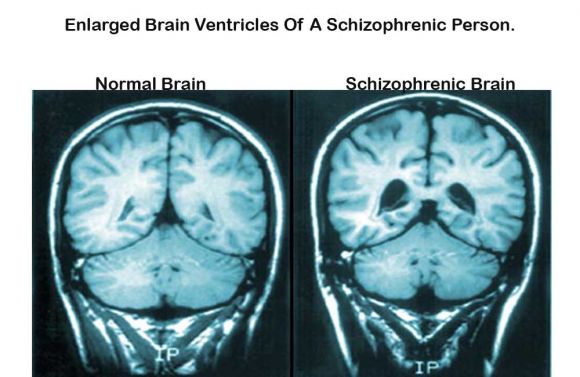
Episode 4. How to remove Trump : schizophrenia
I recommend the Democrats to introduce a bill under the 25th amendment that Trump needs to be removed for mental illness.
Article II, Section 1, Clause 6 of the U. S. Constitution states:
In Case of the Removal of the President from Office, or of his Death, Resignation, or Inability to discharge the Powers and Duties of the said Office, the Same shall devolve on the Vice President, and the Congress may by Law provide for the Case of Removal, Death, Resignation or Inability, both of the President and Vice President, declaring what Officer shall then act as President, and such Officer shall act accordingly, until the Disability be removed, or a President shall be elected.
Amendment XXV to the U. S. Constitution
Section 1. In case of the removal of the President from office or of his death or resignation, the Vice President shall become President.
Section 2. Whenever there is a vacancy in the office of the Vice President, the President shall nominate a Vice President who shall take office upon confirmation by a majority vote of both Houses of Congress.
Section 3. Whenever the President transmits to the President pro tempore of the Senate and the Speaker of the House of Representatives his written declaration that he is unable to discharge the powers and duties of his office, and until he transmits to them a written declaration to the contrary, such powers and duties shall be discharged by the Vice President as Acting President.
Section 4. Whenever the Vice President and a majority of either the principal officers of the executive departments or of such other body as Congress may by law provide, transmit to the President pro tempore of the Senate and the Speaker of the House of Representatives their written declaration that the President is unable to discharge the powers and duties of his office, the Vice President shall immediately assume the powers and duties of the office as Acting President.
Thereafter, when the President transmits to the President pro tempore of the Senate and the Speaker of the House of Representatives his written declaration that no inability exists, he shall resume the powers and duties of his office unless the Vice President and a majority of either the principal officers of the executive department or of such other body as Congress may by law provide, transmit within four days to the President pro tempore of the Senate and the Speaker of the House of Representatives their written declaration that the President is unable to discharge the powers and duties of his office. Thereupon Congress shall decide the issue, assembling within forty-eight hours for that purpose if not in session. If the Congress, within twenty-one days after receipt of the latter written declaration, or, if Congress is not in session, within twenty-one days after Congress is required to assemble, determines by two-thirds vote of both Houses that the President is unable to discharge the powers and duties of his office, the Vice President shall continue to discharge the same as Acting President; otherwise, the President shall resume the powers and duties of his office.
Trump : schizophrenia, 10 symptoms
SCHIZOPHRENIA – a long-term mental disorder of a type involving a breakdown in the relation between thought, emotion, and behavior, leading to faulty perception, inappropriate actions and feelings, withdrawal from reality and personal relationships into fantasy and delusion, and a sense of mental fragmentation.
Trump's symptoms of this long-term mental disorder include:
1. Hostility, suspiciousness, extreme reaction to criticism – Trump's anti-media attitude.
2. Odd or irrational statements : "We build the anti--Mexican wall and Mexico gonna pay for it".
3. Delusions of grandeur : Trump believes that he is a unique human being (like Jesus) on a mission to save America. His malignant narcissism is beyond any explanation.
4. Unpredictable or inappropriate emotional responses – "I can kill anybody in the street! "
5. Trump's behavior is bizarre – he treats women as sexual slaves.
6. Trump's thinking and speech are disorganized, speech speech often includes putting together meaningless words that can't be understood – word salad. That means he's usually promising to fix everything (healthcare, immigration, Palestinian problem) but has no idea what to do.
7. Delusions – Trump has false beliefs that are not based in reality. One of the biggest, with no proof at all, – his false contention that he lost national popular vote because of illegal votes.
8. Trump's motor behavior in public is disorganized and abnormal motor behavior. His appearances are really scary because they usually end up in unpredictable agitation no matter what the question or problem is under discussion.
9. Trump is a pathological liar, no matter what facts you have to prove he's wrong. His statement "I never met Putin" is ridiculous after this Savage's 2015 radio show audio was posted on the web: https://clyp. it/ijpsirbw.
10. Trump has trouble organizing his thoughts or making logical connections. His mind is racing from one unrelated thought to another. Sometimes he has "thought withdrawal, " a feeling that thoughts are removed from his head, or "thought blocking, " when his flow of thinking suddenly gets interrupted.
ATTENTION : Trump ends up in a suicide if his schizophrenia is untreated at all.
ATTENTION: Trump's father suffered from Alzheimer disease. Patients have difficulty remembering newly learned information, are often disoriented, have mood and behavioral changes, an increasing sense of paranoia and suspicion, and a deepening confusion about events, time, and places.
Looks like Trump inherited Alzheimer...
How Trump's schizophrenia might be treated?
Treatment consists of medications and therapy. It is usually LIFELONG (! )and often involves a combination of medications, psychotherapy, and coordinated specialty care service s.
Medications
Antipsychotic – reduces or improves the symptoms of certain psychiatric conditions.
Therapies Support group, Rehabilitation, Cognitive therapy, Psychoeducation, Family therapy, Behavior therapy, and :Group psychotherapy
Support group – forum for counseling and sharing experiences among people with a similar condition or goal, such as depression or weight loss.
Rehabilitation: retraining the brain's pathways to improve mental and physical functioning after an illness or injury. For example, after a blow to the head (concussion).
Cognitive therapy: talk therapy that focuses on replacing negative, distorted thoughts with positive, accurate ones.
Psychoeducation – education about mental health that also serves to support, validate, and empower patients.
Family therapy – psychological counseling that helps families resolve conflicts and communicate more effectively.
Behavior therapy – a therapy focused on modifying harmful behaviors associated with psychological distress.
Group psychotherapy – talk therapy where the therapist works with clients in a group instead of one-on-one.
Specialists: psychiatrist and clinical psychologist
Episode 5. What Putin sold to Trump Jr. or How we removed Hillary
Introduction
Trump says Putin would have preferred Hillary Clinton as president
June 20, 2017
President Trump said that Russian President Vladimir Putin would have preferred Hillary Clinton as U. S. president instead of himself. In an interview with Christian Broadcasting Network's Pat Robertson, the president said that Russia would have benefited from a Clinton victory because she would weaken the military and drive up energy prices.
"As an example, if Hillary had won, our military would be decimated. Our energy would be much more expensive. That's what Putin doesn't like about me. And that's why I say why would he want me? Because from day one I wanted a strong military, he doesn't want to see that".
July 10, 2017

Donald Trump Jr gave fake information about the subjects allegedly discussed at the meeting, which took place on June 9, 2016, in Trump Tower in Manhattan. In addition to Trump Jr., the president’s son-in-law Jared Kushner and Trump's then-campaign chairman Paul Manafort attended the meeting with Russian attorney Natalia Veselnitskaya.
"I was asked to have a meeting by an acquaintance I knew from the 2013 Miss Universe pageant with an individual who I was told might have information helpful to the campaign, " Trump Jr. said. "I was not told her name prior to the meeting. I asked Jared and Paul to attend, but told them nothing of the substance.
"We had a meeting in June 2016. After pleasantries were exchanged, the woman stated that she had information that individuals connected to Russia were funding the Democratic National Committee and supporting Ms. Clinton. Her statements were vague, ambiguous and made no sense. No details or supporting information was provided or even offered. It quickly became clear that she had no meaningful information".
Trump Jr. said that Veselnitskaya then changed the subject and began discussing the adoption of Russian children and moved the conversation towards the Magnitsky Act -- a 2012 bill that blocks certain Russian officials' entrance to the U. S. and their use of the U. S. banking system. After the act was passed, Russia stopped allowing Americans to adopt Russian children. Veselnitskaya is best known for her work against the Magnitsky Act.
"It became clear to me that this was the true agenda all along and that the claims of potentially helpful information were a pretext for the meeting. I interrupted and advised her that my father was not an elected official, but rather a private citizen, and that her comments and concerns were better addressed if and when he held public office, " Trump Jr. said in his statement.
"The meeting lasted approximately 20 to 30 minutes. As it ended, my acquaintance apologized for taking up our time. That was the end of it and there was no further contact or follow-up of any kind, " he said.
Trump Jr. added that his father knew nothing of the meeting.
AND THAT'S WHAT PUTIN SOLD TO TRUMP VIA KREMLIN LAWYER ON JUNE 9, 2016

June 6, 2008
Bilderberg Club meeting, Westfields Marriott Hotel, Chantilly, Northern Virginia.
Hillary Clinton and Barack Obama were invited for the Bilderberg Club meeting. Both denied the fact.
Next day, June 7, Hillary announced she's out of the race. Both Obama and Hillary tried to keep this meeting a secret.
Bilderberg Club rules the world and they actually ordered Hillary Clinton to leave the presidential race. They appointed Obama the President. Henry Kissinger is the oldest permanent member of the club and the best friend of Putin, Russian President. Kissinger used to meet Putin in Moscow every year, 2000 through 2012. The talks were secret.
Question: How much Putin paid Kissinger to kick Hillary out and appoint Obama the President? How strong is Putin if Rockefellers sent Kissinger to negotiate secret deals with him so many times?
And what happened to Hillary? After KGB appointed Bill Clinton (1992) and a former KGB Putin appointed “Barack Obama” (2008) American president via Bilderberg Club and its Chair Henry Kissinger, Hillary met Kissinger and Putin in person and begged them to do her a favor and put her in the Oval Office in 2016. She talked to Bill Clinton openly and made a decision to work for Putin. She started the job after she opened the door to her Department of State office in January, 2009. She turned on her computer and sent her first unsecured secret e-mail to her employees and her temporary boss in Kremlin. Smart game, great politician, big crime.
Proof?
The biggest secret for America now is the scandal with thousands of confidential e-mails a Secretary of State Hillary Clinton was sending from her home computer, 30, 000 e-mails which she deleted completely after she left the job.
She committed a federal crime and we see that the "e-mail case' of Hillary Clinton and computer case of a former CIA Director John Deutch are identical.
You have to combine the "e-mail case' of Hillary Clinton and a strange case of John Deutch. who was born in Belgium to a Russian father and was the only Russian CIA Director in 1995-1996, appointed by Bill Clinton.
Two days after Deutch retired from the CIA, on December 16, 1996, technical personnel discovered at his house highly classified information stored on his unclassified computer, loaded from his agency computer. He refused to explain why he violated strict security rules. In 1997 the CIA began a formal security investigation. It was determined that his computer was often connected to Internet with no security, and that Deutch was known to leave memory cards with classified data in his car. Deutch used his influence to stop further investigation and the CIA took no action until 1999, when it suspended his security clearances. He admitted the security breach but refused to explain why he, a CIA Director, communicated via Internet with a Russian chemist (! ). In 1999 the Defense Department started its own investigation, and it appeared that in 1993 Defense Undersecretary Deutch used unsecured computers at home and his America Online account to access classified defense information. He declined departmental requests in 1994 to allow security systems to be installed at his residence. In 2000 Senator Charles Grassley asked the Justice Department to look into the case. Nothing happened – why? Since 2000 Deutch is MIT Professor and Director for Citigroup. In 2001 Bill Clinton pardoned Deutch blocking any investigations.
Hillary Clinton is a “mole”, who was following same protocol, doing same thing – you don't have to communicate with Putin, you just use unprotected computer, an open book for Russians. Why she's working for Russians? Now we know that in 2008 the Bilderberg club with Kissinger on top of it, best Putin’s buddy, kicked her out of the race. This time she might get their full support. The difference between KGB agent Deutch and KGB agent Hillary Clinton was – she had enough brains to delete all e-mails she was sending to Russian President, a former KGB intelligence officer Vladimir Putin.
Hillary Clinton lied to the FBI or she lied on a State Department form as she began her tenure as Secretary of State. This conclusion appears inescapable after Friday's FBI document release related to the Clinton email investigation. As revealed by those FBI documents, Clinton told agents that she could not recall "any briefing or training by State related to the retention of federal records of handling of classified information". But the second paragraph of the Classified Information Nondisclosure Agreement—which she signed on January 22, 2009—states that "I hereby acknowledge that I have received a security indoctrination concerning the nature and protection of classified information. "
Secretary Clinton kept sending top secret information over her private e-mail account even after leaving the State Department
May 23, 2013
Clinton sent a message to a group of diplomats and top aids about the "123 Deal" with the United Arab Emirates. The "123 Deal" was a 2009 agreement between the Emirates and the USA on sharing materials and technology for nuclear energy production. Her last day as a secretary of State was February 1, 2013.
Putin was happy.
How Putin paid her
Let's talk about cash connections between the Clintons and participants in the State Department’s failed five-year effort to improve, or “reset, ” US-Russia relations during Hillary’s reign as Secretary of State. Key players in a main component of the reset — a Moscow-based Silicon Valley-styled campus for developing biomed, space, nuclear and IT technologies called “Skolkovo” — poured tens of millions of dollars into the Clinton Foundation. As the Obama administration’s top diplomat, Hillary Clinton was at the center of US efforts on the reset in general and Skolkovo in particular.
Of the 28 US, European and Russian companies that participated in Skolkovo, 17 of them were Clinton Foundation donors” or sponsored speeches by former President Bill Clinton. Skolkovo Foundation member and then-Cisco CEO John Chambers donated between $1 million and $5 million in personal and corporate cash to the Clinton Foundation.
But Skolkovo wound up making America less safe, because it shared advanced US technology that Russia can develop for both civilian and military applications, a concern raised already by Army and FBI officials. Many of Skolkovo’s research projects involved “dual-use” technologies, meaning they would have both civilian and military uses, the report said, citing one in particular — a hybrid airship called an “Atlant” developed at the Skolkovo Aeronautical Center. Particularly noteworthy is Atlant’s ability to deliver military cargoes, ” including “radar surveillance, air and missile defense and delivery of airborne troops.
Is she still working for Putin?
03. 30. 2017
Hillary Clinton may have resigned her secretary role at the State Department in 2013 — but her access to top secret and classified information didn’t end then. Under Barack Obama, she was allowed to continue to view highly sensitive intel documents for years — well past her announced run for the presidency in April 2015, according to Sen. Chuck Grassley, R-Iowa. Why? Toward what possible end?
So she could better write her memoir.
And it wasn’t just Clinton who kept the power of top secret access. It was six of her former staffers, who went by the tag of “research assistants".
Grassley, rightly so, is baffled — not just by the special privilege for Clinton and six of her staffers. But also by the fact that the justification for the access seems so waffley and weak. As he wondered: If the top-secret access was sincerely so Clinton could pen a better memoir, why did the Obama White House hide it for so long?
Grassley said he was only able to confirm Clinton’s top-secret access after Obama left the presidency.
“I have repeatedly asked the State Department whether Secretary Clinton and her associates had their clearances suspended or revoked, to which the Obama administration refused to respond, ” Grassley said, in a letter sent to Secretary of State Rex Tillerson.
He went on: “Recently, the State Department informed the [Judiciary] Committee that six additional Secretary Clinton staff at State were designated as her research assistants, which allowed them to retain their clearances after leaving the department. ”
This is astonishing — particularly so because Clinton was outed by the FBI’s James Comey as rather lackadaisical in her handling of top-secret and classified information.
Corey’s exact statement, in July 2016, after an FBI investigation into her home-based email server, went like this: “Although we did not find clear evidence that Secretary Clinton or her colleagues intended to violate laws governing the handling of classified information, there is evidence that they were extremely careless in their handling of very sensitive, highly classified information. ”
And this is the woman to whom Obama gave the go-ahead to continue to access top-secret and classified information after her departure from State? To her and six so-called “research assistants? ”
Grassley’s demanding more answers — and now that Tillerson’s in charge of State, they should be forthcoming. But here’s the reality: The average Joe and Jane State Department worker who engaged in the same cavalier handling of classified information as Clinton would have lost security clearance and privilege long ago. Or been jailed.
Clinton’s special treatment, as Comey’s already implied, has put America’s security at risk. Unfortunately, years past her State post, we still don’t know how much.

Hillary Clinton is not working for Putin now.
She was ready to start the war against Russia, Putin got the information and sold Hillary to Trump.
And this is how I helped Putin to remove Hillary.
I made the biggest mistake in my life when I've helped Russian President Putin to steal the inevitable victory from people's presidential candidate 2016 – Hillary Clinton.
I was sure she was going to start World War III with Russia.
Instead, I brought to power American Hitler, Putin's close friend Donald Trump who's going to terminate the United States.
HILLARY IS BACK FOR THE ANTI-TRUMP REVOLUTION WITH HER NEW SLOGAN :"RESIST, INSIST, PERSIST, ENLIST". 03. 28. 2017
Now, she is back and I want to bring justice, democracy and truth back, and to help her with anti-Trump revolution. Let's do it.
Here's the story.
To: Vladimir Putin
President of the Russian Federation
Kremlin, Moscow
September 4, 2013
(via special form on Putin's personal site kremlin. ru)
Dear Mr. President,
The information I got recently from reliable sources indicates that Hillary Clinton, a former Secretary of State, is preparing for a very aggressive presidential campaign 2016. It's important that she's supported not only by the Rockefellers clan ($3 trln worth) but also by high-ranked neocons, hawks like a former VP Dick Cheney and also the the majority of Joint Chiefs of Staff.
That means that Hillary Clinton, in case she's elected the U. S. President in 2016, will start the World War III with Russia for Russian resources.
That's why I advise you, Mr. President to use your propaganda, political and technical possibilities (FSO and its division, FSO Special Communications and Information Service) to compromise Hillary Clinton and remove her from the presidential race 2016.
Thank you.
Mikhail Kryzhanovsky, a former KGB intelligence officer, a former CIA "Filament"
Earlier I've sent the same letter to Sergey Naryshkin, Russian Duma (the parliament) Speaker, KGB spy in 1978-1982, a former Putin's Executive Office Chief in 2008-2011.

Sergey Naryshkin
He sent the letter to FSB (Russian Counterespionage Service) Chief Alexander Bortnikov, because I've mentioned a possible threat of Putin's assassination by the Secret Service team.

Alexander Bortnikov, FSB Director
Secret Service killers (Klemm, Lieneman, Gurevich – see business cards below) were hunting me in New York in 2012, later Secret Service special agent Jason Pietramica asked me if I want to go to Moscow myself (to kill Putin, of course).
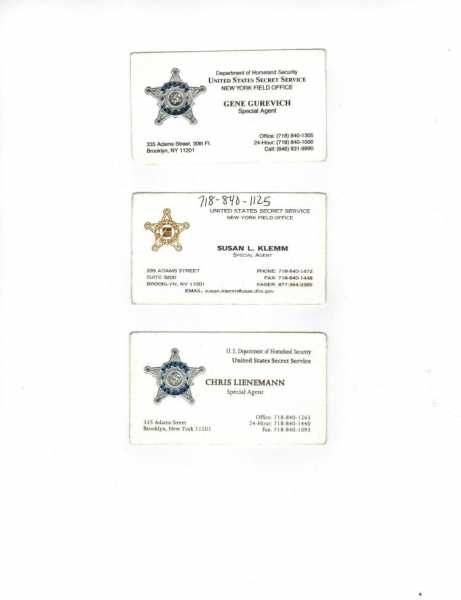
I can imagine how angry Putin was when Naryshkin showed him my letter – he had no doubt that Hillary Clinton, his personal enemy, was behind the Secret Service planned murder.
FSB answered me fast:
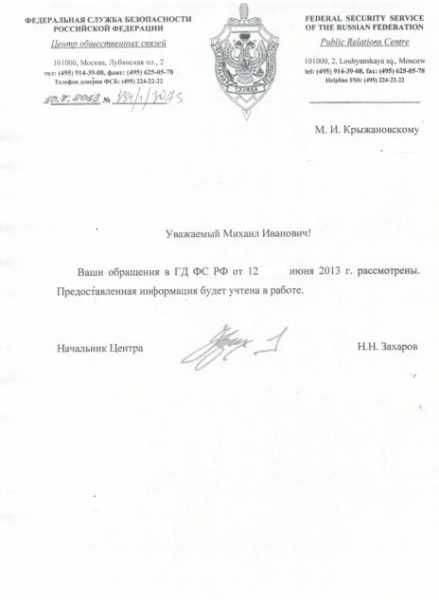
October 3, 2013
Federal Security Service of the Russian Federation
101100, 2 Lubyanskaya sq, Moscow
Dear Mikhail Ivanovich,
We received and looked into your letter to the Duma. We'll use the information you've provided.
N. N. Zakharov, Chief, Center of Public Relations
Remember FSB (a former KGB) have very well trained killers – I was a member (a sniper) of KGB "Nabat" anti-terror team and I know very well how they work. If Putin orders to kill Hillary Clinton, they'll do it no matter what.
Putin got my letter and answered fast, because Hillary Clinton was his personal enemy since 2008 presidential campaign when she said:" He [Putin] was a KGB agent. By definition he doesn’t have a soul, " He got very angry and punched her back saying that at a minimum, she should have a head, "
Besides, Putin knows me in person as the author of the White House Special Handbook and Espionage Handbook, and that's why took my warning very seriously.
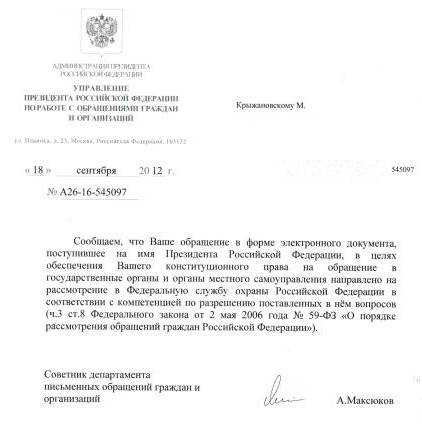
From: President of The Russian Federation
Executive Office
Directorate for Communication
Ilinka str, 23/16, Moscow
September 18, 2012
#A26-16-545097
To. M. Kryzhanovsky
We inform you the letter to you've sent via e-form was received by the President.
The letter has been sent to the Federal Protective Service.
A. Maksukov
Adviser, Directorate of Communication
Attention.
The Federal Protective Service (FSO) is a federal government agency concerned with the tasks related to the protection of several, mandated by the relevant law, high-ranking state officials, including the President of Russia, as well as certain federal properties. FSO includes the Russian Presidential Security Service. The FSO has roughly 50, 000 uniformed personnel plus several thousand plainclothed personnel and controls the Cheget that can be used in the event of global nuclear war.
It also operates a secure communications system for senior government officials. The FSO is a powerful institution with a range of rights and powers, including the right to conduct searches and surveillance without warrants, make arrests, and give orders to other state agencies.
FSO includes Special Communications and Information Service of Russia (Spetsviaz or SCID).
It is is a cryptologic intelligence agency of Russia responsible for the collection and analysis of foreign communications and foreign signals intelligence, as well as protecting Russian government communications and information systems, which involves information security and cryptanalysis/cryptography. It is the equivalent to the United States National Security Agency.
Putin appointed these two chiefs to be in charge of the "Hillary-2016" Project.

Dmitriy Kochnev, FSO Director

Alexey Mironov, the Special Communications and Information Director
Kochnev prepared the "Hillary" Project plan to be signed by Putin and executed by Mironov.
According to this plan SCID :
1. Had penetrated the servers of the Democratic National Committee and Debbie Wasserman Schultz, the DNC chair, Clinton campaign chairman John Podesta in person, whose private emails were published by WikiLeaks in the days leading up to the Democratic convention. Putin called the hacking and release of nearly 20, 000 emails from the DNC "a public service". The e-mails the DNC's favoritism of Hillary Clinton over Bernie Sanders published by Wikileaks compromised Dems' leaders and Hillary too.
2. Hacked Hillary Clinton's personal phone and computer. All information was transferred straight to Trump who got the possibility to correct his strategy. And leaked to the public.
3. Hacked the 2016 elections.
How?
First, the attackers probed election offices well in advance in order to find ways to break into their computers. Second, closer to the election, when it was clear from polling data which states would have close electoral margins, the attackers spreaded malware into voting machines in some of the states, rigging the machines to shift a few percent of the vote.
Episode 6. $50, 000 for me to remove Obama
The story starts with Jerry Corsi, an American author, WorldNetDaily political commentator best known for his New York Times bestselling books The Obama Nation, Unfit for Command and Where's Birth Certificate, personal Obama's enemy. He investigated Obama's life in details and proved that the president wasn't born in USA and his presidency is illegal.
The WorldNetDaily (WND) is a very popular and influential radical Conservative website which supported Donald Trump's very aggressive anti-Obama campaign to remove him from the office as a fake US citizen.
April 12, 2012, Queens, S. Richmond Hill, New York

Jerry Corsi came to see me (he lives in New Jersey) after we communicated for couple of days via e-mail about our anti-Obama investigations – read my full version of Obama's real biography below.
Corsi brought me his book "Where's Birth Certificate" and gave it to me for "my courage". We talked three hours at the nearest café. He was impressed by my experience as a spy and KGB sniper. We made arrangements for the next meeting and Corsi promised me some big and important job.
May 20, 2012, same place
Corsi brought a simple anti-Obama conspiracy plan. A big fake.
I had to go back to Russia and find 2 former KGB officers who allegedly knew that Obama was working for KGB intelligence. These officers had to write down personal statements and didn't have to sign them with their legal names. I come back with the papers and "anonymous sponsor" pays me through Corsi $50, 000. Sponsor wants to remove Obama from the Oval Office.
Anonymous rich sponsor paying cash.
Trump.
Money was big, but there was a problem. CIA was watching me on the daily basis and I could never leave USA alive for this conspiracy trip.
Corsi was angry – I understood him. if Trump pays me $50, 000, WND guys and Corsi could get a million.
I said "No". I can imagine how angry Trump was.
Now I have a question for president-elect Trump.
Corsi asked me how good I am as a sniper. Mr. Trump, you still want me to kill Obama?
JAMES B. COMEY
FBI Director
601 4th Street NW, Washington, DC 20535
(202) 278-2000
November 14, 2016
Dear Mr. Comey,
I've been working for CIA and FBI since 1995, and you know me as "Filament".
I'm ready to cooperate with you on Donald Trump's attempted Barack Obama's murder.
Mikhail Kryzhanovsky (CIA and FBI "Filament")
November 14, 2016, WND
by Jerome Corsi
WND AUTHOR RECOMMENDED FOR JOB IN TRUMP ADMINISTRATION
Could fill 1 of 2 key positions for president-elect.
A supporter of Donald Trump from early in his candidacy, WND author and Oxford professor, an American citizen by birth, Theodore Malloch is being referred to the Trump transition team as a candidate for either ambassador to the United Nations or to the United Kingdom.
OBAMA IS KGB INTELLIGENCE OFFICER
(full version of Obama's real biography by M. Kryzhanovsky)

Documentation
August 4, 1961
Barack Obama was born in Honolulu, Hawaii.
If there's something very wrong with someone's birth certificate.
If there's an indication that this someone used a birth certificate of a newborn child (Virginia Sunahara) who died at birth or soon after birth.
If this someone is the U. S. President.
We have to talk about Russian intelligence (SVR, a former KGB) and its illegal espionage department. We have to talk about the illegal spy "documentation process" – using birth certificates to get legal documents in USA – SS#, driver license, passport.
“Obama” showed his "real" birth certificate in 2011. A single reporter – NBC Savannah Guthrie – was allowed to see the “real” document, and then it was scanned as a PDF file and loaded into the Internet. Numerous electronic document experts have shown, using steps that anyone can repeat with if they have the proper software, that the document the White House uploaded is not simply a scanned version of an original paper document. Instead, it’s what’s called a “layered” document. A document that’s scanned will have only one layer, which is the image itself. A “layered, ” electronically manipulated document will show one electronic addition after another. The White House’s birth certificate PDF has 9 layers. This was an assembled electronic document, not a scanned paper document.
KGB is here.
Transformation

Barack Obama in 1971, age 10 and in 2001, age 40 – face aged on in20years. com

"Barack Obama" in 2001
Illegal spy cover story works best if it's a mix of actual and fake facts. "Obama" (let's call him John Smith) was a child of a student from Kenya who studied in Moscow and dated a Russian girl. Such kids in Russia were often unwanted by both partners and were raised and educated at a special school. Like Obama, John Smith was born in 1961 and, like him, graduated from high school in 1979. KGB paid attention to a very smart young man, and he joined the organization. Smith was Intelligence Institute student in 1979-1981 in Moscow, not far from "Cosmos" Hotel. There are couple of buildings in the area and I got intelligence education myself in one of them back in 1987 (15 Yaroslavskaya Street, Moscow Russia).
Then a decision was made to train him individually as illegal intelligence officer. The "dacha" (Russian for small villa) not far from Moscow, provides an ideally isolated territory for training. 2-3 instructors live there to immerse the candidate completely into his American identity and supervise him all the time. From the first day the candidate becomes accustomed to the circumstances in which he will be living and working in USA for many years. He wears American clothes, eats the food, he's thinking, acting and living like 100% American. He’s supplied with newspapers and magazines, he's watching movies and TV shows. The instructors communicates with him non-stop, from 6 AM to 10 PM. After a number of years of such training, the future illegal spy knows everything about America, espionage technology and speaks perfect English (by the way, "Obama" once made a very interesting mistake – he said "leave the Agency" instead of "lead the Agency. In espionage business, we say :" One mistake in pronunciation, and the enemy will finish your sentence with a lead dot".
After special training candidate goes through “abroad transformation” process :
a) illegal probation period abroad. A trip abroad through intermediate countries with numerous changes of passports and cover stories, jobs, personal connections. Finally, he gets to the target country, stays there for another 1-2 years and goes back to his country for additional training and correction of the cover story – actually, it's his first combat assignment. The most important part of this assignment is to check the reliability of the cover story and documents; the cover story has to be reinforced with new and old true facts, like short-term studies at universities or professional training courses.
b) intermediate legislation. On his way back to Russia the officer could stay in an intermediate country for another 1-2 years, make contacts with business, scientists, government employees, celebrities.
c) basic legislation. Officer comes to the target country, obtains genuine documents, gets a job which allows him to travel and talk to many people, recruit informants thus creating an illegal station.
At the same time, in 1979-1981, Barack Obama studied at Occidental College in Los Angeles where he became a socialist ready to transform the nation by redistributing wealth. KGB station in Washington, DC which was constantly looking for future secret sources at American top universities and colleges, like Columbia, Yale or Harvard, got information about young socialist. They sent his picture and info to Moscow where some resemblance was discovered between a college student from Los Angeles and a future illegal spy John Smith.
What happened next?
1981
Obama traveled to Indonesia to visit his mother and sister Maya, and visited the families of college friends in India and Pakistan for 3 weeks. India was a good friend to Soviet Union and a perfect place to recruit foreigners. He was recruited and he disappeared.
“Obama” was secretly brought to India and from 1981 he’s playing Barack Obama. Then he stayed in Pakistan at Lahore Hilton International, was introduced to Yousa Gillani, the Central Working Committee of the Pakistan Muslim League (PML) member and the future prime minister – and went bird-hunting with him.
That's exactly what illegal spy had to do – make business and political contacts on his way to the target country. John Smith aka Barack Obama came back to the United States – change of agents, a regular illegal espionage method.
Obama's father, Barack Obama Sr., aged 46 died in a car accident in Nairobi. His mother, Ann Dunham, lived in Indonesia and might be just avoided or ignored by her "son" (Don Johnson, Dunham co-worker, said "Obama was distancing himself from her"). Russians approached her under a "false flag" ( National Security Agency or CIA) and explained that her son had to stay abroad for a secret mission for some time. They told her that she had to be ready to accept another person as her own son. For operation like that, espionage agencies often recruit close relatives and allow them to meet their son (daughter) from time to time outside USA. Money talks, there's nothing unusual, but Dunham wanted his son back and in 1995 KGB helped her to die of cancer at the age of 52.
Time changes people, so "Obama" had to stay away from his friends and do not show up in public too much.
1981-1983. He transferred to Columbia University in New York City, where he majored in political science and where nobody could remember him at all, and graduated with a B. A. in 1983.
"Obama" declined repeated requests to talk about his New York years, release his Columbia transcript or identify a single fellow student, co-worker, roommate or friend from those years. Wall Street Journal editorial in September 2008, titled "Obama's Lost Years" noted that Fox News contacted 400 Obama's classmates at Columbia and found no one who even remembered him. "Mostly, my years at Columbia were an intense period of study, " Obama told Columbia College Today in a 2005 alumnus interview. "I didn't socialize that much. I was like a monk".
Perfect cover up! Columbia has refused to release any records regarding Obama's attendance, including his application to attend, his grades, and his financial aid records, if any exist. Only one person could order Columbia to shut up – CIA Director Leon Panetta, a former Bill Clinton’s
Chief of Staff, by the way.
1983-1985
He worked at the Business International Corporation and at the New York Public Interest Research Group. He worked in Chicago as community organizer in 1985-1988.
1987
Moscow, 1987
I have a perfect memory and I state that I saw the man in the center of this picture in Moscow in 1987, where I’ve been trained at KGB Intelligence Institute.

“Zolotoi Kolos” Hotel, Yaroslavskaya Street 15, Moscow, a secret PGU KGB Intelligence Institute facility. If you open the Moscow hotels catalog, you’ll see that this hotel has 5 buildings – 1, 3, 4, 5, 7, 8 – buildings 2 and 6 “do not exist”.
Nearby I saw the man who looked like the person in the center of the picture above in January 1987.
I left a small note about that on Internet and on October, 13, 2011 a statement appeared on Internet: Paul Pieniezny :”The Obama who was in Russia at that time [1987 – M. K. ] was not Barack Obama, but a student from Western Africa. He is still alive and well and a diplomat. I have mentioned that little fact a few times on the Fogbow. I hope he sues Mr Kryzhanovsky for every cent he earned in the extreme-right talk circuit”. Looks like Obama and his KGB bosses are really scared.
1988 – 2008
“Obama” travelled to Europe to meet his KGB handlers and get new instructions. He had a choice – a safe variant (to make a political career in one of African countries), and a risky one of staying in America – KGB wanted him to be Martin Luther King #2. But it appeared he could get much more which was Oval Office.
KGB made a decision : he had to stay in USA longer and it was a success : KGB financed his successful Illinois Senator election (1997-2004) and – very important step on the road to the White House – U. S. Senator election (2005-2008).
Bill left the Oval Office in 2001 and KGB had to substitute him for another asset, as they couldn’t recruit George Bush Jr..
Ask Lugar
August 5-7, 2005, Perm, Russia

Senators Lugar and “Obama”, Russia
"Obama" visited Russia (together with Senator R. Lugar) and met secretly his SVR (former KGB intelligence) handlers to discuss his perspectives for the U. S. presidency. It appeared that U. S. Senator “Obama” was getting out of control and Russians decided to teach him a lesson. Here’s what happened.
Senator Richard Lugar, an Indiana Republican and Chairman of the Senate Foreign Relations Committee, and Senator “Obama”, an Illinois Democrat, were detained for three hours on August 7 at an airport in Russia's city of Perm. "We are not certain as to why the particular activity caused that delay, " Lugar said. He said U. S. Embassy officials informed the senators that "an official at the Foreign Ministry has issued an apology. "
No one from the Russian Foreign Ministry could be reached. The U. S Embassy could not immediately confirm the information. Russia's Federal Security Service, however, defended the plane's delay, saying it was because the Perm airport isn't part of an Open Skies Agreement, which allows certain planes to bypass inspections. The FSB, the agency that succeeded the KGB, said it could only comment on the report within a week's time. Maksim Zhalayev, deputy head of the border control service at Perm’s airport, accused the senators of refusing to follow border guards’ orders, telling Russia’s Ekho Moskvy radio that was the reason behind the delay. U. S. Embassy officials said the flight was a U. S. military flight, and therefore should have had diplomatic status. Lugar's spokesman, Andy Fisher, said that Russian officials had initially refused to allow the plane to take off, and insisted on boarding it. "They did not. The border patrol finally got orders to let us go, " Fisher said. The senators and their aides spent three days in Russia visiting sites where warheads are stored before destruction under the U. S. -funded Comprehensive Threat Reduction program.
This international scandal could never happen without President Putin’s straight order. “Obama” got the message.
KGB Pelosi
August 28, 2008
KGB paid big to Nancy Pelosi, the House Speaker, and asked her to help “Obama” win the Democratic nomination. They informed her that “Obama” was not eligible under the US Constitution and she has to change the Nomination Certification.
Pelosi was smart enough to understand that if KGB pushed “Obama” to the very top of political power, they had enough money and possibilities to erase her in case she refused. And the money was big.
Now, look at the evidence.
Original document.

Democratic National Committee
Official Certification of Nomination
This is to certify that National Convention of Democratic Party of the United States of America, held in Denver, Colorado on August 25 through 28, 2008, the following were duly nominated as candidates of said Party as President and Vice President of the United States respectively and the following candidates for President and Vice President of the United States are legally qualified to serve under the provision of the United States Constitution:
For President of the United States
Barack Obama
For Vice President
Joe Biden
Signed by :
Nancy Pelosi, Chair, Democratic National Convention
Alice Travis Germond, Secretary, Democratic National Convention
Notary Public
August 28, 2008
And now look how Pelosi earned the KGB money and forged the document :

Democratic National Committee
Official Certification of Nomination
This is to certify that at the National Convention of the Democratic Party of the United States of America, held in Denver, Colorado on August 25 through 28, 2008 the following were duly nominated as candidates of said Party as President and Vice President of the United States respectively.
For President of the United States
Barack Obama
For Vice President of the United States
Joe Biden
Signed by:
Nancy Pelosi, Chair, Democratic National Convention
Alice Travis Germond, Secretary, Democratic National Convention
Notary Public
August 28, 2008
Got it?
KGB asset Nancy Pelosi deleted “…are legally qualified to serve under the provision of the United States Constitution…”
Perfect job, Nancy.
And a perfect federal crime.
Variant 1
Variant 2 – official document
KGB psychotechnologies
Igor Smirnov (1950-2004) was a Psychotechnology Research Institute (Moscow) Director, professor, the father of "psychotronic weapons, " the Russian term for mind control weapons. His father, Victor Abakumov, was KGB Chief in 1946-1951. The Institute was established first as KGB psychotechnology lab by KGB Chairman Y. Andropov in 1980.
His research was focused on a unique "psycho-correction" technology – the use of coded acoustic subliminal messages transmitted in "white noise" or music to bend a subject's will, and modify a person's personality without their knowledge. Using an infrasound very low frequency-type transmission, the acoustic psycho-correction message is transmitted via bone conduction – ear plugs would not restrict the message.
Messages like "Vote for Obama! " might be sent through a mobile phone, radio, TV or PC – you don't hear them but your brain accepts them. In a same way the brain accepts the visual image. They by-pass the conscious level and are effective almost immediately.
Janet Morris is President and CEO of M2 Technologies Corp, specializing in non-lethal weapons (NLW), novel technology applications, tactics and technology. Ms. Morris's seminal non-lethal concept and novel technology applications work has been used by the White House Office of Science and Technology Policy. She served at the United States Global Strategy Council (1989-1994) and at the Center for Strategic and International Studies (1993–1995).
In 1991 Morris met Smirnov who showed her his “Mind Reader”. In 1993 Smirnov came to Washington, DC and showed his technology to Bill Clinton’s people, Pentagon and CIA experts. In March, 1993 the Richmond, Virginia based Psychotechnologies Corp signed an agreement with Smirnov in which "the Russian side agreed to commit the psycho-correction technologies still in Russia and all related know-how to the US. company in exchange for stock. The Russian side has agreed to provide all support necessary to recreate current [psycho- correction] capability in the US and to upgrade the capability using US components and computer programmers. All necessary developmental and existing algorithms will be provided by the Russian side. "
In 2008 Barack Obama won presidential elections and it was a national psychosis combined with euphoria.
Many out of 69, 5 million Obama’s voters can’t explain what happened to them and what “CHANGE! ” they wanted.
Watch the microphone!
OBAMA- RUSSIAN PRESIDENT MEDVEDEV SECRET TALK DECODED by Mikhail Kryzhanovsky
Seoul, March 26, 2012
The secret deals.
"On these issues, but particularly missile defense, this can be solved, but it's important for him [Putin] to give me space". Barack Obama.
Explanation.
1) "... these issues can be solved".
Obama promised that America won't start war in Iran in 2012 and, for sure, it won't happen after Obama is re-elected. Obama and Medvedev reached a secret deal on Iranian nuclear program, because Obama didn't even mention it, it's a minor problem now.
2) "... particularly missile defense... this can be solved"
Obama and Medvedev already reached a secret deal on American missile defense in Europe – Obama will put it on hold until 2016, for the period of his future second term.
3) "It's important for him [Putin, Prime Minister] to give me space"
Obama didn't mention Putin's name and that means that secret deals in Seoul were initiated by Putin, not Medvedev. Obama is begging Putin to "give him space" and that means Putin is pressing Obama hard as his asset.
Dmitriy Medvedev: "Yes, I understand. I understand your message about space. Space for you... "
Explanation.
Medvedev didn't promise to stop pressure, he promised "understanding".
That means: "We understand you can't be weak on this issues now. But Putin wants to start his new presidency with international victory – missile defense in Europe is a threat to Russia and it has to be removed".
Barack Obama:"This is my last election. After my election I have more flexibility".
Explanation.
Obama is 100% sure he's re-elected and that means Obama and Medvedev reached a secret deal on Obama's 2012 campaign financing.
"After my election I have more flexibility" means "If Russian intelligence could finance my campaign properly, I'll get the second term and you'll get whatever you want, but not before".
Dmitriy Medvedev:"I understand. I will transmit this information to Vladimir [Putin] and I stand with you".
Explanation.
1) Again, Medvedev promised "understanding" and that means that Putin will make ultimate decision on Obama's campaign financing.
2) "Transmit", "transmitter" is espionage technical jargon. Medvedev would never use it if it was a regular meeting of two presidents. He would rather say "I'll inform Putin on that"
KGB kills USA
1. Socialist intervention into the US economy.
A person who wants to spend $1 trillion on health care reform which is not a priority at all in the middle of horrible economic crisis, in a country with $ 17 trillion national debt is either an idiot or an enemy of America with a very well calculated plan to terminate the country. “Obama” did it – in March 2010 he signed Health Care Reform legislation into law.
1. Socialist intervention into American society.
“Obama” is planning an explosive immigration reform which is the KGB order.
He is ready to turn 12 million poor illegal Latinos into US citizens-revolutionaries. In 2016 they'll get green cards, by 2020 they'll get citizenship and bring here all their family members – around 50-60 million unemployed poorly educated people. And that will be the death of America, the end of American Constitution and the birth of a totalitarian "Obama” or any other KGB appointed U. S. President – forever " Communist regime.
2. “Boiling point” strategy
Rising unemployment and inflation, budget deficits all over the country is another Obama's trick, planned by KGB. “Obama” is pushing big states like Texas, New York and California to a "boiling point" after which they might take serious steps towards independence. USSR collapsed the same way – now Putin wants revenge using “Obama” as a hammer.
3. KGB ordered “Obama” to insert a small trick into the U. S. National Security Strategy :
“Analysts, agents and officers who protect us must have access to all relevant intelligence throughout the government”.
A very dangerous trick – just imagine Russian recruit a “mole” with access to all relevant information.
I call this a “hologram technology”.
Russian “mole”, who’s working for CIA as, say, nuclear proliferation analyst, has access to “all relevant information” throughout US intelligence community: Air Force Intelligence, Army Intelligence, Central Intelligence Agency, Coast Guard Intelligence, Defense Intelligence Agency, Department of Energy, Department of Homeland Security, Department of State Bureau of Intelligence and Research, Department of the Treasury, Drug Enforcement Administration, Federal Bureau of Investigation, Marine Corps Intelligence, National Geospatial-Intelligence Agency, National Reconnaissance Office, National Security Agency Navy Intelligence, Office of Director of National Intelligence
Do you understand what that means? I’ll explain. The White House is sending requests for information or research on a certain political or economic problem, situation in Europe, Asia, etc. A “mole’ is sending those request to Moscow and Russians calculate the US strategy, understand? Besides, “mole” is stealing information from all above mentioned agencies.
We have to stop it today – just for that deadly blow to American national security Obama has to go to jail as the enemy of state.
Russia’s Savior
Russia has the world's largest reserves of mineral and energy resources, the world's largest forest reserves and 25% of the world's fresh water. Russia is energy superpower : #1 in the world in natural gas reserves, #8 in oil reserves and #2 in coal reserves.
The sources of energy (oil, gas, uranium, coal) are rapidly coming to an end. At the same time China, India, Brazil, Indonesia are rapidly growing.
We have 9 billion people on Earth with energy, food and fresh water supplies coming to an end in the next 25-40 years. That means that 500 million Europeans and 300 million Americans have to lower their standards of living – and they will not accept this! On top of it we have the global financial and economic crisis which is actually killing America.
The only way out – to capture resources that still remain to preserve our standards of living.
The World War III is coming – the war between USA and Russia. Actually, civil war in Ukraine, the closest Russia’s neighbor and partner is a huge threat for Russia as USA and NATO support the nationalist regime. Kremlin supports the pro-Russian rebels.
Russian leader Putin will do everything and will pay anything to postpone the war as long as possible.
Episode 7. What Putin has on Bill Clinton
RECRUITMENT

Bill, 1974
December 31, 1969, Moscow, Russia
“Very poor” Oxford student and anti- Vietnam war activist Bill Clinton came to Moscow through Holland, Denmark, Norway, Sweden, and Finland for 5-day vacation at super expensive "National" Hotel, a place for rich who come to Russia on big business. Who paid for European tour and the “National”, Bill? OK.
The only person Bill knew in Moscow was Anik “Nikki” Alexis, a daughter of a French diplomat. Clinton recalls in his 2004 “My life” autobiography, "One night I took a bus out to Lumumba University to have dinner with Nikki". On the bus back home, Clinton says, there was only one other passenger, Oleg Rakito, who "spoke better English than I did" and "asked me lots of questions and told me he worked for the government, virtually admitting he was assigned to keep an eye on me".
Bill’s story is a total lie.
First, foreigners who can afford "National" don't use public transportation on -30 C Russian winter night. Second, KGB officer might break his identity to a foreigner if he's recruiting him only. Third, Bill was successfully recruited by KGB, otherwise he would have left Moscow immediately and in panic. Instead, he enjoyed the rest of his vacation and went to Czechoslovakia, another socialist country. In 1969 Bill was 23, perfect age for KGB – they recruited young foreigners (students of Yale, Harvard, Columbia, Oxford) between ages 21-26 because:
a) you brainwash them easier and faster than adults
b) you build their careers the way you want
c) these guys always have a chance to occupy the Oval Office one day
How KGB recruited Bill
KGB intelligence officer under diplomatic cover met an anti-war activist Bill in Oxford, brainwashed him and gave him a gift – paid Christmas Europe-Russia tour. He also said that his friend in Moscow would like to talk to Bill and make some deal. In Moscow Bill met Oleg Rakito at “National” and signed the recruitment paper. Rakito promised him fast political career – Governor and then the U. S. President. Bill made a choice and the choice was right as we all know.
Bilderberg
June, 1992, Baden-Baden, Germany
In the middle of his first presidential campaign Arkansas Governor Bill Clinton made a 3-days secret trip to Baden-Baden, Germany where he attended the annual Bilderberg Club meeting. Media went crazy as the Democratic candidate completely disappeared from view for 72 hours.
But for Bill and Godmother it was the most important meeting in their lives as there were two people who had the power to appoint American President – David Rockefeller, CEO – Chase Manhattan Bank and Henry Kissinger, the informal Bilderberg chair, who’s serving Rockefeller clan, the most powerful family in USA, for many years.
Rockefeller and Kissinger liked Bill Clinton and he was elected the next U. S. President.
SUPERJOB

1997
Russia, totalitarian, 100% corrupted country with dying economy and dictator Boris Yeltsin ("Czar Boris") on top, joined the G7, a group of seven major industrialized democracies. It was KGB agent Bill Clinton’s huge effort to shut up Canada, Great Britain, France, Italy, Germany and Japan who unanimously opposed the G7 “reform”. Good job, Billy.
HOW KGB PAID HIM
In 1993 Vice President Gore and Russian Prime Minister Chernomyrdin signed a 20-year $12 billion deal under which Russia would ship its weapons-grade uranium to the United States. Bill in his over 1, 000-page memoir My Life (2004) wrote actually nothing about this “deal of a century. ” Look,
“In the afternoon [April, 3, 1993] we [Clinton and Russian President Yeltsin] agreed on a way to institutionalize cooperation, with a commission headed by Gore and Chernomyrdin…. On January 30 [1996], Prime Minister Chernomyrdin of Russia came to the White House for his sixth meeting with Al Gore. After they finished their commission business, Chernomyrdin came to see me to brief me on events in Russia and Yeltsin’s prospects for reelection” [p. 697].
You’ll never make Bill Clinton talk about the deal again even at gun point. Why?
At their summit meeting in Vancouver, in April 1993, President Clinton and President Yeltsin created the U. S. – Russian Joint Commission on Economic and Technological Cooperation. Since then it has become known as the Gore–Chernomyrdin Commission (GCC). The Commission’s original mandate was to support cooperation between the United States and Russia in the areas of space, energy and high technology.
In fact it was a cover-up of two thieves to mask a non-proliferation agreement to convert highly enriched uranium (HEU) taken from dismantled Russian nuclear warheads into low-enriched uranium (LEU) fuel to be sold to customers in the USA and worldwide through the USEC (United States Enrichment Company). USEC was created in 1993 as a government corporation with the mission to restructure the US government’s uranium enrichment operation and to prepare it for sale to the private sector.
Attention!
On April 26, 1996 Bill signed into law the USEC Privatization Act. The HEU Agreement required the United States to purchase through USEC 500 metric tons, $12 billion worth, of HEU. The money disappeared. Most of the documents are still classified.
KGB KILLED 3 RUSSIANS TO COVER HIM UP
Three Russian statesmen tried to investigate the Clinton- Yeltsin deal :Ruvim Nureyev, Lev Rokhlin, Yuri Shchekotchikhin. All of them are dead.
1. Ruvim Nureyev. The Russia Chief Inspector for Nuclear and Radiation Safety, who strongly opposed the deal, was found dead on the railroad tracks in June 1996. The incident was described as a suicide.
2. Lev Rokhlin. The Russian State Duma Deputy Lieutenant General Rokhlin started his own official Clinton-Yeltsin deal investigation. Lev Maximov, the Nuclear Technologies Institute Director, who helped Rokhlin to obtain the documents, received death threats.

July 3, 1998, Moscow, Russia
Rokhlin was shot three times and killed in his house while he was sleeping. His wife, Tamara Rokhlina, was arrested and testified that she killed him “for reasons of personal enmity. ” She later recanted her testimony, saying she incriminated herself under threat. Rokhlin’s bodyguard, who was there that night, testified that he heard no gunshots (the killers used a silencer). Within days three dead bodies were found in the vicinity of the Rokhlin household and cremated before they could be identified. In November 2000, Rokhlina was convicted of murder and sentenced to 8 years in prison, but the Supreme Court overturned the verdict and ordered a new trial.
October 2, 1998, Washington, DC
The US Congress, taking into account that Lev Rokhlin was a former Russian State Duma Defense Committee Chairman, asked Bill to “urge the Russia Government to promptly and thoroughly investigate” the case. Billy was smart enough not to dig his own grave, and just ignored this
Resolution
Expressing sympathy to the family and collegues of Lev YakovlevichRokhlin, and expressing the sense of the House of Representatives that President of the United States should urge the Russia Government to promptly and thoroughly investigate the circumstances surrounding the death of Lev Rokhlin and to provide a full accounting of the circumstances no later than November 1999.
Whereas Lev Rokhlin assumed the chairmanship of the Defense Committee of the Duma and was the highest-ranking elected official in the Duma working on Defense issues…Wheras in October 1997, Lev Rokhlin advocated the resignation of President Yeltsyn. Whereas attempts were made for 6 months to remove Lev Rokhlin from his Committee chairmanship. Whereas on July 3, 1998, Lev Rokhlin was stripped of the chairmanship of the Defense Committee, but maintained his position as a member of Duma. Whereas on July 3, 1998, Lev Rokhlin was shot in the head three times and killed. Whereas members of Lev Rokhlin’s family have stated that Rokhlin’s wife, Tamara Rokhlina, was physically abused and was threatened with death unless she accepted responsibility for Lev Rokhlin’s murder. Whereas Lev Rokhlin’s bodyguard, who was in the home the night of the murder, claimed that he heard no gunshots. Whereas three bodies were cremated by the Moscow government authorities before they could be identified. Whereas any inability of Russia to provide a full accounting of the circumstances surrounding the death of Lev Rokhlin would raise serious questions about the existence of a stable democratic system in Russia:
Now, therefore, be it
Resolved, That –
(1)The House of Representatives expresses sympathy to the family and collegues of Lev Rokhlinand :
(2)it is the sense of the House of Representatives that the President of the United States should urge the Russian Government –
(A) to promptly and thoroughly investigate the circumstances surrounding the death of Lev Rokhlin;
(B) to provide a full accounting of circumstances not later than November, 1999
Kremlin did nothing.
3. Yuri Shchekotchikhin, a famous Russian reporter and corruption fighter, was elected to the Russian State Duma where he served as National Security Committee Deputy.

After Rokhlin was murdered in 1998, Shchekotchikhin continued his investigation and concentrated his efforts in two directions: first, he tried to obtain the #1 Gore–Chernomyrdin Agreement (September 2, 1993), but President Yeltsin denied the requests. Second, he started a full-scale investigation into the Atomic Ministry corruption and – against Atomic Minister Adamov in person. On June 16, 2003, he lost consciousness and was taken to the Central (Kremlin) Hospital. He was pronounced dead after lying still unconscious for 12 days. (The official diagnosis – a flu). All medical records are still classified, but experts insist he was poisoned by thallium or cadmium.
KGB KILLED 31 AMERICANS WHO KNEW TOO MUCH
(AND IN ESPIONAGE THAT MEANS "WHO TALKED TOO MUCH")
1. James McDougal. He died on Sunday, March 8, 1998 in John Petersmith Hospital in Ft. Worth, Texas. He had been serving a federal prison sentence for fraud in connection with the Whitewater land deal. At first, he claimed to be innocent, but after being convicted of 18 felony counts, he cooperated with Special Prosecutor Kenneth Starr's investigation of the Clintons. He was scheduled to give damaging testimony against the Clintons, although critics of the investigation say his testimony had previously been inconsistent and that nothing new was expected to be revealed. A prison spokesman said McDougal died of a heart attack and had been suffering from heart disease and blocked arteries.
2. Mary Mahoney. A former White House intern was murdered July 1997 at a Starbucks Coffee Shop in Georgetown. The murder happened just after she was to go public with her story of sexual harassment in the White House. Mahoney was murdered over the July 4th weekend in 1997 at the Georgetown Starbucks near Washington D. C.. She was the assistant manager and, according to published reports, she and two other employees were working late at night after the coffee bar had closed. All three were found shot to death. No money was taken and there was no sign of forced entry
3. Vince Foster. A former White House counselor, and colleague of Hillary Clinton at Little Rock's Rose Law firm. Died of a gunshot wound to the head, ruled a suicide. Foster was Deputy White House Counsel and the Clinton's lawyer. He was found dead in Fort Marcy Park on July 20, 1993. Three investigations into Foster's death, including one by Independent Counsel Kenneth Starr, have concluded that the death was a suicide.
4. C. Victor Raiser II and Montgomery Raiser. Major players in the Clinton fund raising organization died in a private plane crash in July1992. On July 30, 1992, Victor and Montgomery Raiser were killed in a plane crash while on a fishing trip in Alaska
5. Paul Tulley. A former Democratic National Committee Political Director was found dead in a hotel room in Little Rock, in September 1992. Described by Clinton as a "Dear friend and trusted advisor". Tulley was a top strategist for the Democrats and working with the Clinton campaign. He died of massive heart failure in a Little Rock motel room. 6. Ed Willey. Clinton’s fund raiser, found dead in November 1993 deep in the woods in VA of a gunshot wound to the head. Ruled a suicide. Ed Willey died on the same day his wife Kathleen Willey claimed Bill Clinton groped her in the Oval Office in the White House. According to published reports, Ed Willey was an attorney who owed the IRS $400, 000 and had embezzled nearly $270, 000 from one of his clients. The Willey's financial woes were a source of stress between Ed Willey and Kathleen Willey and she finally demanded a plan that would bring it to an end. There was a stormy family meeting about it on the night of November 28, 1993 and Ed Willey moved out of the house. The next day is when Kathleen Willey went to the White House to see Bill Clinton about a job. She says the president assaulted her during that visit. It was later discovered that Ed Willey had driven into the woods on the same day. His body was found by hunters on November 30, 1993. Authorities ruled his death a suicide by shotgun. There was a suicide note apologizing for the financial problems.
7. Jerry Parks. Head of Clinton's gubernatorial security team in Little Rock. Gunned down in his car at a deserted intersection outside Little Rock. Park's son said his father had a dossier on Clinton. He allegedly threatened to reveal this information. After he died the files disappeared. Parks was the head of security for the Clinton-Gore Little Rock headquarters in 1992. On September 26, 1996, he was murdered down while driving through a Little Rock intersection. A lone gunman fired seven shots at him. This was two months after Vince Foster's death. Both Parks' wife and son have said that they believe Parks was murdered and that he feared for his life. His murder has never been solved. According to Gary Parks, Jerry Parks' son, the files were on the sexual escapades of Bill Clinton. They were not removed from Parks' house after his death. According to investigative reporter Christopher Ruddy, the files that Parks had been keeping on Clinton were taken during a burglary several weeks before Parks' death.
8. James Bunch. He died from a gunshot suicide. It was reported that he had a "Black Book" of people which contained names of influential people who visited prostitutes in Texas and Arkansas.
9. Bill Shelton. Arkansas State Trooper and fiancee of Kathy Ferguson. Critical of the suicide ruling of his fiancee, he was found dead in June, 1994 of a gunshot wound also ruled a suicide at the grave site of his fiancee. He was one of many of her friends who felt that Ferguson did not commit suicide and that the coroner's report was not accurate about her wound being self-inflicted. He was found a month later sprawled over her grave with a gunshot wound to his head that was similar to what the coroner had described as Ferguson's wound.
10. Gandy Baugh. Attorney for Clinton's friend Dan Lassater, died by jumping out a window of a tall building January, 1994. His client was a convicted drug distributor. The Truth: Gandy Baugh jumped out of a window of a multi-story building and died on January 8, 1994. Published reports say he was defending a man named Dan Lassater in a financial misconduct case. Lassater was an associate of Bill Clinton's who was convicted of cocaine distribution. 11. Suzanne Coleman. She had an affair with Bill when he was Arkansas Attorney General. Died of a gunshot wound to the back of the head, ruled a suicide. Was pregnant at the time of her death.
12. Paula Grober. Bill’s speech interpreter for the deaf from 1978 until her death December 9, 1992. She died in a one car accident.
13. Danny Casolaro. Investigative reporter. Investigating Mena Airport and Arkansas Development Finance Authority. Casolaro was found dead in the Sheraton hotel in Martinsburg, West Virginia on August 10, 1991. His wrists had been slashed. According to an October 14, 1991 People Magazine story on his death, he had warned friends and family that his life was in danger. Bill was governor at the time and there have been numerous questions about whether Bill was in any way involved in any of the activities connected with Mena or protected those who were involved.
14. Paul Wilcher. Attorney investigating corruption at Mena Airport with Casolaro and the 1980 "October Surprise" was found dead on a toilet June 22, 1993 in his Washington DC apartment. Had delivered a report to Janet Reno 3 weeks before his death. In his report to Attorney General Reno, Wilcher said that he was in grave danger and that if the information he had for the Attorney General fell into the wrong hands, there could be people "silenced in the very near future. "
15. Jon Parnell Walker. Whitewater investigator for Resolution TrustCorp. Jumped to his death from his Arlington, Virginia apartment balcony August15, 1993.
16. Barbara Wise. Commerce Department staffer. Worked closely with Ron Brown and John Huang. Cause of death unknown. Died November 29, 1996. Her bruised, nude body was found locked in her office at the Department of Commerce.
17. Barry Seal. Drug running pilot out of Mena Arkansas, death was no accident Johnny Lawhorn Jr. – Mechanic, found a check made out to Bill Clinton in the trunk of a car left at his repair shop. He was found dead after his car had hit a utility pole. He was a danger-loving pilot who was regarded as the best known cocaine smuggler of the 1980's. He did not die in a car accident. He was murdered in Baton Rouge, Louisiana in 1986 by three men with machine guns and who were later arrested and convicted. They were Colombians and authorities say they were connected with the Medellin drug cartel. The Attorney General of Louisiana told U. S. Attorney General Ed Meese in 1986 that Seal smuggled $3 to $5 billion worth of drugs into the U. S. In 1981, Seal began running his smuggling operation out of a highly guarded and, for a while, secret airport in Mena, Arkansas. That airport and Seal's activities were to become a part of the investigation into the Iran-Contra controversy from the Reagan administration. There have been questions of whether Bill Clinton, who was governor of Arkansas at the time, may have looked the other way if he knew about the drug smuggling operation, but there has not been proof of that.
18. Kevin Ives & Don Henry. "The boys on the track" case. Reports say the boys may have stumbled upon the Mena Arkansas airport drug operation. A controversial case, the initial report of death said, due to falling asleep on railroad tracks. Later reports claim the 2 boys had been slain before being placed on the tracks. Many linked to the case died before their testimony could come before a Grand Jury.
19. The following Clinton’s bodyguards are dead: Major William S. Barkley Jr., Captain Scott J. Reynolds, Sgt. Brian Hanley, Sgt. Tim Sabel Major, General William Robertson, Col. William Densberger, Col. Robert Kelly, Spec. Gary Rhodes, Steve Willis, Robert Williams, Conway LeBleu, ToddMcKeehan.
20. Ron Brown. Secretary of Commerce and former DNC Chairman. Reported to have died by impact in a plane crash. A pathologist close to the investigation reported that there was a hole in the top of Brown's skull resembling a gunshot wound. At the time of his death Brown was being investigated, and spoke publicly of his willingness to cut a deal with prosecutors.
21. James Bunch. Died from a gunshot suicide, he had a "Black Book" of people which contained names of influential people who visited prostitutes in Texas and Arkansas.
22. James Wilson. Found dead in May 1993 from an apparent hanging suicide. He was reported to have ties to Whitewater. 23. Florence Martin. Accountant & sub-contractor for the CIA, was related to the Barry Seal Mena Airport drug smuggling case. He died of three gunshot wounds.
24. Paula Grober – Clinton's speech interpreter for the deaf from 1978 until her death December 9, 1992. She died in a one car accident.
25. Judy Gibbs.

"Penthouse" model and а call girl Judy Gibbs, who appeared in the December 1979 issue of Penthouse, and her sister Sharon worked at а brothel in Fordyce, Arkansas, that also engaged in blackmail of its more powerful clients. Linked to Bill Clinton by both her own family and by one of Bill's bodyguards, Judy had just decided to cooperate with police in an investigation of Arkansas cocaine trafficking when she burned to death inside her home from a fire of undetermined origin.
26. Dr. Ronald Rogers. Dentist from Arkansas Killed in plane crash as he was on his way to an interview with a London Sunday Telegraph reporter to reveal information about Clinton scandals.
27. Johnny Lawhon. Died March 29, 1998 In the spring of 1997, a tornado ripped through some junked cars at Johnny's Transmission shop and opened up the trunk of a car that proved to have a box of Whitewater records in it, including a copy of a $27, 000 cashier's check drawn on Madison and payable to Bill Clinton. Lawhon realized what he was looking at and turned the box of documents over to the FBI. According to police, Lawhon and a friend hit a telephone pole at a high rate of speed after their car had become airborne and left the road. They had driven less than a quarter mile at the time of the impact.
28. Eric Butera. An informant who came forward offering information regarding the murder of White House intern Mary Mahoney. He was then sent into a known crack house to make an undercover buy for the police and was beaten to death.
29. Larry Lawrence. Ambassador to Switzerland nominee. Lawrence was a fundraiser, made famous by his burial at Arlington which revealed not only the special treatment given him but the depths of his legal troubles prior to his being nominated as ambassador to Switzerland. Less well known is that at the time of his death, allegedly from a heart attack, Larry Lawrence had just come under criminal investigation by the State Department and had (as had Ron Brown) indicated a willingness to cooperate.
30. Stanley Huggins. Investigated Madison Guarantee. His death was a purported suicide and his report was never released.
31. Hershell Friday. Attorney and Clinton fund raiser died March 1, 1994 when his plane exploded.
PART 2. WHY PUTIN WANT TO KILL HILLARY, OBAMA AND TRUMP


Best tools I used as KGB sniper – Stechkin, silenced, SVD rifle
INTRODUCTION
“Passive sabotage” technology
To kill Hillary Clinton, Barack Obama or Donald Trump I need three helpers: the U. S. Secret Service Director Alles, FBI Director McCabe, CIA Director Pompeo,.
They will help me in case I kill Clintons, Obama and Trump, because they want me back to work no matter what.


Why them?
Because I have to use a KGB "passive sabotage" technology.
Let me show you how it works.
August 5, 1962, Los Angeles, California
CIA agents killed Marilyn Monroe (staged suicide – "acute barbiturate poisoning") who got information on planned JFK assassination and desperately tried to contact him or his brother, Robert Kennedy. It’s simple to kill without any traces or in the body if you use a suppository.

November 22, 1963, Dallas, Texas
President John Kennedy was assassinated at 12:30 p. m. in Dealey Plaza, Dallas, Texas.

What's conspiracy?
It’s when you ask the government a simple question and nobody wants to answer it. And if you ask the wrong questions you get the wrong answers, as with the Warren Commission. Let’s ask some good questions.
Question 1. What would have happened if the snipers missed the target or Kennedy survived, being merely wounded – sniper is a human being – he makes mistakes?
Answer. Kennedy would have won the 1964 Presidential election and then conceivably his brothers, Robert and Edward, would keep the Oval Office until 1984 (count the years for yourself). No war in Vietnam. The CIA would have been shut down. The FBI and Pentagon would have been "cleaned up" and "cleaned out. "
Question 2. Why would the CIA, FBI and big business behind them, not to mention others who had their eye on the Oval Office, take such a huge risk?
Answer. ATTENTION. There was no risk at all and there was no "huge conspiracy – there was a "passive sabotage" operation. CIA Director John McCone, FBI Director Edgar Hoover and Secret Service Director James Rowley made a deal not to touch Lee Harvey Oswald until operation is over.
Question 3. Why was Kennedy murdered in public? President Kennedy was a sick man, taking a lot of pills daily. He had Addison’s disease which, in addition to susceptibility to infection can cause weakness, weight loss and low blood pressure; so he was taking cortisone. For his back pain Dr. Max Jacobson injected him (and Jackie) with a mixture of unspecified (! ) multivitamins, hormones, steroids, enzymes, and animal organ cells. Kennedy also used cocaine, marijuana, hashish and even LSD, especially during dates with women, including prostitutes —- for many people this was not a secret. There were enough opportunities to stage a death in private.
Answer. This had to be a public execution with a very clear message for the next Presidents – "Don’t touch the CIA! " and it worked until now. I want to touch CIA.
Question 4. What was the rush?
Answer. Kennedy wanted to eliminate CIA. JFK's assassination was planned by a very professional expert. It might be Gestapo Mueller who, unlike other assassins, had a very good reason to keep his mouth shut. That's why Congress wants to keep 40, 000 documents on JFK case classified for another 20 years.
June 5, 1968, Los Angeles, California
After winning the California primary election for the Democratic nomination for the US President, Senator Robert Kennedy was shot as he walked through the kitchen of the Ambassador Hotel. Sirhan Sirhan, a 24-year-old Palestinian immigrant, was convicted of Kennedy's murder and is serving a life sentence for the crime. Robert Kennedy promised a full investigation of his brother's assassination in case he was elected.
1995, New York City, Carlyle Hotel, New York City
John Kennedy Jr. who said once that his father's death investigation was the most important thing of his life, approached Princess Diana Spencer for an interview for his "George" magazine. They met at New York Carlyle Hotel where JFK dated Marilyn Monroe – a holy place for John Kennedy Jr. where he would never have "hot sex" and "try cocaine" with Diana. It was a business meeting, an "investigation" meeting. In 1995 CIA wanted me to kill somebody very important – it could be Diana and John Kennedy Jr.

August 31, 1997, Paris, France
CIA used my instructions on staged car accidents to kill Princess Diana. Diana was fatally injured in a car crash in the Pont de l'Alma road tunnel in Paris, which also caused the death of her boyfriend, Dodi Fayed.
Billionaire Mohammed al-Fayed, Dodi's father, recruited a "mole" inside CIA, somebody who knew the Agency had a file on Diana. He didn't get it of course through Washington, DC District Court and the mistake was – he had to recruit somebody with straight access to archives. If Diana left a notice on her talks with John Kennedy Jr for her sons, they might be next CIA victims. I can tell Mohammed al-Fayed what's in Diana's CIA file for free – surveillance documents, a video tape of the Carlyle Hotel meeting, a plan to stage the car accident, a file on me if I had to do the job.
If I have to investigate Diana's death, I would start with a very simple question :what happened to the driver, the Ritz security chief Henri Paul? He tried to out-run paparazzi by speeding down a Riverfront Expressway, but lost somehow control of the Mercedes S280 near the entrance to the Alma Tunnel and crashed into a concrete pillar at an estimated speed of 65 to 70 miles per hour. He died on impact of a severed spine and a ruptured aorta.
Attention. The tests showed an extraordinary high (not explained until now) level of carbon monoxide in his blood (20. 7 %), which should have caused a severe headache, dizziness, confusion and absolute aversion to alcohol. Very heavy smokers can have a level of up to 9%, and Henri Paul was not a heavy smoker. There were no ventilation problems in his apartment, office or car. The gas didn’t appear from inside Mercedes because no other passenger was affected. So, what happened to Henri Paul?
July 16, 1999, Atlantic Ocean off Martha's Vineyard
CIA killed John Kennedy Jr. in a staged plane crash. Kennedy along with his wife Carolyn and sister-in-law Lauren were reported missing when the Piper Saratoga II HP he was piloting failed to arrive at its planned destination, the Martha's Vineyard Airport in Vineyard Haven, Massachusetts.
Episode 1. Kill Bill Clinton

Is this a "protection"? No, it's a "perfect mark' situation for a sniper, I mean, for me.
September 1, 1995
I was recruited by CIA and had to work as a killer and special operations expert for three agencies – CIA, FBI and the U. S. Secret Service (they approached me directly later). I had to spy on the White House and the U. S. Congress and kill American politicians. The U. S. Secret Service wanted me to kill for them as well.
Also, I, a KGB spy, had to teach American presidents how to rule America and created "The Professional" system – special instructions on successful election and re-election campaigns, strategic planning and top decisions making, national security, foreign policy and diplomacy, propaganda, economy, war and special operations. That’s why Bill Clinton won 1996 re-election campaign. In 2007 it was published as the White House Special Handbook. Obama was using it, and now – Trump.
I could never imagine that in America I could have a unique status, "carte blanche" which means a “license to kill” any politician who is the threat to CIA.
CIA and FBI also asked for effective interrogation, tortures and murders methods and readily used them in Guantanamo, Iraq and Afghanistan. I, not Condi Rice or Hillary Clinton, designed the world domination, “controlled chaos” and “color” revolutions strategies successfully used to blow up Yugoslavia, Tunisia, Libya, Egypt, Syria, Ukraine, Yemen, and unite USA and EU for the World War III for Russian resources.
But CIA + FBI + Secret Service wanted more from me – they had "a hell of a job up to my high professional skills as a former KGB anti-terror “Nabat” (”The Bell”) group sniper.
Working abroad – Europe, Asia, Middle East – was OK with me, but I had no intention to kill politicians in America and play Lee Oswald-2. They've pressed me hard in return.
Who was the target? President Bill Clinton – CIA wanted me "to stay close to him".
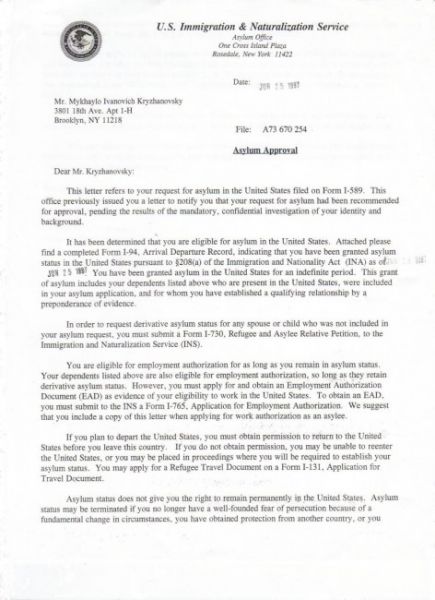
CIA and FBI awarded me with immigration status for my consent to kill President Bill Clinton.
I knew Bill Clinton's favorite "Filomena" restaurant in Washington, D. C. and could kill him at the entrance with a decent sniper rifle like M21 (700 m effective accuracy).
CIA + FBI+ secret Service didn't guarantee my personal security, so, and I couldn't do “a big job” and Bill Clinton has to thank for saving his life.

“Filomena “ restaurant where Bill Clinton used to dine with other presidents.
Episode 2. Kill Barack Obama
Putin and Obama hated each other. Right now I'm not going to tell you my version of Obama's real biography.
What you'll see is "passive sabotage technology" again which means that one or all three directors (CIA, FBI, Secret Service) work(ed) for Putin.
Kill Obama or go to FBI "special jail"
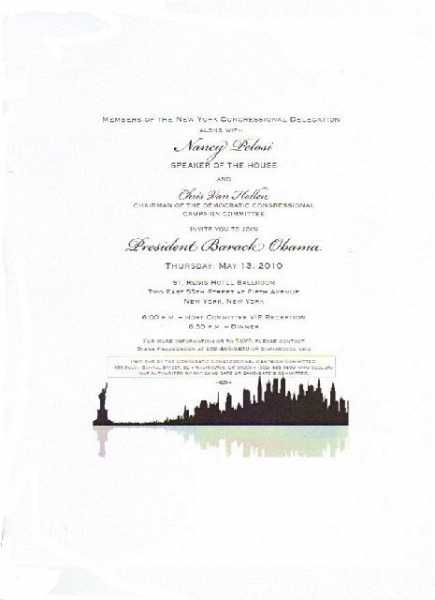
Robert Mueller and CIA Leon Panetta really needed me for another conspiracy. To kill Obama.
They sent me this invitation for a dinner with Obama in NYC to set me up after the President's assassination.
March 12, 2010, New York.
An invitation for a dinner with President Obama and Speaker of the House Pelosi came from DCCC (Democratic Congressional Campaign Committee) signed by Ian Sugar, Director of Development, Hillary Clinton’s big friend. "Mike, we wanted to make sure you received this invitation for a very special occasion. We would love to have you be a part of this event. DCCC needs your support to fight for the American people. We hope to see you on May 13th in new York City".
Thank you, Mr Mueller. So, I had to come to St. Regis Hotel, New York to join President Barack Obama Thursday, May 13, 2010 (St. Regis Hotel Ballroom, Two East 55th Street at Fifth Avenue, New York, New York). 6:00 p. m. – Host Committee VIP Reception 6:30 p. m. – Dinner
OK, I got St. Regis ballroom plan. Actually, I could eliminate “Obama” but it’s a suicide to work on the roof of the hotel.
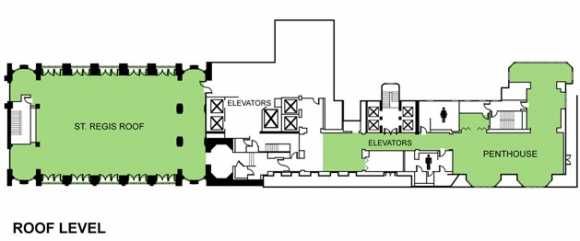
It wasn't very complicated job if I would have taken it. All I had to do was: buy 9mm Zig Zauer (Secret Service pistol), practice shooting in the forest upstate, come to St. Regis unarmed, disarm any Secret Service fat pig and do the job.

Obama protected by a pig.
The problem is, I'm 40 years in espionage business and I'm always listening to what my intuition says. It was a 100% CIA-FBI-Secret Service pre-assassination setup – I come, they kill “Obama”, arrest me and kill me in a jail same day. Same thing they did to Lee Harwey Oswald.
It was a very serious problem and I've informed the U. S. Special Counsel Patrick Fitzerald.
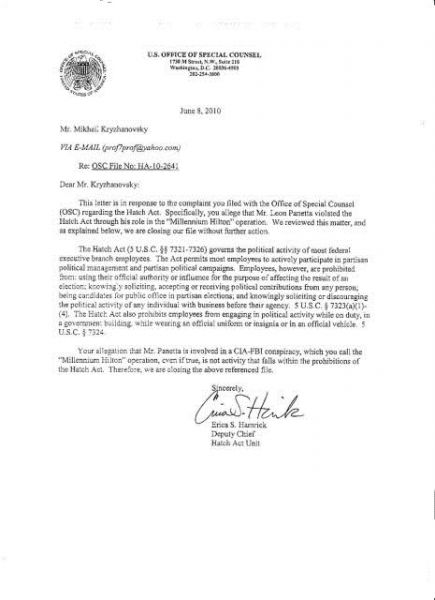
June 8, 2010
Bill Clinton and Obama's murders were not Patrick Fitzerald's ( the U. S. Special Counsel) business – he didn't want to get a bullet from Mr. Mueller or Mr. Panetta
U. S. Office of Special Counsel 1730 M Street, NW, Suite 218, Washington, DC 20036, 202-254-3600 RE: OSC File No: HA-10-2641
Dear Mr. Kryzhanovsky,
This letter is in the response to the complaint you filed with the Office of Special Counsel (OSC) regarding the Hatch Act. Specifically, you allege, that Mr. Leon Panetta [CIA Director – M. K. ] violated the Hatch Act through his role in the "Millenium Hilton" operation.... We are closing our file without further action... The Hatch Act (5 U. S. C. p. p. 7321-7326) governs the political activity of most federal executive branch employees.... Your allegation that Mr. Panetta is involved in a CIA-FBI conspiracy, which you call the "Millenium Hilton" operation, even if true, is not the activity that falls within the prohibitions of the Hatch Act. Therefore, we are closing the above referenced file. Sincerely, Erica S. Hamrick, Deputy Chief, Hatch Act Unit
I’ve called the White House and sent e-mail to Barack Obama, telling the whole story and saving his life in such a way. Obama made a mistake – he asked Secret Service to look into the case.
And Secret Service sent a team to kill me
January, 20 2011
FBI special agent Eric Perry, FBI NYC field office (tel. 718) 286-7100), informed me that my actions [telling the truth – M. K. ] made "high authorities, people on the very top extremely nervous". Perry said I better disappear for some time if I don’t want to end up at FBI “special jail”.
I have a question for Robert Mueller, Special Counsel who's overseeing now the investigation into ties between President Trump’s campaign and Russian officials :
FBI has its own secret jail in New York City to torture and kill people – is it constitutional?
I was sure CIA- FBI -Secret Service planned to kill me. I was right – the U. S. Secret Service Director Mark Sullivan sent a team of killers to hunt me.
October 12, 2010
I’ve got confidential information that two Secret Service teams were hunting me all over New York City: team #1 (two guys) and team #2 ( two guys and a woman).
Team #1 asked my friend to give me their phone number, so I could call them, emergency.
Team #2, armed with handguns, broke into my wife’s apartment, searched it and interrogated her in a very rude manner, ordered her to keep their visit secret, took her PC and left. Soon after that my wife (we were separated) had a stroke and in 2013 she died.
I talked to team #1 on the phone and then I met them in a safe place. They said they came from Washington to stop team #2 from killing me. They also asked me to shut up about the dinner with Obama. I said: "If they want to kill me, tell them to put a sniper in a house across the street – I'm not scared". They got very nervous and asked me to slow down and stop talking if I don’t want problems.
I got team #2 members’ names Here they are, my killers: Chris Lienemann, special agent, tel. 718-840-1263, Susan Klemm, special agent, tel. 718-840-1448, Gene Gurevich, special agent, tel. 718-840-130
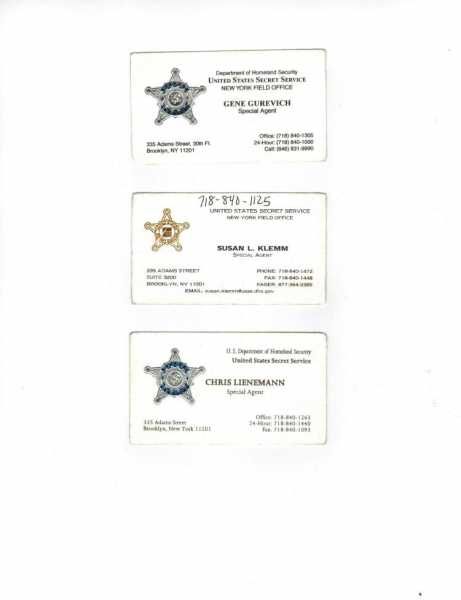
Episode 3. Kill Hillary Clinton
Hillary Clinton was (is) viewed by Putin as the biggest threat to Russia's national security and the hawk who might start the war in case she's elected the U. S. President. This threat had to be removed. "Passive sabotage" technology again.

June 22, 2001
I've sent a letter to the U. S. Senator Hillary Clinton and asked her to help me with my family reunion, blocked by CIA + FBI + Secret Service. She responded fast, she was scared and she didn’t ask a single question about the CIA-FBI conspiracy and my job.

She didn’t know what to do for half a year, and I had to inform her about CIA-FBI-Secret Service conspiracy, and the fact that I've saved her husband's life. It was kind of a blackmail, of course, and it worked. She had to fight three directors and she won.

September 17, 2002 White House letter
On top of it, I've informed President George W. Bush on the conspiracy and he sent a request to the Department of Justice.

FBI Director Robert Mueller and his CIA and Secret Service co-conspirators blocked (! ) the president's request successfully – I never got any information from the Department of Justice. Good job, directors – together you are more powerful than POTUS.

No matter what, three directors wanted me back to kill politicians, and that's the "reminder" I got from my bosses.

August 9, 2006, Lefrak City, Queens, New York
At 8 A. M. I saw a flyer next to the door of my apartment – this one.
ATTENTION : There were no other flyers in Lefrak City – why? It was a personal message from three directors – she is the one we want you to kill.
Now, do you know what’s Lefrak City?
It’s 10 old brick 18-floor projects for poor African-Americans, Latinos, and Russians. The most dangerous area in Queens and the New York State, stuffed with street gangs, crack cocaine, prostitutes and illegal guns. In two minutes I was at the place – just to make sure a Senator and a former First Lady Hillary Clinton is protected by the "best of the best" – the U. S. Secret Service.
I was sure they watched the area for the last 24 hours. I was sure the access to the area is restricted. I was sure that one week before the event local police and FBI instructed the secret sources to stay at alert and report any suspicious activity and people who had or tried to purchase illegal guns, and who want to kill Hillary Clinton. I was sure bad guys and aggressive psychos were isolated temporarily or monitored at least. I was sure technicians checked the air, soil and water (in the open pool) for radioactivity and toxic substances, looked for explosives and brought a trained dog. I was sure there was no access to a single roof and they put metal detector at the entrance to the area. I was sure they double checked the guest list. Kill me, but I was dead sure the Secret Service team would never let any bad guy approach Hillary. I was wrong.
8. 30 A. M. Nothing, nobody.
The place was a heaven for terrorists: – a circle of six 18-floor-1500-window buildings (such meetings in the open areas close to residential buildings are not allowed for people guarded by Secret Service ) – a playground; – an open stage under a small roof (no walls) – a BBQ place – a pool.
And 6 hours to get ready for assassination: – observe the place and plan the operation – put a mine under a stage – try a silenced sniper rifle from the roof and make necessary corrections if there are any deviations – place the whole army of terrorists all over the place.
ATTENTION : I've checked one roof – the door was open, thank you.
11 A. M. Two girls, three assistants, free "Pepsi", 2 cops, no restriction, not even a "Don’t cross" tape. 1 P. M. About 500 people came to the playground – retired old men and women, homeless alcoholics, drug addicts, screaming psychos, kids, teens and reporters. 2. 30 P. M. People screamed like crazy when Hillary finally appeared and tried to make her way through the crowd. Any psycho could kill her with a kitchen knife – cops and two Secret Service agents were as passive as they could. She got to the stage encircled by a wild, absolutely uncontrolled crowd. One agent was standing behind her, another one – on the stairs. No security.
She made a 15 minutes speech and then I’ve witnessed a total uncontrollable chaos – still on the stage, she tried to shake hands and people went wild; somebody gave her flowers (absolutely unacceptable thing), somebody asked her to hold a baby to make pictures; people screamed and pushed each other. Agents paid no attention, chewing gums, proud of their James Bond style sunglasses. Poor Sabini asked people to move away – nobody cared. Only when young girls jumped up on the stage, police officer restricted the place with a yellow tape – the Secret Service guys were surprised (! ) At 3. 30 P. M. she left the playground and had to move through the crowd again.
I was shocked. It was a very easy job to kill her at any public place – Secret Service allowed me to do anything I
July 30, 2012, New York City.
I know why the U. S. Secret Service wanted to kill Hillary Clinton. Somebody on top didn’t want her to be elected the U. S. President. Never.
A meeting with Secret Service, this time – special agent Jason Pietramica and his partner, tel. 718-840-1000, New York office.
He was nice and promised to help me and give me a job. What was the job? Murder, of course.

Professional questions followed : What are my political views? Do I visit the places were Bill and Hillary Clinton appear in public? Do I plan to see them, get in touch with them?
My answer was a big "No".
Pietramica got angry but then changed the subject and the object.
They wanted me to consider a trip to Russia to do a professional job. As I understood, they wanted me to terminate Putin, the President of Russia. They knew whom to ask to kill Russian President as I know perfectly well how Russian FSO Special Service protects Putin, I was doing same job in 1985, protecting Andrew Gromyko, the Soviet Parliament speaker. I didn't agree.
Pietramica was ready to kill me right there.
June 29, 2012

James Clapper, Director of National intelligence.
I've contacted his assistant William Shea (williams1@dni. gov). They asked CIA about me and Shea called me advised me to go back to CIA and FBI. "I'm not authorized to talk anymore. Good luck".
Episode 4. Kill Trump
There's nothing strange. I'm sure, Trump tried some independence from Putin,, his handler, and Putin's reaction was very negative and aggressive. "Passive sabotage' again.
Right now, after G20 meeting, Trump is going to behave. I can image the 2 hours 16 min lesson he got from Putin!

March 20, 2017
I got a phone call from Scott, Secret Service special agent, New York Office, tel. 646-592-2686, who asked me to meet him in Rego Park Center café, Queens, New York.
His first option was the secret Service field office in Queens, but I've rejected it.
Scott didn't want to talk much on the phone, but I've insisted on the details. He said it’s going to be a very important conversation about Trump. Clear. They wanted me to kill Trump – why?
Scott promised he'll come alone but then he made a mistake saying that he'll bring "somebody". It was enough for me to say "I don't trust you". Because “somebody’ could be a team – I say “no” and they kill me right there.
March 21, 2017
I've called the Secret Service Director's office, FBI and CIA HQs and demanded to stop the Trump’s murder. But if they want to kill me – they are welcome, I’m not scared, I have nothing to lose, I’ll buy I gun and I’m gonna fight.
They were scared to death and promised investigation.
PART 3. PUTIN GAVE INSTRUCTIONS ON TRUMP'S ELECTION (full document by M. Kryzhanovsky).
INTRODUCTION
CBS NEWS June 23, 2017, 8:16 AM
Vladimir Putin gave direct instructions to help elect Trump.
A report claims Russian President Vladimir Putin gave direct instructions to help elect Donald Trump president. According to a Washington Post investigation, former President Obama received a secret CIA report in August. That report "captured Putin's specific instructions on the operation's audacious objectives – defeat or at least damage the Democratic nominee, Hillary Clinton. "
CBS News confirmed last year that U. S. intelligence officials knew that the Russian government operation to interfere in the U. S. election had been approved by Putin himself, but they were reluctant to reveal how much they knew out of concern that sources and methods could be compromised, CBS News justice and homeland security correspondent Jeff Pegues reports.
The Post reports that U. S. intelligence agencies had sourcing deep inside the Russian government capturing Putin's direct instructions in the operation.
The Post also reports that before he left office Mr. Obama set in motion a secret program that authorized the deployment of "implants" in Russian networks – digital bombs that could be triggered in a retaliatory cyberstrike in the event of Moscow aggression – and that it would be up to President Trump to decide to use the capability.
CBS News confirmed that Obama officials felt that their effort to expel Russian diplomats in retaliation was undermined by the incoming administration.
Determining whether that is true is part of the ongoing investigations. CBS News has confirmed that congressional investigators are looking into whether Trump campaign associates obtained information from hacked voter databases during the election.
So far there is no evidence of that, but it is a sign that the congressional investigations are expanding.
HOW TO WIN PRESIDENTIAL ELECTIONS
By Mikhail Kryzhanovsky
These instructions were written for KGB in 1987, updated for CIA in 1996
1. 1 Get Ready
Before you make a decision to run for President, you must determine for yourself if you can handle the Oval Office: Are you willing to accept such a huge responsibility and put the rest of your life on hold? Are you skilled in dealing with big groups of people? Can you motivate the nation to action? And repair about your biography, which is, of course, not perfect.
Then you must:
1. Decide how are you going to impress party leaders.
2. Make intensive preliminary polling to determine your chances.
3. Poll big demographic groups as well as smaller groups of people from selected demographic groups.
4. Determine the rationale for your candidacy. What is your political record?
5. Delay announcing your candidacy until late in the year before the election to minimize expenditures and risk, avoid legal spending limits, avoid voter fatigue, avoid getting involved in unnecessary controversies and contradictions.
6. Carefully study applicable election laws before you start fundraising and spending.
7. Write your campaign plan (strategic objective, tactical targets, key message, target audiences, methods of delivery, timing, your progress evaluation — polls).
8. Learn the political and economic issues and develop your campaign message.
9. Prepare the “speech” and the “book” (the “speech” is the standard speech that you deliver and it should answer the most important question — why are you running for President; the “book” contains the message and all possible questions on your program.
10. Take a benchmark poll – it will provide the road map for your campaign.
11. Establish your strategy and message
12. Study the results, polls and “successful” areas of previous election.
13. Establish a perfect graphic look (image).
14. Develop a fundraising plan, put the fundraising team in place and start asking for money. No money – no campaign.
15. Create a personal contacts pyramid (priority and general contacts) because personal popularity is your starting point.
16. Set up offices.
17. Get professional candidate training.
18. Determine the focus of your presidential policy (taxes, crime, education, health, social security, national security).
1. 2 Working with the Staff
Basic campaign staffers include:
1) campaign managers — they plan the campaign, organize and recruit the staff, supervise daily campaign operations, make priority contacts with key special groups big business and big media, correct the strategy and make quick decisions. It has to be someone you trust completely.
2) campaign consultants-specialists in both direct (personal and public meetings) and indirect (media, advertising) campaigning
3) strategists
4) analysts
5) issues researchers
6) speechwriters
7) lawyer (interprets election and campaign reporting laws)
8) personal assistants (work on issues in foreign and domestic policy in cooperation with the whole team).
9) fundraisers (plan and execute fundraising events — dinners, parties, auctions, direct appeals through telephone and letters, receptions, computerized fundraising). Big business has to be approached by rich fundraiser only.
10) scheduler (determines events and locations — TV and radio talk shows, news — conferences, meetings with students and professors at college campuses and with professionals at their associations’ annual meetings, special events and fundraisers especially with ethnic leaders in big cities, as well as festivals and big shows where celebrities demonstrate their support, large extravaganzas, meetings at civic clubs, farm warehouse auctions and special auctions, local civic events. Also, scheduler makes arrangements with local media before your visit and sends media the copies of your speech; insures that good crowd will attend the event and takes care of transportation arrangements). The purpose of the campaign planning and strategic scheduling is to draw press attention to the candidate for transmission to the voting public. That’s natural — the candidate who has enough media attention has much better chances of recruiting public acceptance and raising campaign funds.
11) image makers – political consultants who sell your public image as a clear, simple, portrait-like characterization, acceptable to all groups.
12) “hit men” – campaign consultants who are experts on negative advertising, designed to “kill” your opponents.
13) field staff (in target cities mostly). The most important person at any local office is the coordinator — he establishes organization and contacts influential people and political activists. Coordinators must be appointed to each special interests group (women, minorities, unions, college students, public interest activists, the professionals)
14) local volunteers are needed to work in the offices and the streets. Your family has to take an active part in your campaign, too. Your wife and kids are your visual image makers
15) running mate
During the “invisible primary” which is the nomination, campaign you have to make visits to party organizations especially in pivotal states, such as the above mentioned Iowa and New Hampshire where you have to make as many handshaking and personal contacts as possible. Key staffers must travel with you.
1. 3 Fundraising
You are the #1 fundraiser yourself. You must have substantial financial support to compete. You must have an overall plan which outlines expenditures month by month. It is imperative to have even more money on hand at the end of the campaign for an advertising blitz when the voters are most attentive and the field of candidates has been winnowed out. Half of a campaign funds go to media.
Failing to do well in early caucus and primary contests means more than losing delegates — it means that contributions stop.
Your speeches have to be a fun, and match the meal and drinks — don’t be heavy and too political. Actually, you have to run two campaigns (a political campaign and a fund-raising one) and you must win both; if you raise less money than your opponent, you lose, because you don’t have enough money to inform, influence, and motivate your voters. If you are a Senator or a Congressman, you already have an advantage in money (free postage on mail sent to your constituents, automatic media coverage) and you can use your congressional staff to assist your campaign. Besides, you are interviewed by reporters for free as an elected official. You can also ask your political party for a contribution to your campaign. Party money can be given in two ways – as a “direct” contribution or as a “coordinated” expenditure. Direct contributions are funds given by the party to candidates to do with as they please. Coordinated expenditures are made for such services as polling and TV advertising, but the party has a say how the money is spent.
Then you have to ask PACs (political action committees) to fund your campaign, too. PACs are special-interest groups which consist of people who pool their money in order to contribute it to candidates or political party committees who share their political, social, religious or economic views.
To finish well in pre-nomination popularity contests (“straw polls”) you have to appear daily in TV ads, and prime-time news coverage — after the primaries media “label” winners and losers and that affects voters and contributors a lot. Media, especially the most influential “the New York Times” and “Washington Post” (their publications influence decisions on which news stories will be carried on TV channels), have to take you as a very serious contender.
The key rules in fundraising are:
– find some “fat cats, ” quick
– get fundraisers with lots of rich friends
– get money from those who usually contribute
– go to new York, Florida, California, Texas
And the most important strategy is to raise big money for yourself and prevent big money from being spent against you. Early fundraising is crucial to a campaign because of the high costs organization and the need to demonstrate viability. The best states for fundraising are California, New York, Florida, Texas, which supply half of all campaign donations. Go right ahead and raise money in New York and spend in Iowa and New Hampshire.
1. 5 The Press
The press officer (contacts media, takes care of newspapers, radio and TV ads) — the person who markets you — is the boss of advance team that takes care in each state of a total exclusively positive press coverage. To my mind, the best choice for this position is a former journalist with good wide connections to media. He prepares press releases and press kits and schedules interviews and press conferences with the positive vision and attitude reporters (press or media kits contain your photos, a brief biography, campaign position papers, printed brochures and names of contacts for additional information).
The technique in good paid advertising is to go with those ideas, arguments, thoughts, themes and believes in which people are already inclined to believe or ready to accept. There’s no difference between commercial and political advertising — you just substitute a car or shampoo for a human being. Modern presidential campaigns center on “media events” — staged public appearances, during which reporters can talk with you and take pictures (if you have too much money, you can organize media wave — a very large amount of political advertising on TV). Then, the “walking tours” must be scheduled when you, followed by reporters, photographers and TV crews visit potential supporters.
Simultaneously your aide sets up press conferences, selects interviews, and background briefings. You have to talk to press 24/7 and everywhere on the campaign bus, train or plain, hotel, etc. A good thing is — you get free media coverage and people trust it more than paid coverage, like TV and radio commercials.
You win if you obey these rules:
– if you can manipulate media – you manipulate the nation (sorry, it’s harder to manipulate free coverage).
– the media makes the election, not the voters
– a presidential campaign does not allow for privacy
– newspapers put emphasis on issues, TV on image, style and ability to communicate.
– never lie to reporters; they will make sure it backfires on you sooner or later.
– if an influential newspaper, radio or TV station endorses you, you have their supporters, readers, listeners and viewers.
– people remember much better what they see, not what they read; if they don’t see you on TV, you don’t exist.
– TV talks to 98% of Americans and takes your message — and other messages about, or against, you – immediately, straight to the nation.
– TV, not your political party, is the #1 channel of communication between you and the public
– your political party is nothing but a service center and a money machine. Parties divide the nation while your message has to be one of unity.
– take it seriously if The New York Times takes your opponent seriously.
– it’s important to know what your opponent is saying to reporters privately, “not for attribution. ”
– if you live in heavily populated state, like New York, California or Texas, you start the presidential election campaign with much better coverage.
– never fight the media like the Nixon administration did – they kept a list of Nixon’s critics (famous reporters), so they could be targeted for harassment, accused of income tax evasion, etc. What happened then? The reporters felt like heroes, Nobel Prize winners. Better target them for buttering up, and feed them lots of stories with a spin in your favor, instead.
1. 6 Polls
Pollsters works through newspapers, Internet, telephone surveys, person-to-person surveys, mailed questionnaire to selected voters. They provide voters' behavior research and analyze past election data. They tell to you how well-known you are, how well you perform, what are the voters’ preferences. You should poll voters in each state in proportion to that state’s share of the national vote. (You must have at least one polling company on payroll. ) Polling is of extreme importance in presidential campaign because it’s the tool to correct your strategy, determine “positive” local areas and supportive voters and work with them, it tests the nation’s attitude to your personality and your issues and that means you can calibrate your message and calculate your success. The most important thing about polls is that they play indicator and identify support or hostility. And the golden rule here is: you have to ask the right question if you want to get a useful answer.
At the same time polling is one of the most expensive elements of a modern campaign because now you have to receive information on too many groups and issues, including groups with specific economic, ethnic, religious, geographic, educational, occupational and residential characteristics and how those characteristics affect attitudes about a wide range of policy issues.
Polls also help you:
– to decide whether to run or not
– improve your recognition and image
– target opposition’s weakness
– formulate media ads
Your pollster has to pinpoint blocks of voters (swing districts) who are undecided and who might be persuaded to vote for you. Experience shows that 40% of public attention go to social problems, 40% — to economy and 20% — to international matters, but if the United States is at war, the situation is different and national security turns into a top priority for everyone. And watch out for campaign spies — keep polls analysis and media plan secret.
Practical polls:
“Benchmark” – surveys of the whole nation which provide basic information about your chances and the nation’s political preferences (it’s your “presidential decision maker”).
“Follow-up” – surveys are used to gather more data about particular concerns raised in initial benchmark surveys. They are conducted state by state and are used in planning campaign strategy.
“Panel” – surveys are used to refine strategy further by re-interviewing previous respondents to determine opinion shifts on specific issues within various demographic categories. They are supplemented by continuous “tracking polls” that measure fluctuations in general voter support for the candidate across time.
“Special group” – used to poll the debate results. Selected groups of voters watch candidate debates and register their “positive “ or “negative” feelings toward the candidate’s specific statements or actions. After that analysts tabulate and analyze the reactions of the whole groups.
1. 7 Campaign Golden Tips
Never behave as if you think you are God’s gift to the nation.
Be presidential – look calm, sincere, knowledgeable and open Mother of the nation.
Be electable – prove to the nation that you are the best choice.
No one has ever been elected the US President without winning the New Hampshire primary.
Primaries direct financial backers to a promising candidate.
Voters judge you by your friends – appear with popular politicians, big business, labor and interest groups leaders, and show business celebrities. Advertize your meetings with Congress members and world leaders (go abroad if you have a chance to meet a world leader).
The most important event in the election process is the National Convention, not only because the eventual finalist candidate is actually nominated but because after that the campaign’s audience increases (more than twice as many people vote in general elections as participate in the nomination process). You have to decide how to win the support of these new voters as well as to appeal to people who identify with the other party and partisans who backed losing candidates for the nomination.
1. 8 Choosing a strategy
Any strategy is good if it helps you to win support of a majority of people chosen by the state parties to be delegates to the national convention. Your choice of a strategy depends on your current position:
A. If you are an incumbent, you have to stress that the American people’s life improved a lot during your first term. You can count on successful start because you are guaranteed to be known actually to every American, and the Oval Office lends you credibility and respect. It’s of vital importance to have economic accomplishments — in such a case well-timed announcements of government statistics on the economy or of plans for domestic initiatives can also help you. Listen, I didn’t tell you this, but you have to manipulate (stimulate) the economy during the election year with tax cuts that can help reduce unemployment, and with social programs financing.
Of course, you’ll have to pay for it, but that will happen after you are re-elected.
And a good thing is – an improved economy erases voters’ bad memories of past years.
Try to avoid too aggressive campaigning – it’s a sign of weakness. Make official appearances in carefully controlled settings. Influence media coverage with official presidential actions and use “pork barrel” politics to appeal to specific constituents. You can also benefit from the nation’s reluctance to reject a tested national leader for an unknown newcomer. And if you start important foreign policy initiatives, it will guarantee you continued media coverage.
If you have poor chances to be re-elected, you can play the “national security” card:
– find a US “enemy”
– start a media psychosis (see propaganda tricks and brainwashing )
– concentrate power (special services) to establish a total legal control on the nation
– provoke an international conflict, restricted or full-scale war
– send a message: “If you are against the President, you are against America! ”
B. If you are a challenger you have to convince the public they don’t live better than they did 4 years ago, or, if the economy is OK, point out mistakes that were made in the foreign policy. Or make up some social issue that will get passions inflamed and hijack the headlines.
KRYZHANOVSKY ”GOLDEN” STRATEGY
You should seek to position yourself as close to the opposing candidate as possible in an effort to capture the “median voter” in the center, and then take by default everyone else on their side of the ideological spectrum. You have to embrace this strategy and move as close as you can to the moderate Republican position with the expectation that you can take all of the votes to the left of this position. Clear?
The job is tough if you challenge a President who is popular — first, you have to break down his positive image; second, you have to portray yourself as a much better replacement. You have no choice but to start with the “outsider” strategy — you present a “fresh face” to voters weary of the current political situation (in such a case you have to attack administration in a very aggressive manner). Plus, you must give quick response to your opponent’s charges (get advance copies of his speeches through friends in the media).
Then, show yourself as a smart and diplomatic person using a special “triangular” strategy, when you, like majority of the voters, place yourself between liberal and conservative positions. Evaluate situation – you may need “early knockout, ” when front-runners hope to use their early strength in polls, fundraising and endorsements into decisive primary victories at the beginning of the primary season. The hope is that the candidate will build such an impressive early lead that the competition quickly drops out.
A “shift” is the most popular thing with challengers – if the President is good with national security, they point out to the problems in economy, if he’s good on the economy, they point out to the problems in national security – very simple. (Watch his mistakes anyway – you can benefit from them. Bill Clinton would never have run for President in 1992 if someone from the Bush White House hadn’t called him in 1990 and asked him not to run. That phone call was one of the most stupid political moves of the 20th century, because it convinced Clinton that they thought he had a good chance to win.
Be simple, identify with “ordinary people” and no matter what tell the voters your parents or your grandparents “were like them – regular people, not millionaires. ”
1. 9 "Black" PR
You must know some very popular and efficient dirty tricks, like “negative campaigning” or “black" PR. To make a long story short: no matter what your opponent says or what decent people think about negative campaigning — “black PR” works! Use it to turn a rumor or a fact into a serious political scandal; respond to and neutralize the opponent’s attacks (using “black PR”) fast, before they are broadcasted or published.
It works best through intermediates (persons and organizations not connected directly to your campaign). You must have a very detailed file on your opponent (negative research) and then start spreading negative and all kinds of compromising data from his personal and political life. If he is or was elected official (Senator, Governor, Mayor), you can point out his mistakes and actions which were not popular. People must know in detail (get your staff to read a few books) the negative sides of his life, program and terrible consequences of his election. Remember also that a rumor repeated twice turns into a fact, especially if you start a “whispering campaign” in Congress.
A “negative ID” trick is my favorite: you identify your opponent with a totally unacceptable (for the voters) viewpoint, like: “There are those who want to stop the war on international terror and you know who they are! ”
1. 10 Attention : debates!
Debates are extremely important because they offer the only all-national event at which candidates can be judged. You and your opponent will be under huge stress as you both must operate simultaneously at the focus of attention of each other and of all elements of electorate. Debates are, actually, head-to-head confrontations with two main aspects: the pre-debate negotiations over whether there will be a debate, and the post-debate analysis of who did how well. The debates offer nothing new for the public and the basic strategy is to hope your opponent will make a mistake (President Ford made one in 1976, saying that: “There is no Soviet domination of Eastern Europe. ” People just didn’t want to hear it. Richard Nixon was very wrong in 1960 trying to debate on substance, while his opponent, John F. Kennedy, concentrated on style and on presenting the correct presidential image).
While preparing for the winning debates you must:
– have a detailed file on your opponent and study all his speeches and statements; ask yourself: “What does he have that
that I don’t have? ”
– train to answer all possible questions
– be ready to demonstrate deep knowledge of issues and your presidential bearing to a nationwide audience
– repeat your message but keep in mind that image is more important than ideas while you debate — people want to see your good looks, good clothes and nice smile.
And here are the debating “Don’ts”:
Don’t attack first — that’s a sign of weakness.
Don’t be over-polite — a little showmanship appeals to voters.
Don’t be too aggressive — it will ruin your image as a future President.
Don’t answer the questions too fast — that implies you are not thinking.
Don’t rush, no negative emotions, no sudden gestures (extra gestures mean that you are not sure what you are saying is correct).
Don’t disappoint people — speak in a clear and simple way.
And you restrict your influence if you sit.
Follow the rules :
No anxiety reactions – speech errors, moistening of lips, perspiring, shifting eye movements, body jerks. Gesturing with fingers apart communicates weakness, while gesturing with fingers tightly together communicates power.
Look at your opponent with intense concentration – it gives the attitude of command and comfort of the situation.
Answer a question you want to answer, no matter what question was asked.
If you give better answers, you are the better candidate.
Immediately after the debates your press officer has to give the media his biased impression and explain why you won the debates. Your pollster has to watch the polls results.
Tricks
1. Intruding into an opponent’s physical space.
Attempted by: Al Gore, 2000
Result: Failure
When Al Gore tried it in a rehearsal debate, his advisors cautioned against it. It looked awkward. It could come off as too aggressive. The risk was simply too great.
Al Gore decided to do it anyway: The vice president, all stocky 6’3” of him, was going to attempt to physically intimidate George W. Bush.
It was the last in a series of unforced errors Gore made in the debates of 2000 (the audible sighs, the pronounced eye-rolling while Bush spoke). Roughly ten minutes into the third and final debate, a townhall-style affair, Gore sloughed off his stool, a scornful look on his face as he saddled up to Bush’s side while the Texas governor spoke.
Bush responded not with surprise or fright, but with a quizzical look and an offhand nod of acknowledgment, turning back to the audience as the crowd laughed and he continued on with his spiel. Gore’s would-be power move had exactly the opposite effect: instead of looking dominant and in-charge, he seemed awkward and inauthentic.
2: Keeping your opponent in the shot, unaware
Attempted by: Bill Clinton, 1992
Result: Success
We take it for granted now, but the townhall debate is a relatively recent addition to the menu of presidential debate formats. It made its debut in 1992, its structure reflecting the style of the daytime talkshows that dominated the era’s airwaves: Donahue, Sally and Oprah.
Bill Clinton’s campaign lobbied to get the townhall format included in the 1992 fall debate lineup. Looking back, it’s easy to see why: the format plays well to his strengths, providing an opportunity to underline his natural charisma and easy folksiness.
It also created an opportunity for a very media-savvy campaign. Ahead of the debate, Clinton and his team carefully choreographed the candidate’s movement around the stage, working with producers to understand the camera placement. Clinton campaign wanted to “keep one or the other of his competitors in the camera shot at all times, a maneuver that circumvented the prohibition on cutaway [shots] of one candidate while another was speaking. ”
The result was that whenever Clinton was in shot while Bush or Perot spoke, he made sure to look stoic and thoughtful. Perot and Bush, on the other hand, were often caught unawares in the background of Clinton shots, including this oddly checked-out moment from the incumbent—underscoring the difference with the more telegenic Clinton.
3: Swapping out the debate’s stools.
Attempted by: Bill Clinton, 1992
Result: Success
In that same debate, one reason Clinton looked so at-home on stage is because the candidates were actually using the exact same stools that Clinton had rehearsed on. Reportedly, the Clinton campaign switched them onto the set without the permission of the debate’s hosts—and without anyone noticing. Paul Begala, a senior advisor to the campaign, later explained their rationale: “We wanted Gov. Bill Clinton to be completely at ease in his surroundings, right down to his butt. ”
It worked. The stools were far too tall for diminutive billionaire Ross Perot, who uncomfortably leaned against his chair for much of the debate. And while the chairs were the right height for Bush, the president often looked unsure of how to perch on a bar chair while looking confident and presidential.
4. Holding on to a handshake for too long
Attempted by: George H. W. Bush, 1988
Result: Success
In 1988, at his debates with Massachusetts Governor Michael Dukakis, George H. W. Bush shook the governor’s hand for an unusually long time. Ever since, it’s been the source of speculation: was the long handshake an intentional move by Bush, meant to emphasize how taller he was than Dukakis, or was it just a handshake that we’re reading too much into?
Regardless of whether it was intentional, it certainly showed viewers that there was a substantial height difference between the two men (Dukakis is 5’8” and Bush is 6’2”, a full six inches taller). On “Saturday Night Live, ” Dana Carvey’s Bush was shown shaking the hand of Jon Lovitz’s Dukakis, patting him on the head like a child before Dukakis headed to his lectern, where a mechanical lift hoisted him to a respectable stature. Without the awkwardly long handshake in the real debate, it’s quite possible that their height difference never would have been noticed.
5. The ambush handshake
Attempted by: Ronald Reagan, 1980
Result: Success
For the first 20 years of televised debates, it was not commonplace for the candidates to shake hands with each other—the debates started after the candidates were already onstage at their lecterns.
That changed in 1980—unilaterally. In their lone debate that fall, right before the cameras started broadcasting, Jimmy Carter and Ronald Reagan entered the stage from opposite wings and headed straight to their respective microphones, as was tradition. But while Carter stopped at his lectern, Reagan continued to stride across the stage, surprising Jimmy Carter by shaking his hand. Reagan seemed in command from that moment forward.
“Carter’s look of surprise suggested that he thought he was about to be knifed, ” wrote Kathleen Hall Jamieson. “The handshake was as lethal. How could Carter then cast a smiling hand-shaker as a mad bomber who would destroy Social Security, the environment, and perhaps the world? ”
Reagan repeated the gesture at the end of the debate, surprising Carter yet again—this time, televised. It made Reagan look amiable and in charge; Carter looked weak by comparison.
6. The unexpected audience member
Attempted by: John Edwards, 2004
Result: Unclear
In a famous incident on the floor of the U. S. Senate in June 2004, Vice President Dick Cheney told Vermont Democrat Patrick Leahy, “go f—k yourself, ” after the senator had accused Cheney’s former employer, Halliburton, of war profiteering.
So when it came time for the vice presidential debates that October, Senator John Edwards (D-NC) had a plan to get inside Cheney’s head during the debate: He reserved a seat for Leahy in the second row of the debate’s audience, where Cheney would almost certainly see him.
Cheney’s debate performance was characteristically reticent, though it’s unclear what, if any, role Leahy’s seat played in rattling him up. Reportedly, after the debate finished, the Bush-Cheney campaign called the Kerry-Edwards team to complain about the move.
7. The derisive prop
Attempted by: Negotiators for both Dan Quayle & Al Gore, 1992
Result: Détente
Every presidential debate is the topic of high-stakes negotiations by the campaigns involved, which will push for any number of advantages and concessions—from podium height to a chillier on-stage temperature.
In the run-up to the 1992 VP debate, though, Dan Quayle’s staff lobbied for the ability to let each candidate take a single prop on stage. Their plan was to have Quayle bring out Gore’s book, Earth in the Balance, and read a passage or two from it during the actual debate to embarrass Gore.
Gore’s strategists agreed to let each candidate have a prop, telling the Quayle team Gore planned to bring a single item on stage: a potato—an unsubtle reminder of a humiliating June 1992 gaffe where Quayle infamously misspelled the word “potato” while attending an elementary-school spelling bee, instructing a 12-year-old who had spelled the word correctly to add an “e” to the end. Quayle’s campaign speedily dropped their request for props.
1. 11 Speaking in Public
"Golden" rules
1. Your aides have to determine the “theme of the day” and brief you about the day’s events and issues. To get elected you must promise economic growth with low inflation and balanced budget no matter how grave the economic situation is.
2. Don’t be too specific on issues and tell people they elect their way, not a candidate.
3. Cite the Bible.
4. Don’t look too intellectual.
5. State repeatedly that you’re not going to divide the nation into supporters and enemies, Democrats and Republicans, “my voters and other voters” — be a leader to all. (But first, to win the nomination you must appeal to the more liberal sections of your party if you are Democrat, and to more conservative sections if you belong to Republicans).
6. Don’t talk much; transform your thoughts into examples and slogans.
7. Never say you want power, even if you want to save the nation in crisis.
8. Never talk down on big business. Promise federal financing, especially in economic downturns.
9. Remember: voters are extremely sensitive to tax-cut proposals and which social segment would benefit from them. The middle class brings you victory, so promise tax cuts for these people, with tax increases for the wealthy and high unemployment rates.
10. Even if the economy is OK, point out the signs of coming crisis and promise to change the situation fast. Keep talking about problems, though it’s hard to win if the incumbent President runs for re-election with balanced budget and economic growth.
11. You can be liberal on domestic issues, but you have to be conservative on national security (defense and foreign affairs).
12. Remember the “women factor”: there are more women than men in our country, women are more likely to be registered to vote, and among registered voters women are more likely to vote.
Use these tactics:
1. “Join the crowd” — this reinforces people’s natural desire to be on the winning side and it is used to convince the audience that your program is an expression of the nation’s desire for change, and it is in their best interest to join;
2. “Provoked disapproval” – persuade a target audience to disapprove your opponent’s message by suggesting that the message is popular with groups hated, feared or held in contempt by the target audience;
3. “Iinevitable victory” – you invite those who did not join majority;
4. “Neuro-linguistic programming” — you will be elected if you can do this better than your opponent and program the whole nation for a positive reaction. People always try to avoid anything and anybody unpleasant; and people are always looking for pleasant things and other pleasant people, somebody they want to meet again and again or at least see on TV. Everybody wants to be a winner; and to be a winner brings pleasure and self respect. Just convey this sense to the nation: “Vote for me and win! ” or “Vote for me or lose! ”, “The choice is yours! ”
PART 4. HOW PUTIN RULES THE WHITE HOUSE AND THE U. S. CONGRESS
I wrote these instructions for KGB in 1987, updated for CIA in 1996.
Putin and Trump use them to rule USA.

HOW TO MANAGE THE WHITE HOUSE AND THE U. S. CONGRESS
by Mikhail Kryzhanovsky
Come in!
Be strong. Be attractive. Be logical.
All you have to do during your first term is to take care of the second one.
The 2nd term’s agenda is to set your place in the world’s history.
1st year. You have enough public support to start big initiatives.
2nd year. Develop your initiatives.
3rd year. Go, go public preparing your re-election. Presidents often lose voters during this period.
4th year. All-politics year. Try to achieve important international agreement (a treaty) for the historic record. Win re-election.
Divide your day into hours and minutes : 30% of your weekly hours go to senior White House staff, 10% – to Cabinet, 5% – to Congress members, 5% – to foreign leaders.
No matter what, even if it’s a war time, sleep one hour during the day to give your brain a break, and finish your day at 6 P. M. After 6 P. M. do not read any documents, do not take any phone calls, do not talk to anybody but family members and close friends.
Eat whatever you want, but remember, the more calories you have to digest, the slower you think.
REMEMBER:
1. You are a national image (a national ideal based on pseudo-facts), a symbol of national unity, national continuity and the symbol of federal government. Leadership is the first quality Americans look for in you – they want a President who is steadfast in his convictions.
2. The power to control the federal budget is your top prerogative.
3. Define for yourself whom are you going to be:
– utopist (ideas manipulator)
– manager (Government and Congress manipulator)
– challenger (reformer)
4. Any problem turns into a political one if it threatens your power.
5. Use your legal right to press the nation and illegal ones to press the world to eliminate problems.
4. Once you’re in politics, you are a hostage of your status and you must sacrifice privacy in return for power.
6. Never play alone.
7. All your decisions are risk taking ones (any decision brings a problem). You may ask advice before you make a decision, but don’t listen to anybody afterwards. You are not paid for the quantity of your work but for leadership and ultimate decision making.
8. Correct political mistakes fast, before they become political scandals.
10. Never blame previous presidents for the problems they left for you – that’s a sign of political weakness.
11. Get rid of a White House tradition to deal with problems if they “knock at the door” only.
The White House Staff
Chief of Staff
The Chief of Staff reviews most of the documents that go to you, gives his/her advice after intense information processing and consultations with other agencies and then – he’s/she’s telling others what President wants.
A lot of people, including Congressmen and Senators, will try to reach you through him/her.
He/she has to give exact instructions to the Press Secretary on the White House message about current headlines and the President’s plans and actions (the Press Secretary works the same way with VP and First Lady/First Gentleman press teams).
He/she is responsible for your time and has to plan at least two months ahead your effective activity together with Communications, Scheduling and other policy offices’ Directors plus VP and First Lady/First Gentleman Chiefs of Staff. Besides, he/she has to do “dirty jobs” for the President like firing people or act as a “lighting rod” to draw criticism away from the President.
National Security Adviser
The National Security Adviser controls all the documents concerning national security coming from Defense, Homeland Security, State Departments, and national security agencies, and coordinates these offices.
His/her position is not subject to Senate confirmation, which, according to a long-standing Washington tradition, means that he/she can’t be compelled to testify before the Congress. He/she decides what papers the President should see and, what’s more, he gives his comments on any document.
ATTENTION :National security is 100% the President’s business, so keep this figure at some distance and don’t let him think of himself as your Number Two – foreign leaders will try to work through him to get to you or to influence you.
He/she has to oversee the functioning of the National Security Council (NSC), which is your foreign policy making tool and a “government inside government. ” This is something very special and convenient about the NSC – it’s responsible only to you and there’s not much Congress control over its budget. Plus, National Security Adviser is involved in every meeting between you and any foreign leader and is responsible for the schedule.
The most powerful of executive offices after the National Security Council is the Office of Management and Budget (it’s authorized to make cuts in federal agencies’ budgets, to advise you on national fiscal and economic policies, supervise execution of the government budget, evaluate the performance of federal programs).
Who they really are
Staffers (and Secretaries) prefer stability and don’t like if you’re “rocking the boat” – that’s why they often play reform-stoppers.
They don’t like to work hard and prefer to send you on “very important visits” abroad as often as possible.
They try to load you up with an extremely busy schedule and “feed” you witnh hundreds of useless documents, create artificial problems and conflicts to show off their hyper-activity.
They try to be your decision makers and they do influence you because, unlike Secretaries, they have daily contact with you; that’s why you don’t see Cabinet members as your principal aides.
They try to set you up by interpreting your decisions and orders in their own way, as every adviser is the “American President himself. ”
They know you won’t accept “complicated, ” “expensive, ” “risky” projects and they’ll try to sell you “simple, ” “cheap” and “popular” ones only.
Watch your senior staff and how they present ideas. If somebody wants to push his idea or a project, he will give you three options, making two of them unattractive. Naturally you pick the one he presented as least harmful.
Their dirty tricks
1. Fight for access (influence) to President or to people with direct access (aiming to get a better position if President is re-elected).
2. Isolate government from the President.
3. Influence = relationship with the President.
4. Get a table in the West Wing. You are nobody if you are stuck in the White House basement and see the President by appointment only.
5. Before you send a document to the President, have to look at it and ask yourself if it’s too immoral or too radical.
6. Never say “no” aloud to anybody.
7. Remain anonymous with conflicts.
8. Never bring bad news to the President – let it be some idiot, not you.
9. Never say “That’s impossible, ” no matter what the President is asking you to do.
10. Disappear (and find an excuse later) if the President is in a bad mood.
11. Never ague with the President if there’s somebody else present.
12. Learn how the President likes to do business (talking, giving orders, writing the documents and taking notes, managing official and non-official meetings) and his habits (food, drinks, cigarettes, favorite sport, movies, show business stars, writers, politicians; attitude to women) and try to copy him — the President has to feel comfortable with you.
13. Fight anybody who’s trying to do your job to be closer to the President.
14. Avoid taking on risky tasks controlled by the President in person (if necessary, try to “delegate” it to somebody else).
15. Avoid being associated with any failures.
16. Don’t say anything President doesn’t want to hear.
17. Use “Smith’s Principle”: if it can be understood by Congress, it’s not finished yet.
18. Write memorandums not to inform the reader, but to protect the writer.
19. No matter what subject is under discussion, employ the language of sports and war: say “breakthrough” instead of “progress”, never speak of compromise, consider “adopting a fallback position. ”
20. Every public appearance in with the President is an investment in your career after the White House.
21. Minimize the number of rivals.
22. Gain independence according to how much the President needs you.
23. Before asking the President for some personal favor, make him believe he’s going to get some (political) profit out of it.
24. Tell the President what he can do and help him try to do it, and never tell him what he shouldn’t do.
25. Avoid giving any personal gifts to the President if you are not Chief of Staff.
Every public appearance in with the President is an investment in your career after the White House.
There is an open power struggle between national security staff members and domestic policy staff and between those who develop new policies and initiatives versus budget staff.
How to Manage the Staff
Adopt a dominant management style:
1. Pyramidal, structured as hierarchy with you at the top, followed by the Chief of Staff and other key assistants. I strongly recommend this one – it insures a clear chain of command and provides precise channels of information going up and directives going down.
2. Circular, when you are surrounded by advisers, all of whom have equal access to the Oval Office. That means chaos (JFK style).
All your assistants are political assistants and everyone will try to play a policy-maker. But a good thing is that all of them were not elected and are responsible to you only.
Thus you can:
– reform your staff freely as there’s not even a word about it in the US Constitution
– interchange key figures if domestic crisis is approaching
– if you don’t agree with the staff on important issues, go to polls for back-up. (The best employee is the one you can blackmail. Besides, a very good “pusher” for your people is their deep understanding that they have to work together to help the President stay in office next term because if the President leaves, everybody leaves)
– use “the carrot and the stick” tactics
– use “pulling by pushing” – give an important job without publicity to those who become too popular
– do as little reading as you can – you have staff for that
– do as little writing as you can – same reason
– involve yourself personally in your staff and Cabinet jobs as little as you can – same reason
– make no minor decisions – same reason
– send back any intelligence or other report if it’s more than one sheet of paper
The Pocket Cabinet
If the bureaucrats are wearing you down, you have the right to fire any Secretary. However, Cabinet members must be approved by Senate, therefore, you have to negotiate with the Senate leaders and party leaders throughout the country. As a result, some positions may go to people you don’t know well and can’t trust. Then if you want to re-organize the Cabinet you have to confront the Congress, because Congress tries to protect the interests of its constituents, who are often the clients of the existing bureaucratic agencies. So, if you plan changes you have to appoint people who share your strategy.
You may also need to offer a position to a group that you need to support in the coming election, or whose help you need; or to help pass legislation (these people will be more loyal to their political benefactors than to you).
Secretaries have disadvantages compared to the staffers as they don’t have easy access to the Oval Office (again, that depends on you). Some of them had little or no contact with you before being appointed. Actually, their task is to win the backing of key interest groups and that’s why you, practically speaking, don’t need Cabinet meetings (if there’s no crisis). If a Cabinet member feels independent (usually, that’s the Secretary of State), don’t fire him/her – substitute him/her by the national security adviser or send him abroad on a regular basis.
The Cabinet members work hard during a crisis only. They prefer to save their plans and suggestions for private conversations with you, because that is what you need them for and they are competing with other Secretaries for your time, support and for funds.
It’s not easy for the President to make government agencies work effectively : first, you have no time, second – they have no competition. Anyway, you must have insiders in all departments, especially in the Justice Department (FBI), CIA and Secret Service firing anybody who’s trying to dig up dirt on you.
Secretary of Defense.
The Secretary of Defense is a very special and unique position for many reasons. This department is regarded a non-political one, defending the United States no matter what (never let him decide, though, what and where US interests are). Military leaders have a lot of friends in Congress who press the administration to accept military demands. Besides, it’s not easy to manage the Pentagon, as you depend on the military for evaluations of the national military capacities; they decide also what kinds of weapons to buy and build. Half of the federal budget goes to Pentagon, making it a major department and that’s the most frustrating aspect of your management.
You have to find compromise between you, Congress, public opinion, interest groups and defense contractors’ lobbyists.
The defense budget affects diplomacy and international relations, because governments worldwide scrutinize it for clues about US global intentions. For example, increases in defense spending, particularly for items such as naval vessels and aircraft, may signal your intention to pursue more aggressive foreign policies, and cuts in defense spending may indicate an effort to scale back on defense commitments.
Hidden Structure
The Cabinet is divided into the inner circle (State, Defense, Treasury, Justice) and outer, less important one (Interior, Agriculture, Commerce, Labor, Health and Human Services, Housing, Transportation, Energy, Education, Veterans Affairs, Homeland Security). While inner Cabinet members are selected more on the basis of personal friendship and loyalty, outer Cabinet members are selected more on the basis of geographical, ethnic or political representation and adopt an advocacy position for their Departments.
The inner Cabinet is divided into two groups:
а) national security group (State and Defense Departments).
b) legal-economic group (Justice and Treasury Departments). The Attorney General usually serves as the president’s attorney and this special responsibility leads to close personal contact with the President. The Secretary of Treasury is very important in domestic monetary and fiscal policies and international trade and currency.
The outer Cabinet is a “domestic” group. Don’t waste your time meeting them – you have enough staffers for that. Sometimes “outer” Secretaries try to build their political base of support within their own bureaucracies. Don’t hesitate to fire and replace any of them if they start to criticize you and behave politically independent, counting on bureaucratic and interest groups’ support.
There’s one (negative for you) thing in common between all Secretaries – self-interest pushes them to protect and expand their departments and then they act more like representatives of their departments to the President then the presidential envoys they were appointed to be (“divided loyalty”).
ATTENTION : Secretaries of State and Defense usually form a coalition against your National Security Adviser. You must be a smart mediator as Commander-in-Chief. These two have weekly meetings, and each of them has a weekly meeting with the DNI (Director of National Intelligence), so you must know from independent sources what they are talking about in case they “forget” to tell you the details. The Defense Secretary meets weekly with the Joint Chiefs, too.
Mind Control
Every day in 2004 we watched the Homeland Security Department "terror alert colors" and very often the threat was "high" or "very high. " With all my 30 years espionage experience I couldn’t understand why they were telling the nation about the threat and producing the multicolor picture on TV. Why? What can ordinary Americans do about that? What happened next made the situation absolutely clear for me and posed one more question for the nation: right after President Bush was re-elected the colors disappeared – why? Again, what happened? Is there no more "terror threat" to America? There is. But there’s mind control, too.
Mind control, which I call mind manipulation or MM, is used to program the "right political behavior" of the nation or "indifferent behavior" (if necessary) without people’s knowing or understanding the procedure.
We are talking here about total illegal social control.
Principles of Mind Manipulation
1) It’s not enough if every single citizen, and the nation as a whole, thinks and behaves your way – it’s much better if they want to behave your way and feel comfortable, and are absolutely sure it’s their own choice and, finally, they become your active supporters.
2) If you want to control the nation and program peoples’ thoughts, you have to control knowledge (information, culture and communication).
3) The political imagination (belief) of the nation has to move in the right direction and has to be accepted as the most comfortable and most acceptable way of political activity: nobody is thinking, nobody is criticizing the President, nobody is making comparisons and drawing conclusions. Everybody believes the American President and hates his enemies.
4) Don’t waste time fighting foreign ideology, take care of ordinary Americans.
5) There is no difference between commercial and political advertising, and MM.
American Propaganda Technology
You need 24/7 effective propaganda to get non-stop public support of your policy — your war for public support does not stop the day you enter the White House — it may stop the day you leave the White House. If your polls go below 40%, the United States effectively has no President.
Use propaganda tricks:
– general (abstract) information on big problem
– information dosage (the less people know — the easier you convince them)
– misinformation (full or partial) presented as news, sensations, rumors
– disorientation – one bit of information contradicts another one
– provocation – information "pushes" people (before you start war)
– information over-dosage – too much information (and people lose interest)
– exaggeration of enemy’s negative sides and promotion of scary data
– distraction of nation’s attention from news that is bad (for you) by publishing sensations and (political) scandals
– stereotype manipulation ("nuclear threat, " "international terror, " etc.
– "shuffle" – all news and facts match President’s political course
– "cocktail" – mix of true and false information
–"facts transportation" from abroad (you buy a foreign reporter and he’s publishing positive information on your politics; then you spread the information through American media)
Remember the principles of mass psychology: people don’t believe the government – they believe the market and the stock exchange; people need statements, not analysis.
MM Technology
1) Create a steadfast American collective will-power: “We want to live forever in the America we live in now” – through the media.
2) Don’t ask people to change their views and beliefs – they have only to change the object of their aggression – “Now we understand who are America's enemies! (the previous President, Republicans).
3) Get people accustomed to accept facts but believe only in the “right” comments – any common sense has to be “switched off. ” This way you create “mass artificial schizophrenia” — people lose the ability to connect statements and facts (notions) and just believe.
Besides, by extreme exaggeration of the enemy’s negative qualities you can install the national schizophrenic fear (of "international terrorism") and people have to accept you, the US President, as a savior. Plus, no matter what, repeat your major statements until people start accepting them without thinking.
4) Divide the nation into “good Americans”(patriots) and “bad Americans”(the “minority).
Make it clear : it’s much better and more comfortable to be “good” than “bad. ” “We aren’t watching good Americans who support the President. The surveillance is for bad Americans and we make their lives and careers uncomfortable. We have to do that because enemies of America may be using them. ” This method is called artificial social selection and its ultimate goal is a total regulation and standardization of the nation.
5) For successful MM, use the combined efforts of popular Democratic American writers, TV and radio anchors, talented publicists and columnists, business and show business celebrities, politicians. Thus, step by step you create the “industry of correct political behavior and correct American thinking. ”
6) Use a combination: statement + image. It reduces the effort needed to understand your message and makes people comfortable with you.
7) Shift all popular TV shows to prime time – Americans don’t have to think about politics after they come home.
Psycho-epidemic
During his first presidential campaign Obama used my strategy of psycho-epidemic.
It's simple – you hypnotize people by permanent repetition of a certain word, like "Change! ", a phrase, a slogan. A crowd, and even a nation,, often behaves like a dog, it's very submissive if there's a strong personality, a strong leader in front of it. Then, the reflex appears – once you see a strong leader, you must listen to him and follow his orders.
Strategic planning
That’s the biggest problem for all administrations.
Strategic planning is the process of making present decisions based on well-calculated future consequences. The basic strategic objective is a decision as to where to concentrate the government efforts this is the essence of strategic planning. The worst example of strategic planning is the war in Iraq.
It is crucial to choose a professional crew and place people in positions where their brains will work effectively and produce quality.
Planning formula:
– design strategy
– amplify and clarify strategy into policy
– organize a team
– guide execution
– make final strategic decision
A. Regular Planning Model:
subject, concept, idea definition of objectives
design of innovative options and debate
exploration of concepts, claims and possibilities
development of program outlines
establishment of expected performance criteria and indications
information gathering
integration of ideological elements
assignment of executive responsibility
scheduling
analysis and experiment
experiment evaluation, examination of likely consequences
comparison of expected and actual performance levels
determination of costs
prognosis
strategic decision
B. Express planning: information interpretation, projects design, choice of a project, decision
C. Regular (math) model:
Negotiations planning (example): pressure, compromise, tricks, break.
Let’s evaluate "pressure": negative international reaction /-1/, breakdown /-1/, positive effect /+1/. Score: -2+1=-1 Conclusion: no pressure should be used.
D. Expertise model.
Government crisis (example): poor planning- wrong decisions- wrong actions- wrong execution- opposition activation- mass protests- coup
E. Scale model.
Risk factors: Risk levels:
Intenationalsanctions : medium
High inflation rise : medium to high
High unemployment : medium to high
Low public support level(low polls) : medium
Presidential decision making
1. Decision making is a multiple choice process.
2. Any decision involves political risk.
3. If you can’t make a decision, you need more information.
4. Be optimistic, but remain realistic.
5. Give yourself a deadline.
6. No brainstorming chaos.
7. There are two kinds of decisions: irreversible and reversible. Better know which kind you are facing.
Here’s the process:
a) Identify the problem
b) Analyze the problem — what are the facts?
c) Evaluate options – what are the pros and cons? what can go wrong?
d) Identify choices – which alternative is the best?
e) Implement plans – what action needs to be taken?
As the world #1 leader you have to know that this world is being ruled not by you but by 11 financial corporations : Barclays, Goldman Sachs, Capital Group Companies, FMR Corp, AXA, State Street Corp, JP Morgan Chase, Legal & General Group, Vanguard Group, UBS AG, Merrill Lynch & Co Inc.
Bonus
Psychological Modeling of a President (Strategic Intelligence Method)
Intelligence services worldwide watch political leaders during public appearances, trying to calculate their physical and mental health judging by their look and behavior. In the US they also evaluate the executives and staffers who surround the President at official meetings to calculate what’s going on in the White House.
They look at:
– a very detailed biography
– personal needs, interests, philosophy
– political views
– intelligence, will-power, character, abilities
– behavior in crisis situations
– compromising facts and possible methods of influence
– personal, political and big business VIP connections
– financial situation
– administration and team
– political opposition and President
– Congress
Domestic headache
You can’t separate domestic and foreign policies because they are married to the same ugly guy – the budget deficit.
Domestic policy rests on three legs: education, health and environment. Americans will never support reduced funding for education, Social Security and Medicare (Medicaid) cuts and weakened environmental-protection laws. But I strongly advise you – don’t bother trying to emulate Europe and the British Commonwealth by providing health care for all – the privately insured middle class (your voting majority) won’t stand for it. If you don’t believe me, go to the polls.
Now, are you a challenger in politics? If "yes, " strengthen your political positions in Washington, DC first, then start some reforms. Before you start a reform you have to win the information war with your opponents and get public support. A reform is always a venture; the process may start taking on momentum and you won’t be able to stop it. You had better continue old reforms using a new tactic because new reforms bring new problems, new enemies and new mistakes, and big economic mistakes bring you an economic crises.
Dealing with big business
1. Big organized money moves big political machines, big political machines move big lobbies, big lobbies move the President.
2. The President is an investment.
3. A group that rules the economy rules the White House.
4. A new political course comes not with a new President, but a change of big business’ global financial interests.
5. Follow 3 "golden rules":
– protect big investments
– help to promote
– don’t interfere
6. If the government doesn’t meet the needs of big business, it forms a new one of its own (something like a President’s Council). This usually happens when the President can’t provide financial stability and super-profits. Besides, big business has much more important foreign connections than the government.
7. Big business is:
a) money
b) political and economic control
8. Any political action gets an economic (big business) reaction.
In terms of partisan politics, Republicans are considered to be more sympathetic to big business interests while traditionally Democrats get electoral and financial support from organized labor. Forget about antitrust policy business has become more global and efforts to enforce antitrust policies have proven deficient and are threats to national security.
Managing the economy
1. Regulate spending, taxation, monetary policy and foreign trade whic has to be under strict political control – you have the right to propose legislation and veto any legislation you think incorrect. Keep in mind that Americans always insist on reducing government spending on foreign aid and space exploration, and they naturally hate any rise in taxes.
2. State and local governments, both through national associations like the US Conference of Mayors and Congress Members, always press the government to get more federal funds even at the expense of inflationary budget deficits.
3. Keep unemployment low and prices stable – these two factors are politically dangerous and failure here can bring a free-fall in approval ratings.
4. Take credit for economic growth, price stability and low unemployment even if you have nothing to do with it.
Still have problems? Try international initiatives.
There are four inevitable factors that will limit your control over the economy:
1) You must share power with Congress — you can’t levy taxes or appropriate money all by yourself;
2) The theoretical nature of the science of economics — no single economic theory has ever explained the behavior of the economy in the future;
3) The imprecision of economic information. Economic statistics and indicators do not measure the immediate conditions of the economy, but rather the conditions that prevailed between one and three months ago, depending on the particular economic statistics. Consequently, if you take action on the basis of incoming economic information you may be reacting to a problem that no longer exists or that is much worse than believed.
4) There are forces outside the reach of the federal government, like international factors (oil prices and foreign trade policies), state and local governments economic decisions and mistakes, big business decisions that affect employment, inflation, the trade deficit and public opinion — which is always against cutting social programs.
Budget deficit
A large budget deficit is a headache and has extremely negative effects on the economy:
1. It limits the government’s flexibility to fight a possible recession; that requires tax cuts and deficit spending, which would exacerbate the debt problem. Since tax revenues fall during a recession and unemployment insurance and welfare payments rise, the budget would be under further strain precisely when deficit spending would be needed to pull the economy up.
2. It reduces the amount of funds available for achieving the nation’s social and defense goals, because interest must be paid on the national debt.
3. It can threaten the economy by "crowding out" corporate and private borrowers from the credit market. Because the government must borrow heavily to finance its deficit, it competes with business and individuals to borrow funds. The increased competition forces interest rates higher, causing loans (including mortgages) to become more expensive. As a result, business can afford to purchase less plant and equipment to expand and modernize their operations and fewer consumers can afford to finance purchases of expensive items, such as houses and cars. The resulting reduction in demand threatens economic growth.
4. The US budget deficit has become so large that domestic savings no longer can provide enough capital to service the debt. Consequently, the government must borrow from foreign sources to make up the difference. This makes us dependent on foreign investors and raises the possibility of a "stabilization crisis, " which can occur if foreign investors lose confidence in the dollar and liquidate their US investments. Such a crisis could cause the dollar to plummet and interest and inflation to rapidly accelerate.
Crisis
Crisis means that your government as a system is exhausted and it’s unable to rule the nation and resources effectively in an extreme situation, including economic, natural catastrophes and war. A crisis has three stages – before the crisis, when the first signs appear; crisis development until culmination; catastrophe followed by impeachment. A crisis could be "programmed" at the very beginning of your term (mistakes in political and economic courses, inexperienced personnel, faulty planning) or it can appear later (too many mistakes, change of political environment, shifts in the economic or international situation). Crisis management includes pre-crisis management and handling of the situation. You must be ready not only for a government crisis but also for sudden military attack, mass riots and natural disasters.
International trade is an important component of national security. Our "friends" (NATO members, Saudi Arabia and Japan) favor a dollar (that is neither overvalued nor undervalued) and a healthy US economy with relatively full employment and low inflation rate. If the dollar is weak, the value of much of their international currency reserves declines and their goods are less competitive in the US market. If the dollar is too strong, their investment capital migrates to the US and the high competitiveness of their products in the US market threatens to provoke calls for trade restrictions. If unemployment in the US rises, the major market for their goods declines. If interest rates are higher in the US than in Europe or Japan, investment capital moves to our country. Consequently, foreign governments press the United States to keep the exchange value of the dollar from fluctuating widely and to hold interest rates steady.
Congress management
It’s much more simple that you think.
1. A Congressional session is a waste of federal time and money – you don’t need debates because Congressional staffers can do all the technical work and they can negotiate between themselves and balance positions. Senators and Congressmen don’t even have to come to Washington – they can vote from their local offices. So these people can spend their time helping thousands of constituents.
2. The President is dependent on Congressional cooperation to carry out the executive responsibilities of the Office because Congress has to authorize government programs, establish administrative agencies to implement the problems and funds to finance them.
ATTENTION : Executive Order might lower this dependence a little bit.
3. It’s important if President belongs to the party with a majority in the House and Senate. But if your party loses the majority in Congress, you have to work out new political strategy yourself.
4. President’s prestige (popular support or political capital) affects Congressional response to his politics.
5. Influence in Congress is courted only for long periods of service; a Senator with 30 years in office (like late Edward Kennedy) has considerably more power than a Senator in his first or second term. This causes the electorate to increasingly favor incumbents, as dislodging one’s Congressman or Senator after 30 years, even if the candidate or his party have become unpopular, can be viewed as hurting one’s district financially. It is often thought that a freshman would be less able to bring home federal money for his state or district.
6. For most Senators, the Senate is a platform for Presidential election campaign. Senators who openly express presidential ambitions are better able to gain media exposure and to establish careers as spokespersons for large national constituencies.
7. The first act of a newly elected Representative is to maneuver for election to the Senate. Why? First, they enjoy their position, power and money for six years non-stop. Second, there are only a hundred Senators and the publicity is much, much greater. But Representatives have a much better chance to be reelected.
8. Congress rejects two thirds of President’s proposals.
9. Senators are always looking for a BBD (bigger, better deal) and often shift from one committee to another (a good choice is those dealing with taxes, budget, energy, commerce).
10. Bills to benefit big business move smoothly. (Congress doesn’t like the poor — they don’t contribute, sorry). To gain majority support for big business legislation members have a special trick – log rolling, when factions combine efforts.
11. Senators don’t depend on the people – they depend on the media.
12. If a Senator is blocking the President’s proposal, he wants to get the President’s attention.
13. When Senators want to bury issues, they create committees.
14. The Senate is a small structure and personal relations between Senators are extremely important.
15. Senators have no incentive to study the details of most pieces of legislation and their decision is simplified by quickly checking how key colleagues have voted or intend to vote.
16. To have power a Senator has to object: much of the Senate work is done by unanimous consent and if you object you’ll be approached for sure by some influential people including other Senators, Secretaries, President’s aides or the President himself. They’ll try to press, blackmail or buy you – and that means you’ve got a piece of the power pie.
17. Senators avoid responsibility in economic policy.
18. Congress loves the military because military contracts are very lucrative for Congressional districts.
19. Senior Senators teach “newcomers” to vote against any reform which is a threat to their stability.
20. A Senator has real influence on legislation only if he has professional staff in charge of the projects.
21. Senators are afraid to vote against a defense budget increase because then they may be accused of a lack of patriotism.
22. Republicans and Democrats are not really enemies, here, though both sides are always looking for a “traitor” or “insider” in the other camp.
23. The President must have “insiders” in the Senate, because the other party could prepare secretly and then launch officially some investigation against you or the members of your Administration.
24. A legislator does exactly what his voters want him to do – stealing federal money from other states and districts, because for him the most important thing is numbers — polls in his state showing how many people approve his activity. His donors watch these numbers too and estimate their investment and the necessity to support re-election.
25. Every member of Congress has a so-called “split personality” – a “Hill style” while working on Capitol Hill and a “home style” while back in the state or district with the voters.
26. A Senator makes a decision only after thinking about what it means in terms of the re-election money that will come to him or to his opponents. His voting decisions depend on his party membership, constituency pressures, state and regional loyalty ideology, interest groups’ influence. His stubbornness comes from the fact that he does not want to be seen by his constituents as a “rubber stamp” for President’s decisions, especially when the bill in question benefits a Senator’s state. (And the hidden problem is – you want to move fast, especially during the first year while your personal popularity is high – but for the Congress speed is not important).
27. Sooner or later every member of Congress starts playing the “pork barrel” game. It’s nothing else but a diversion of federal funds to projects and places not out of national need but to enhance a member’s chances of re-election in his district (military projects, federal buildings, highways construction projects). So be ready for a “Christmas gift” when these fellows add pork barrel amendments to appropriations bills you are about to sign. They often wait until late in each session to pass critical spending bills, which narrows your range of possible responses because a veto may not be feasible if Congress has adjourned and the funds needed to run the federal government are contained in the legislation.
28. In Congress a small percentage of bills (about 500 out of 10, 000) actually become law because many bills are introduced merely to get favorable press. The strategy is especially effective if the legislation is “tied” to the headlines of the day (mass murders, natural disasters, ethnic riots etc. ).
29. In the Senate it’s easier for a minority to block the bill than for a majority to pass it: a 60-vote majority is needed to force a final vote on the bill, while only 41 votes are needed to continue debate and delay a vote.
30. The minority can hold the majority responsible as the party in power for whatever legislation does or does not emerge from the Senate. But both parties prefer to be the party in power in the Senate – all Senate legislation begins in the committees, whose membership and chairmanship are controlled by the party in power. Besides, each chairman has power in terms of controlling the committee budgets and deciding which hearings will be held and which legislation he will allow to be released to the Senate floor for a vote. He can also “lock up the bill” in committee until it dies. Perfect!
How to Control the Congress
The President can propose legislation, but Congress is not required to pass any of the administration’s bills. But you know already that Senators and Representatives need re-election more than anything else. So you can go with indirect influence through appeals to the public; this is a confrontation and direct challenge to Congressional authority. You can also enlist the support of interest groups or direct influence through favors and personal involvement in the legislative process. (Get public support for a proposal before it’s discussed with the Congress. )
And don’t hesitate to start a national debate — you have enough media attention for that.
You also have an independent tool, presidential power in the form of an executive order. You can give favors directly to members of Congress or to influential people in their constituency, or the favor may be of benefit to the constituency itself:
– appointments with the President and other high-ranking officials
– federal grants to recipients in the constituency, government contracts with local companies, the deposit of federal funds in banks, grants to local government and educational institutions
– support of projects (military installations, research and administrative facilities, public works such as buildings, dams and navigational improvements to rivers and harbors, etc. )
– recommendations for the US district court judges, attorneys, marshals, etc.
– campaign assistance (cash contributions from the party’s national committee invitations to bill-signing ceremonies, White House parties or to accompany President on trips
– bargaining and arm-twisting (pressure and threats to lose the projects).
Tools
1. The Congressional Relations Office. Used for:
– intense lobbying to form Congressional coalitions if the opposition controls one or both houses
– intelligence gathering (of policy preferences — centralized headcounts reveal the voting intentions on a particular bill and constituency concerns of individual members)
– representation
– creating “inner coalitions”
– coordination of executive branch legislative activity (monitoring and tracking bills, controlling departments’ staff appointments, collaborating with departments’ liaison offices)
Attention! Senators and Congressmen have to trust your people, who must keep their mouths shut, otherwise there will be no business. Anyway, watch these people — a Senator can call one of your assistants and if they hear “no, ” he will try to reach somebody else until he gets “Yes, the President will see you. ” Don’t let this happen – if it’s “no, ” it has to be everybody’s “no. ” There has to be no difference between personal views of your adviser and your official views.
2. Congressional Relations personnel of various executive Departments are a conduit. Talk to the Secretaries and explain to them that they have to give the Director of Congressional Relations their best people.
3. The White House interest groups liaison staff (office of public liaison)
4. Veto. Threatened with a veto, Senators often seek compromise.
Congress has its ways to undermine your vetoes or threats of vetoes. Because you can’t veto parts of a bill, they load up major legislation with amendments on a completely different subject (“riders”) that they know the President must accept. (Presidents who vetoed the most bills: Franklin Roosevelt – 635, Harry Truman – 250, Dwight Eisenhower – 181, Ronald Reagan – 78, Gerald Ford – 66).
5. Executive agreement. It permits the President to enter into open or secret agreements with a foreign government without any advice or consent of the Senate. There are two categories of executive agreements:
а) presidential agreements made solely on the basis of the constitutional authority of the President and under his sole power to faithfully execute the laws (or under his diplomatic or Commander-in-Chief powers). President needs to report secret agreement to the Foreign Relations Committees of the two houses no later than 60 days after such agreement has entered into force. Congress has no authority to disapprove it.
b) congressional-executive agreements, which cover all international agreements entered into under the combined authority of the President and Congress.
Finally, this is what you can do with a bill:
– sign the bill (the bill becomes a law)
– do nothing (the bill becomes a law in ten days)
– veto the bill (the bill does not become a law)
– pocket veto the bill (hold the bill until Congress is no longer in session, and the bill does not become a law)
Chapter 4. Foreign policy
“Golden rules”
1. International treaties have to be negotiated by diplomats prior to endorsement by presidents.
2. The information gathered by spies plays an increasingly role in diplomacy (arms-control treaties would be impossible without the power of reconnaissance satellites and agents to monitor compliance).
3. If you start war, it does not mean you failed diplomacy, it means military decision is much more profitable.
4. Make it clear to foreign leaders right away whether you are or you are not going to follow the previous President’s foreign policy (after consultations with big business). If you are not going to follow it, design a doctrine of your own (it’s a strategy that is the recognized approach or policy of the US government.
5. National security is your top priority and is the “king’s job” because actually you have no domestic political obstacles to your foreign policy (if it’s a question of war), so you are a chief decision maker there. (The CIA Director has to be excluded from from this process — you don’t need him. Besides, the CIA even today, no matter how hard I tried to educate the Agency, remains the worst of the worst and is not to be reformed — it has to be abolished. We have to transfer political intelligence functions to Pentagon. National security is designed to protect the United States and the vital interests (investments) of big business and to promote American values in a world of rivals, and the CIA, through all 60 years of its history, has proved to be absolutely unsuitable for the job).
6. Any country has to be involved in the sphere of our strategic interests if it has a strategic geographic position, significant sources of raw materials, a well-developed transportation system, or could be used as a military base. The strategic policy of any country rotates around the USA and if not — that means a certain President is waiting for greater incentives to come on board. Against target countries, don’t hesitate to use the strategies of pre-emptive war, post-war (post-crisis) reconstruction, and nation building (which means erasing national identity and supplanting it by liberal values).
With China’s growth, the Cold War is back with a vengeance, so we are back to secret deals based on spheres of influence — but that’s a temporary strategy.
7. You can’t always do what you want without help – you are dependent on other world leaders, Congressional positions and international public opinion. Ask the Senate to help you sometimes – believe me, they’ll be happy and proud to do so.
8. Create super-profitable conditions for big business by political penetration worldwide. Big money men start investing abroad when they find a safe environment — law and order. The more they invest the more political power they get (international corporations is the most important element of international system ; the other two are governments and non-governmental organizations).
9. Use big investors to ruin other national economies and governments by withdrawing finances when the economic situation is worsening. As soon as the country opens its financial markets, it increases its dependence on global economic processes that it cannot control; and a financial crisis can easily be staged. Conversely, other countries’ access to the US markets is a powerful economic and political tool.
10. Use my “controlled chaos strategy”. My idea to make the US economic and financial markets the most attractive for investors by provoking unstable situations in other countries and regions.
11. Send troops or work through military intelligence (not the CIA) to wherever you perceive a threat to the US investments.
12. Use pressure everywhere – strategic nuclear missiles are still the most powerful blackmail tool. Remember, if you are dealing with Russia or China, they will look not only for agreement, but for advantages.
13. Use “personal diplomacy” – phone calls to foreign leaders (every planned phone call has to go through the National Security Adviser and be well prepared, like a serious negotiation). Most important are phone calls to our allies — NATO members. Don’t forget to wish happy birthday to the leaders in person!
14. Use “informal diplomacy” – recruit politicians in other nations who might be able to give informal access to a country’s leadership. In some situations, such as between USA and China diplomacy is done through semi-formal channels using interlocutors such as academic members or think tanks. This occurs in situations when presidents wish to express intentions or to suggest methods of resolving a diplomatic situation, but do not wish to express a formal position.
15. Don’t hesitate to use summits as a tool, because:
–if you meet a foreign leader in person, you can reduce tensions and clarify national interests.
–personal relationship may lead to improved relations between nations.
–summits allow you to focus national attention on specific issues.
–presidents engaging in personal diplomacy are much more capable than career diplomatic bureaucrats of understanding the domestic policy consequences of diplomatic actions.
–summit negotiations can yield quick results, since discussions are between leaders with the power of decision rather than between representatives who must receive instructions, make reports and rely new proposals.
–diplomatic impasses may be overcome at summits by shifts in policy that only top leaders are empowered to make.
–if presidents desire an international forum for their diplomatic policies, a summit meeting can provide one.
–successful summits can enhance the image of the President and the United States
16. If you’re ready to fight for national interests, forget about human rights — you can always blame infractions on the other side.
17. Isolation is the greatest enemy to information.
18. There’s no sense in applying sanctions if big business isn’t interested.
19. Economic and hence, political progress for any country affects the USA through economic competition that threatens the market and jobs.
20. Any initiative is risky if it’s about unstable region, but you lose popularity fast if you are perceived as indecisive or weak in foreign policy.
21. Any trip abroad has to convey a strong message.
22. Direct military intrusion indicates weakness in your foreign policy. If it’s inescapable, involve as many allies as you can.
23. Don’t touch our military bases abroad!
24. Big debts open markets. No matter what, open national markets world-wide for American big business and remember – the markets, not Presidents, rule the world.
25. Tie your allies to international economic projects and make them pay most of the expenses.
26. Never talk about money in public — talk about democracy, human rights, liberal values and disarmament – people like it.
27. Move forward – transform Americans’ national and patriotic feelings into nationalistic ones (follow the French model) to get total support of your policy (see “Mind Control”).
28. Don’t pay too much attention to the CIA – all they have to do is to support you with appropriate information to justify your strategic political decisions – and nothing else.
29. Ignore the UN – Secretary General has no real power, but you can take advantage of such a thing as the UN peace-keeping if it corresponds with your interests – the US economic costs could be minimized. Besides, UN peacekeeping can promote a spirit of international accountability in solving a certain regional problem. Don’t forget to explain your strategy to the Congress – they don’t like the UN either. On the other hand, you have to manage an international crisis, if it threatens our national interests (start with strategic planning, check national security system for the adequate response, use propaganda to get domestic and international support, consult with big business and allies, start crisis negotiations if possible, use diplomacy (see below) and force or threat of force).
30. To reach global leadership you must have enough resources, national support and a well-calculated strategy (see also “Strategic planning”). As you already know, the US budget is financed by foreign lending. When the dollar goes down in foreign exchange markets, it’s supported by foreign central banks and you’re OK as long as Japan, Saudi Arabia and Germany have an interest in propping up the American economy and do not raise the price for financing America’s debt. The worst situation would be to lose support both at home and abroad
Decision making
– assessment of the international and domestic political environment
– goal setting. We have multiple foreign policy goals, and we must determine which goal is effected by the international and domestic political environment
– determination of policy options
– decision making action
– implementation of chosen policy option
World Domination
Securing the top position requires :
– economic domination
– military power – pre-emptive war or blackmail by war (seeking domination requires an inevitable increase in the military budget)
– a cultural and media invasion
– special operations to influence or neutralize leaders with negative attitude
Modern mechanism of world domination
1. If the country does not accept American rules of the game, we start a "velvet" or "colored revolution.
2. We replace the government by pro-American regime.
3. If the government resists, we start the US and NATO military operation and help the anti-government organizations to overthrow the government.
Strategies used
1. Destabilization strategy based on terrorism – you kill political leaders and civil population, blow up government buildings and blame the opposition.
2. Stabilization strategy – first, "terrorists" destabilize the situation in the country and then the US and NATO troops come to "stabilize' it.
3. "New order" or a "controlled chaos” strategy – American “new world order” to be established through the international chaos, permanent wars, civil wars and revolutions.
My definition :
"Controlled chaos” strategy –
geopolitical re-division of the world by provoking riots, revolutions, civil wars and overthrowing regimes in independent from USA sovereign states to keep the U. S. world hegemony. Political, national, religious and social conflicts in target countries have to be permanent. The strategy is being covered by a "struggle against international terrorism". The operation is preceded by information war against the target regime and backed by NATO forces if necessary.
Most important targets of the 21st century – Russia and China. That’s the reason we occupy Afghanistan. We have to circle China with our military bases in Central Asia.
4. Global energy control strategy – the US control of major oil regions and gas fields.
To keep America on top, we would have to prevent cooperation and coalitions between: China and Africa; Shi’ia and Sunni Muslims; Germany and France; Venezuela and Cuba. Their trade agreements and alliances will change the geopolitical situation.
In most important world regions keep the balance by supporting the country which follows the leader:
In Europe – support Britain to balance Germany. You rule Europe if you rule the Persian Gulf. You rule the world if you rule Europe, and that’s why you have to keep NATO by all means to block the military independence of Europe (Germany).
In East Asia – support Japan, Russia and Taiwan to balance China.
In South Asia support Pakistan to balance India.
In Latin America – support Argentina to balance Brazil.
Diplomacy secrets
1. Use secret visits (send the National Security Adviser) if the international problem is complex and important – in this way you don’t depend on media and public opinion. Afterwards you can talk, if it was a success.
2. If presidents like to drink with each other, they are ready to deal with each other.
3. Avoid negotiating on major issues at the end of the day, when your energy is low.
4. Negotiate smart, watch your initiatives. The more you tell about your position, the less your partner will tell you about himself, and the higher price you’ll pay. Diplomacy is all about money and the essence of any negotiations is the price range.
5. Any information should be exchanged as a part of a compromise and not merely given away.
6. Always talk less than necessary. Concentrate on facts and never tell other person about feelings (or your family and medical problems). Don’t interrupt others, try to understand what they really want and if they try to manipulate you. Also, resist giving in to interruptions until you have completed your thoughts – “Just a moment, I haven’t finished”. Use Taleyran approximation – if it’s difficult for you to speak up, try to make just one diplomatic statement. If they press you, insist on moving this questions to experts. And use indirect language such as “It looks like” or “You see situation from a very special angle”.
7. No negative emotions, they indicate weak nerves. Never take things personally.
8. Stop self-limiting behaviors, such as smiling too much, nodding too much, tilting your head or dropping your eyes in response to other person’s gaze. Speak normal conversational volume, don’t scream and don’t whisper, either, as you won’t be taken seriously.
9. Take a problem-solving approach to conflict, and try to see the other person as your collaborator rather than your opposition. You’d better postpone negotiations than allow them to break down.
10. Fix all questions, don’t be in a rush to answer any of them.
11. The slower you talk, the more confident you are.
12. Never ask straight questions, it’s a primitive approach.
13. It’s important to know what questions and when to ask.
Start with an “invitation” question that does not need a definite answer but opens up the discussion, like: “No matter what reporters say, we’ll start negotiating for arms control. ” Proceed with “intelligence gathering” questions, like: “Are you going to abide by our last agreement on the withdrawal of military forces or do we have other options? ” Go to “expertise” questions, like: “It’s 500 missiles, right? ”
There’s a difference between expertise and straight questions – straight question are like: “Will you sign the treaty? ” and these have to be avoided because you’ll get no straight answer right away. Finish with a closing question, like: “I think that’s what we intend to sign? Next time we can start from here. ” Or you can press your partner: “Let’s not lose this last opportunity, eh? ”
14. Explain your negative attitude in a smart way: give half the information and continue, depending on your partner’s reaction. If you can’t accept his proposal, tell him that the experts may look into it again and come to agreement. If your partner is not a complete idiot he’ll understand his proposal is unacceptable (because the experts have already done all they could). But if he is an idiot, he’ll agree to “kill” his proposals by passing them to the experts.
15. You start to lose momentum if you start to defend yourself. Stop (postpone) negotiations the moment you start to lose or you could end up in a total failure and that could be used by opposition back home.
16. If you bring ideology – try to win. If you bring national interests, try to find compromise. Be flexible – that’s strength, not weakness.
17. Don’t make aggressive statements for the media, no matter what.
18. Respect is half a victory, but you usually win when your partner is scared. Avoid open confrontation and respond to personal attacks with humor.
19. Watch the military experts – they are always ready to “push” you. No arms agreement can win ratification without backing from Joint Chiefs, because Congress needs and trusts their expertise, and their disapproval is a strong tool against you in case you ignore their advice. So, think three times before you appoint Joint Chiefs.
20. Take negotiations on the trade deficit very seriously – they often take you nowhere and have zero results as your partner wants you to change your attitude to him completely as well as your international economic policy, while you expect the same favor from him. You can influence one partner but you can’t very easily influence the international system.
21. After you come back home do some positive advertising through the media – in such a way you influence other presidents and future negotiations. If the negotiations resulted in a treaty, “sell” it to the Senate for approval.
22. Negotiation no-nos:
– don’t be confused if your partner threatens you – that means he needs your cooperation. Don’t enter into negotiation right away with high demands.
– don’t touch the toughest issues first. Don’t assume – that’s a sign of weakness.
– don’t hesitate to pause or take a break.
– never say “no” to your partner’s ideas – rather, pack them up in one “package” with your proposals.
Diplomatic tricks
Tricks in diplomacy are usually used to distract your hard working team, shift the emphasis of the negotiation in order to shape the deal on terms of your adversary or manipulate your team into closing negotiation and accept terms you don’t really like. And the tricks are:
“Leap” – your adversary is losing and starts “jumping” from one point to another
“Pile” – your adversary “piles up” problems, tries to provoke a chaotic discussion or stop negotiations
“Empty chair” – a day or two before negotiations start your adversary informs you that he’s not ready yet, trying to press you (or he wants to change location)
“Diplomatic illness” – the practice of feigning illness to avoid participation in negotiations and at the same time to avoid giving formal offense.
“Deaf” – your adversary keeps asking questions instead of answering yours
“Provocation” – your adversary doubts your team’s professional level and your ability to negotiate. Don’t go crazy.
“Busy guy” – your adversary breaks negotiation for an hour or two pretending he has to do some very important business (or that he got a very important call).
“Mirror” – it’s a “programming” trick. The technology is simple: you try to “mirror” your adversary’s style and behavior, adopt a similar posture, use his gestures, and follow the speed of his speech. First, he will like it subconsciously and will be more open to you. Second, you’ll understand better his way of thinking.
“Sandwich” – pressure (often – military) – negotiations – pressure
“Show” – using certain arguments your adversary appeals to your emotions
“Circle” – a very sophisticated trick: your adversary tries to “push” his proposal in different variants and finally comes back to his initial variant, trying to convince you that’s the best choice
“Carrot and stick” – threat (blackmail) plus promises (money). The guy could blackmail you also by demanding to set a deadline
“Student” – your adversary talks too much about the details, asking a lot of minor questions, trying to make you nervous and make mistakes
“Donkey” – your adversary declines the offer to speak first
“Ball” – encourage your adversary if he’s looking for “global decisions” and he’ll do a lot of minor favors
“Rubber” – delay, if you can’t predict the result, and press your adversary by delaying the answer
“Last train” – you can press your adversary by an ultimatum right before negotiations are over, if he really is interested in some result. “Spice” the ultimatum with some important reasons and give your adversary a choice of variants.
You can also leak opposing demands to the media (be careful with this one. Do not betray diplomatic trust by talking about secret deals or demands that actually have been mentioned). You may also escalate your demands during negotiation and manipulate public opinion to line up behind your demands.
Negotiations Procedure
I. Preparation
1. Write a plan.
2. Define your objectives.
3. Identify issues that are open to compromise and those that are not.
4. Conduct research for information to support your objectives and have information to undermine your partner’s position; think what information is available to your partner (State and Defense Departments will help you with that; not the CIA).
5. Find out how your partner negotiates with other leaders (he might have a “rabbit in a hat” for you).
6. Consult with members of a previous negotiating team about his style, strong and weak points.
7. Check the current balance of power. Attention: if you start multilateral negotiation you have to know what are the conflicts or allegiances between other partners. If they are divided into groups, identify who has the power to make a decision on behalf of a group.
8. Use game theory if you are intending to cooperate. Game theory is a theoretical analysis of the decision-making process taken by two or more players who are in conflict. You must actually estimate any possible strategies of the players who have to make decisions without knowledge of what other players are planning. Each player’s strategy, once undertaken, will affect the others. Game theory is often illustrated by the “prisoners dilemma” paradigm. It supposes that two men have been arrested on a suspicion of committing a crime together and are being held in separate cells. There is not enough evidence to prosecute unless one confesses and implicates the other. Both of them know this but cannot talk to each other. The dilemma is that the best outcome, not being convicted, is only available if they each trust the other not to implicate him. If X decides to trust Y, but Y fears X may not be trustworthy, Y may confess to get a lesser sentence; X then gets a worse one. The best solution to this dilemma is for both to cooperate, to minimize the worst that can happen, rather than trying for the outcome that is maximum. This is called the minimax strategy and it’s classified as being the most probable outcome.
II. Conducting negotiations
Never conduct negotiations before 10 a. m. or after 4 p. m.
First of all, you have to decide whether you want to speak first or to respond to your partner’s proposal. There’s an advantage in letting your partner make the opening proposal as it might be much more beneficial for you than you suspect.
Then:
a) put forward a proposal (with as little emotion as possible). You have to make your initial offer-demand high and compromise from that point onward. Your partner will understand perfectly well it’s too much, so make your initial demand greater than you expect to receive, and offer less than you are expected to give. (For the same reason feel free to reject the first proposal received. ) While talking further, leave yourself room for maneuvering, presenting your proposals, and don’t try to pin down your partner to a fixed position too soon, because he needs room to maneuver, too. Make a final offer when the atmosphere is most cooperative.
b) respond to proposals in a smart way (again, no emotions). Never take the first offer – if you take it, your adversary may feel there is something wrong with it or he didn’t get the best deal. Capture any similarities on both sides. Don’t hesitate to make conditional counter-offers: “If you do this, we’ll do that. ” Cut the unexpected introduction of new issues and follow strictly a concise step-by-step agenda. Probe your partner’s attitudes: “What would you say if we both lower our demands? ” but indicate that every concession you make is a major loss to you. Ask as many questions as you want – the more information you have, the more you control negotiation. To think over and re-design your strategy, ask for a break as many times as it’s acceptable. Summarize your partner’s proposals.
c) move towards a bargain. You must know perfectly well the response to each of your points before you open your mouth. If your aides can’t help you, you have the wrong aides and you even might be a wrong president. Offer the lowest price first, as you may not need to go any further. Negotiate a “package, ” don’t concentrate on one demand and link other, smaller demands to it. While making a final offer look at the other party and check the body language (see below), your team members must confirm by body language that this is your final offer. It’s OK to press the partner by emphasizing the need to reach agreement, like: “We know our nations are waiting to see the treaty signed. ” (If your partner looks at his watch, it means he wants to end the talk. ) If you see you are approaching a dead end, ask your partner to talk off the record, in private, but if you talk in private, you have to keep your word no matter what.
Sometimes negotiations (as in the Israel-Palestine case) run into serious problems and breakdowns. Strong diplomats never say “never” and never leave forever, and always are ready to come back and agree right away on new dates to continue talks, as though a breakdown is just one more pressure trick. The best thing to do is to re-establish communications as soon as possible and you have to do this through your team member who has good connections and influence with other party. Act fast, especially if the consequences of “no deal” would be worse than the last deal that was on the table. If the situation is not improving, you have nothing else but to use a mediator. I do not recommend you to take responsibility as mediator or to use a mediator for your diplomatic needs. International experience shows that these old and “experienced” people usually make the situation worse, like bringing in a lawyer — even if the situation looks better for the next couple of years. But if you have no choice and your partner, and your aides insist on using a mediator to resolve the situation you have to think it over … and agree.
Mediation is the process in which deadlocked parties consider the suggestions of a third party, agreed upon in advance, but are not bound to accept the mediator’s recommendations. The mediator works as a referee between the negotiating parties and tries to find common ground among their agendas. Once some common ground is established, the mediator can begin to look for mutually acceptable ways out of the deadlock. A mediator between presidents has to be a president himself, very influential, and well informed on the situation to be able to make effective recommendations.
He has to:
a) consider the situation from all angles
b) help both parties to understand each other better
c) help the parties to create new approaches
d) suggest a solution, give alternatives
But if the two sides’ demands are too far apart, no outside party can bring them together at all. ( Often a mediator has to make multiple trips between two parties, who do not talk directly, and it’s called shuttle diplomacy. Usually, two parties do not formally recognize each other, but still want to negotiate. The term became widespread following Henry Kissinger’s term as National Security Adviser and then, as the United States Secretary of State (in 1973-1977), when he participated in shuttle diplomacy in the Middle East and China).
III. Closing negotiation
That’s the most important part, a final mutual agreement or disagreement, a test for your foreign policy making strategy and tactics and personally for you, your power and your image. Any treaty you sign with foreign leaders, if it meets American interests, is not your personal success, but that of the nation. There are three options:
a) the agreement with all conditions is acceptable to both parties
b) the agreement is acceptable to one party only
c) the agreement is unacceptable for both parties
Diplomatic Double Talk
Statement Meaning
We are disappointed. We got nothing.
Situation disturbs us. It’s unacceptable.
There are still differences between There are huge differences.
our approaches.
We can’t accept this deal. This means trouble.
We reserve the right to use any means
to prevent further worsening of the situation. This means war.
Discussion helped us to understand each
other better. We’ve wasted our time.
We don’t understand your attitude. Stop it immediately.
I’m trying to understand your position. Understand me too, idiot!
If I’ve understood you correctly, you don’t agree. Do you have any other option?
We’ll pay a very high price if we don’t
reach agreement. Yes, that’s a threat!
Chapter 5. Espionage management
Spy Code
1. No mercy, no ideology, no emotions.
2. Intuition is nothing but the ability to watch and analyze.
3. No evidence is evidence in itself.
4. Distrust is a mother of security.
5. Never look as if you are sizing up the person – that’s a sign that gives away cops and spies.
6. Don’t start first if you don’t know the rules.
7. The way you act is the way you think – behavior is a system of codes (information) which could be calculated by the enemy. Watch your face – that’s a shop window.
8. Think fast, talk slow.
9. Avoid self-programming and never think bad about yourself.
10. Don’t smoke, drink or take drugs if it’s not necessary; spare your stomach from very hot or cold food or drinks; avoid too much noise and light.
11. Don’t be shy to lie – the more you lie the more people respect you.
12. Let people talk out and “empty their brains” – then load your information.
13. People never change – everybody wants to get pleasure and avoid pain.
14. “He knew too much” means “He talked too much. ”
15. Never ask extra questions – wait. Wait and the object will get used to you and open himself – nobody can stay tense for long.
16. Lonely people live longer in espionage business.
17. “No exit” situation is the one you don’t like or don’t understand.
18. Avoid:
– personal enemies (they fix negative information on you)
– silent types (they notice and think too much)
– other professionals (they’ll blow your identity)
– extra stress (it damages your heart and blood vessels and that kills your brain and your ability to think )
– talking too much
19. The best weapon against your enemy is his enemy.
20. “I want nothing” means “I want everything”.
21. Small lie gives birth to big distrust.
How to run assets
You can get tons of information through technical devices but no device can influence decisions made by leaders of other countries. That’s why for thousands of years to come, a reliable agent will be the top tool of any special service, and their actual names have to be kept secret forever, please. A VIP agent (a top government employee) is a very rare thing and depends hugely on luck, because he can make or influence big political decisions. If he has access to the Oval Office, he can change the President’s plans and strategy, and can sabotage political, economic or military actions. When major presidential initiatives fail, time after time, one might wonder who is sabotaging whom.
The most important thing a secret source can get is a reliable information on any possible attempt on the US President’s life, or concerning a decision of a foreign government to start a war against the United States. A professional agent is actually is both an instrument (to get information) and a weapon (to influence or neutralize people).
Categories:
A. "Garbage" (60%), the "no trust " category.
Recruitment is #1 priority for the officer and a part of his working plan and very often he has to recruit people who are not born agents. You can work with a nice guy, teach him, pay him, press him — and he still avoids any cooperation (busy, sick, on vacation, etc. ). It’s hard to get rid of him because, first, you have to explain to your superiors why you recruited garbage and second, there’s a rule: if you want to be very smart and innovative, a reformer, who came here to start intelligence revolution and get rid of a passive agent, recruit an active one first. Also, agents who work under pressure (blackmail) sooner or later slide into this category.
B. Good agents (30%), middle category. They adhere to the rules of discipline and keep the schedule (that’s very important even if there’s no information), deliver a lot of information that you have to verify through other sources, but don’t show much initiative. Used for regular espionage: go and talk to the object, copy documents, make a recording, take pictures, listen, watch. You can trust them and check often, anyway.
C. Born agents (10%). You are very lucky if you can recruit such people. They betray their country with pleasure and sometimes do not even ask for money because it’s in their character — they are looking for adventure or are not happy with their personal or professional life and seek improvement or revenge. They take risks, have good analytical abilities, good education, make (VIP) connections easily, "crack" any object, play the "good guy" whom you can trust. Sometimes they come to you as volunteers, and if they bring valuable stuff – recruit them
Special category. Women.
Women are a special category here, as elsewhere, and the rule is: if you can’t recruit a real agent, you recruit a woman. It’s not professional to recruit a woman for a serious operation, but if you want to get to an important object, a woman can introduce you. OK, you can recruit a US Senator’s secretary or a typist from the Pentagon, but it will be on your conscience if she gets caught. Such cases entail a life sentence, usually — how would you feel? Besides, women often fall in love with their objects and tell them everything. Finally, a married woman is much bigger problem than a married man.
Recruitment
Recruit a small number of well-informed people. Do not recruit:
– psychos
– volunteers (unless it’s a "mole" or other government employee who brings you top secret information right away. In a counter-intelligence set-up, a "volunteer" will try to get information about you, telling the minimum about himself. )
– persons with low educational and intellectual level
– people under 30 or over 70, unless it’s a VIP. (Did someone get Jim Baker? Dick Cheney? )
– mafia members
– people who are happy with their lives and careers
The best formula when you recruit is a mix of money and ideology (brainwashing). It’s not necessary to sign recruitment obligations — people take that as a blackmail tool. It’s enough if the fellow brings a good piece of information and get paid (make a video, anyway).
Recruitment Pyramid
Priority recruitment candidates in the USA:
President
The White House staff
The Cabinet and federal agencies
The US Congress
Big corporations
Big scientific institutions
Local politicians
VIP world (celebrities – big media, show biz, big sport)
Candidates for recruitment
1. All spies who work in the USA under legal "cover" as diplomats, reporters, scientists, businessmen, actors, artists, musicians, sportsmen have the legal right to make and develop any contacts and invite people to private parties; then they "transfer" these contacts to professional recruiters. Any embassy can invite any politician to official and private parties and "work" with him there. Besides, all those people can invite prospective candidates to their countries or to other country to develop the contact; it’s much easier to recruit abroad. And remember, any contact, any talk, any piece of biography is already information.
2. You can get information about candidates through other agents and through the media.
3. It’s useful to install listening devices in the government buildings or listen to the phones, and collect compromising information on politicians. I recommend listening to the phones all over the city, if it’s the capital of the country.
"Golden" rules.
1. Do not tell the agent about problems and mistakes of the agency, about your personal problems, about other agents, about his own file and compromising information you have on him.
2. Don’t show him any classified documents – you might provoke him to sell the information to somebody else.
3. Don’t trust your agents too much; they can use you to compromise their personal enemies.
4. Never criticize the source – be an adviser. Don’t talk straight if he avoids cooperation or brings you garbage – just reduce or stop payments, or get rid of him.
5. You lose the agent if you don’t pay him for a job well done, ask him to "produce" fake information (to show your bosses how much great espionage activity you have going on) or if you don’t care about his personal security and his personal problems (health, career). And — never give poison to your agent for security reasons.
Questioning the source
This is of extreme importance – the right question brings you the right answer and top secret info. Give your agent a chance to tell and show you everything he’s brought, no matter how chaotic the story might be or how ordinary the documents look. Don’t make written notices. Don’t bring written questions even if you are talking about some advanced technology — look and be professional. Don’t let the agent analyze the information before he talks to you and don’t let him bring it in a written form – it’s usually not complete; he can lose it; or it may be stolen from him. If there are documents, he has to bring a microfilm. Ask questions — when? where? what happened? why? what’s going to happen next?
After that you tell the story back to him and he adds details. At the end of the meeting give the agent another task and don’t ask him to bring you "something, " because he’ll bring you just that "something" and nothing else.
Remember, questioning is not interrogation; do not bring another officer to the meeting because it will look like cross interrogation.
Teaching the source
Teach your agent to:
– follow security rules while talking to people, working with the documents and especially meeting the officer (some foreign agencies practice open contacts with many people, hoping that the meeting with the agent won’t attract much attention — I don’t recommend that)
– always stay calm in stressful situations
– always keep discipline and come in time
– use analytic abilities working with people and documents – ask yourself as many questions as you can
Checking the source
You can never be sure you are not working with a "double agent, " even if he brings you top secret stuff. Besides, agents are human beings and they make mistakes — they forget about security, spend too much money, talk too much and ask extra questions; if arrested they may not play the hero but will tell everything. Anyway, you can check your source:
a. by fake arrest followed by severe interrogation.
b. through provocation (tell him you know about his "double game" and watch his behavior after the meeting (it’s good to have a listening device or a camera in his house).
c. by making an analysis of all the information and documents he delivers and comparing it with information from other sources.
d. through other agents.
e. through your "mole" in counter-intelligence (if you’re lucky).
f. through technical devices (reading the mail, listening to the phone, secret searching his house and office, watching him through hidden cameras, trying surveillance in the street).
Agent termination (one-way ticket)
It doesn’t happen often but you have to know some special situations when you have to terminate the agent:
1. He knows too much (talks too much) and is ready to betray you.
2. VIP agent (politician) is under suspicion and you can’t help him for political reasons (diplomatic, international scandal, etc. ) — in such a case an accident could be staged. It happens that the agent is too close to President.
3. Agent was involved in special operations (murders) and is dangerous as a witness.
4. Agent is trying to blackmail you.
5. You need to press (blackmail) other agents.
Special Influence Methods
1. Tortures
Torture is a category of methods of interrogation designed to shock, hurt and humiliate the object and get information or to make him do something (if used for blackmail). Points to remember:
–ongoing torture decreases pain sensitivity
–people with strong will power take torture as a test
–resistance to torture is often a form of hysterics after arrest
–the object could take himself as a martyr if you torture him too much
–torture could damage object’s psyche and you won’t be able to work with him (that’s why we keep terrorists in Guantanamo Bay without trial – we turn them into idiots)
–people usually trust "after torture information" more than voluntary confessions
–there are different types of torture and professionals often combine them
Techniques of psychological torture include:
– fake execution
– complete isolation ("wall therapy")
– daylight deprivation
– forcible narcotics addiction. Here you can use depressants, stimulants, opiates or hallucinogens : depressants (alcohol, barbiturates, antianxiety drugs
with effects of euphoria, tension reduction,, muscle relaxation, drowsiness; stimulants (cocaine, amphetamine, methamphetamine (crystal meth), with effects of fast
euphoria, exhilaration, high physical and mental energy, reduced appetite, perceptions of power, and sociability; hallucinogens with effects of euphoria, hallucinations, distorted perceptions and sensations
–making the object observe others being tortured (such as family members)
–abuse of object’s national, religious feelings or political views)
The effects of psychological torture are: anxiety, depression, fear, psychosis, difficulty concentrating, communication disabilities, insomnia, impaired memory, headaches, hallucinations, sexual disturbances, destruction of self-image, inability to socialize
Techniques of physical torture include:
–food, water, sleep deprivation
–damage to vital body organs (brain, lungs, kidneys, liver, private parts) plus electric shock. The brain is particularly dependent on a continuous and stable supply of oxygen and glucose.
–rape
–face deformation
–water cure ( the torturer pours water down the throat of the subject to inflict the terror of drowning. In another variation, the subject is tied or held don in a chair, his face is covered with a cloth or plastic sheet, and water is poured slowly or quickly over his face to encourage him to talk
The effects of physical torture are: extreme (unbearable) pain, hypertension, fatigue, cardiopulmonary and other disorders, brain atrophy.
2. Special psychology
1. "Brain washing" (implantation of new ideas). The process is: isolation from outside world ("information vacuum") — sleep and food limitation (very effective) — "bombing" with slogans – ideological aggression – achieving the result (brain is loaded). The object is now ready to brainwash newcomers.
2. "Behavior modification" (by placing into a group). The process is: initial contact — introduction to a group — mutual interests — mutual activity–mutual ideas — control and prevention of any negative contacts outside the group. No rush, no pressure.
3. Special psychotherapy methods: talk + drugs + blondes + alcohol (used for recruitment)
Attention: An alcoholic is more impulsive, untrustful and unreliable; he demonstrates a poverty of ideas and incapacity for attention. He usually has serious personality maladjustments. He’s immature, insecure, oversensitive and anxious. Without alcohol he’s unable to meet and enjoy people socially, and suffers from marked feeling of inferiority. Besides, alcoholics suffer from vitamin B1 deficiency, which leads to anatomic changes in the central nervous system and heart with symptoms like anorexia, fatigability, and sleep disturbances. Other common symptoms are irritability, poor memory, inability to concentrate, heart pain.
4. "Transfer" (the object is placed in a regular hospital and then he’s transferred to a mental health clinic or jail). In jail you can use such methods an accelerated work schedule (to exhaust the object), turning him into a number to traumatize his psyche, physical punishment or a threat of punishment to keep the object tense and depressed; senseless labor to destroy his personality. Remember: the lower the intellectual level of the object, the more aggressive he is and more sensitive to incentive or punishment.
You can actually re-organize any object’s behavior by combining rewards and punishments, exposing him to feared situations and teaching him an instinct of a total (political) obedience.
Imprisonment is a very strong (sometimes — ultimate) tool. My friend who spent 10 years in jail described the changes in his behavior like this:
1st year – aggression as self-defense method (to survive)
2nd year – less personal tension, attempts to adapt the mind and body to the new, isolated way of life
3rd, 4th, 5th – gaining some inside status
6th, 7th – life in jail looks like natural routine
10th – euphoria
3. Blackmail
Used to force a person to do something (or stop the action) against his will; it’s used also for recruitment. Blackmail methods include:
1. Leaking "dirt" on the object through media
2. Creating problems in his personal life and career
3. Straight blackmail (threatening to make public certain compromising facts about him)
4. Placing weapons, drugs, secret documents in object’s house or office, followed by search and arrest
5. Accusations of rape (robbery) (use hookers for that)
6. Blackmail by pressing family members. Careful, object may commit suicide after intense blackmail, especially if he is an intellectual
Murders technologies
Regular
Shooting, explosives or poison (cyanides, curare). Use a sniper or a "mouse" car (loaded with explosives and parked on the object’s route) if access to the object is impossible because of high security. Anyway, the murder is obvious and investigation is inevitable.
General scheme.
The best thing to do is to recruit or " install" somebody with access to the object’s security system and get information on his schedule (plus health and habits), places where he likes to relax. Try to gain access to his phone.
Then prepare the plan and train three groups: surveillance (with optics and radios), action (includes snipers, explosives technicians or staged accidents specialists), and security (these people neutralize bodyguards, witnesses and other people who could interrupt the action; they complete the action if the action group fails; and they can neutralize the action group later, if planned so; they "cover" the safe retreat of action group and "cut" the chase).
For some operations you can modify the ammunition to make it more deadly – hollow cuts in the tip of the bullets will cause the lead to fragment upon impact, making a huge exit hole. You reach same effect using bullets with a drop of mercury in a hollow tip and you can also coat bullets with arsenic or cyanide. Use depleted, non-radioactive uranium bullets (uranium is much heavier than lead – it can be used to make a bullet with a smaller slug and a larger portion of explosive). Teflon bullets are good because with Teflon’s antifriction characteristics they pierce bullet proof vests.
Complex
Staged accidents (suicides, catastrophes, drowning or fall, robbery or rape followed by murder, technical accident (fire, electricity, gas), drugs, weapons, poison, explosives misuse. Also, staged natural death (stroke, heart attack, chronic illness as a result of using special technical devices like irradiation).
" Illegal " spies.
When I talk about “the best, ” I mean the highest intelligence level — illegal spies, intelligence operatives who are secretly deployed abroad and covertly operate there under assumed names and well-documented cover stories, masquerading as native citizens. It's very important if you get, for example, original birth certificate of American citizen, who died (at young age preferably) or any records and documents on him(birth, wedding, death, any IDs, etc).
The process of training and “penetration” of the officer is rather complex and includes:
a) Special training. Foreign language, general, political and special (espionage and counter-espionage) knowledge of the target country; personal cover story — new biography, special technical devices, recruitment methods). Up to three years.
b) Illegal probation period abroad. A trip abroad through intermediate countries with numerous changes of passports and cover stories, jobs, personal connections. Then he gets to the target country, stays there for another 1-2 years and goes back to his country for additional training and correction of cover story — actually, it’s his first combat assignment. The most important part of this assignment is to check the reliability of the cover story and documents; the cover story has to be reinforced with new and old true facts, like short-term studies at universities or professional training courses).
c) Intermediate legislation. On his way back the officer could stay in an intermediate country for another 1-2 years, make contacts with business, scientists, government employees, celebrities.
d) Basic legislation. Officer comes to the target country, obtains genuine documents, gets a job which allows him to travel and talk to many people, recruit informants thus creating an illegal station.
The illegal is usually supplied with a variety of cover documents to make him “invisible” for counter-intelligence — some are used only to cross the borders on the way to a target country, others — to live there, other documents — only for travel to “third countries” to meet with officers of legal or illegal stations or to be used in case of urgent recall to home country (in that case the illegal is supposed to transit at least two or three countries). His further activity depends on how professional counter-espionage service is working in the country.
He could fail in his mission also because of:
– poor training and low quality documents
– neglecting security rules.
– one mistake in pronunciation can give you away
– treason (traitor-informant or a “mole” inside his own service)
– low personal security level (while working with sources)
If we talk about "legal plants", KGB (and modern Russian SVR) loves to recruit Harvard, Yale and Columbia students and "push" them to the top of American politics – US Congress, the White House, the Cabinet.
Coup d'etat
Coups, like war, are one of the most violent tools of special services and one could be artificially staged in a target country by “feeding” and “pushing” the political opposition or by using VIP agents in the government. Most coups are “Bureaucratic, ” and entail mainly a change of leader, usually by person #2. That person might be the trigger or might be induced to practice “passive sabotage” and allow certain others to take over. It is also an example of political engineering. Coups usually use the power of the existing government for its own takeover.
Conditions for a successful coup:
–the army is supportive or at least neutral (a coup usually involves control of some active
–portion of the military while neutralizing the remainder of the armed services)
–the leader is out of town (vacation, visit abroad) or is ill
–a political or economic crisis.
–opponents fail to dislodge the plotters, allowing them to consolidate their position, obtain the surrender or acquiescence of the populace, and claim legitimacy
Military coup
Changing a civilian government to a military one, usually in developing countries.
Conditions: a long-term political and economic crisis that threatens national security and the unity of the country. Military chief(s) eventually let the people elect a civilian president and form a civilian government after “re-construction” of political and economic systems. They usually leave for themselves the right to control further political process.
A good example is the attempt of anti-Nazi officers to assassinate Hitler in a coup. On July 20, 1944, Colonel Claus Schenk von Stauffenberg brought a bomb-laden suitcase into a briefing room where Hitler was holding a meeting. The bomb exploded and several persons were killed. Hitler was wounded, but his life was saved when the suitcase was unwittingly moved away by someone. Hitler was shielded from the blast by the conference table, leaving him with minor injuries. Subsequently about 5, 000 people were arrested by the Gestapo and about 200, includingStauffenberg, were executed in connection with attempt, some on the very same day (which means that Himmler was involved and knew perfectly well about the coup).
“Democratic” coup
A democratic coup would be a change of the government by the most aggressive (nationalistic) political party.
Conditions:
–artificial or actual government crisis
–mass anti-government propaganda
–organized “democratic” movement all over the country
–provoked mass protests (10, 000 participants and up) and civil disobedience actions
To provoke a mass anti-government meeting you have to bring to the place well-trained group of agitators (bring as many as you can), and they will inevitably attract an equal number of curious persons who seek adventures and emotions, as well as those unhappy with the government (unemployed people, young and old, are usually very supportive). Arrange transportation of the participants to take them to meeting places in private or public vehicles.
Design placards, flags and banners with different radical slogans or key words; prepare flyers, pamphlets (with instructions for the participants), posters and signs (to make the concentration more noticeable). It’s good if you place a surveillance team on the top floors of the nearby buildings – they will report any changes in the event; have also messengers to transmit your orders. Remember, if you clash with police and military and a participant(s) is being killed, the conflict inflames right away.
Your people can also infiltrate the spontaneous anti-government meeting and turn it into a mass radical demonstration with fights and incidents. Key agitators (with security attached to them) have to be dispersed and stand by placards, signs, lampposts; they have to avoid places of disturbances, once they have provoked them.
–the leader of the meeting must be protected by a ring of bodyguards (they protect him from police or help him to escape).
–government buildings must be “covered” by a blockade
“Democratic” nationalistic coups in Ukraine (2004 and 2014), so-called “orange revolution”. CIA gave the nationalists my instruction and followed them absolutely: acts of civil disobedience, strikes, sit-ins (in the central square), aggressive propaganda, mass demands to re-vote the presidential election, clashes with police.
Revolution
A change of government and political and economic systems by political gangsters, usually fed, pushed, incited, and possibly funded and equipped by the secret services of another country. (Even the American Revolution would not have succeeded without French military advisors and financial support. ) Government buildings are blockaded, the government isolated, all communications and transportation systems captured, government media closed, new government formed.
Conditions:
–political and economic crisis
–mass anti-government propaganda (in the army too)-provoked mass protests and civil disobedience actions -terror and urban guerillas
Self-coup
The current government assumes extraordinary powers not allowed by the legislation. It often happens when the president is democratically elected, but later takes control of the legislative and judicial powers.
Surveillance
Actual espionage is not what you see in the movies and you have absolutely no chance of evasion if a real professional surveillance crew is following you. Why? Because they use multiple methods and mixed methods.. Physical surveillance.
Methods
"One line" – officers follow the object forming a line behind him and passing him one by one.
"Two lines" – officers form two lines on both sides of the street.
"Circle" – officers block the area and start searching (used in case they lose the object).
"Fork" – one officer (a car) moves in front of the object, another one – behind, other officers (cars) move along parallel streets
"Box" – used when the object enters supermarket, hotel, restaurant. One or two officers follow the object, the others wait for him at the exits.
"Demonstration" – officers demonstrate their presence to press the object and lower his activity.
"Provocation" – officers attack the object, beat him, steal (secret) documents. Often used to lower his activity if he’s trying to play James Bond.
"Outstrip" – officers do not follow the object because they know exactly where he’s going.
"Football" – officers pass the object to each other (car — a group — bicyclist — car…)
"Movie" – the crew watches the object in stages: first day — to the subway only, second day — from subway to his office, etc. (used abroad). The crew has to have a female member if they are watching a woman (she could use the ladies room for a secret meeting) and members of various ethnicities (white, black, Latino) because the object could go to a specific ethnic area.
If you’re the object and you’ve noticed surveillance:
Don’t rush, move at the same speed.
Relax at the nearest bar (and relax the crew).
Don’t show how professional you are by trying to disappear, otherwise they could intensify surveillance or even neutralize you (smash your car, beat you up).
Postpone the operation you were engaged in.
Use a "draught" if you need to see your agent no matter what. Change lanes (if you are driving), stop the car and then drive left or right.
If you don’t see surveillance, that means either there’s no surveillance or you’ve failed in counter-surveillance. Discreetly watch the agent who’s coming to meet you and try to detect any possible surveillance; or you may have been "outstripped. "
Surveillance crew mistakes:
The same crew follows the object all day long.
The object "rules" the crew and calculates it (he moves faster — the crew moves faster).
A crew member is too noticeable (unusual dress, haircut, disabled parts of the body, too fat or too skinny, too ugly or too pretty).
The crew starts to search possible hiding places for espionage evidence right after the object leaves (and he may be watching).
The crew leaves traces after a secret search of the object’s house (office).
The crew does not report its mistakes or the fact that they’ve lost the object.
The crew is not professional (using childish tricks like jumping out of a subway train just before the doors close).
Technical Surveillance
1. Visual surveillance. Done through special holes in the ceilings and walls, through the windows from the opposite building (car) or by installing the camera inside the house (you can substitute something, like a clock, for the same thing but "stuffed" with a camera or recorder. ) You can use informant as well to watch the object outside his house (especially if you want to do a secret search).
2. Listening devices. The easiest thing is to listen to the object’s phone (record all calls, including those dialed "by mistake"). If you work inside his apartment, make sure you equip the room where he usually talks. Attention: avoid widespread mistake when your agent keeps the listening device on his body; install a miniature device in his clothes or shoes, because the object could try a test and ask the agent to take off his clothes or invite him to the sauna or pool.
3. If you are working abroad, listen 24/7 to local counterintelligence surveillance radiofrequencies.
4. Reading the mail. When you control the object’s mail, remember he could use multiple addresses and PO boxes. Open all the letters with no return address or PO box. Watch when you open the letter — the object could leave a tiny piece of paper, hair, etc. to check if anybody opened the letter. Analyze the text carefully — there could be a cipher or the words with double meaning (jargon), especially when you read mafia mail.
5. Combination of above-mentioned methods
Spies Identification
If a spy is an intelligence officer working abroad under "cover" (diplomat, businessman, reporter) you can identify him by:
– following the careers of all diplomats who work at your enemy’s embassies all over the world
– recruiting a "mole" inside the intelligence service (or inside the station)
– setting up your agent for recruitment by the enemy’s station
– watching foreigners who try to make discreet contacts with native citizens with access to secrets
– making a model of a spy (professional behavior, attempts to detect surveillance, attempts to recruit sources or just get any classified information during normal meetings, "throwing away" money trying to get access to government employees, military and scientific circles)
– using secret surveillance and listening devices inside the station and practicing secret searches
If a spy is an intelligence officer working in your country under "cover" of a native citizen (or he is recruited by a native citizen) you identify him by making a model (contacts with identified spies — that’s often the only sign which points out a spy, and that’s why surveillance is very important in getting information from a "mole"). CIA “mole” and KGB intelligence officer V. Martynov arrested at Moscow airport, 1987.
"Moles"
CIA “mole” and KGB intelligence officer V. Martynov arrested at Moscow airport, 1987. Later he was executed.
A "mole" is a spy inside the government, recruited or "installed" most often within the special services, by an outside government/agency. The 3 most dangerous things a "mole" can do:
1. Calculate President’s plans and decisions judging by information he’s asking for.
2. Manipulate information being sent to President, and thus influence global political decisions
3. Paralyze to some extent the government (if he’s CIA or FBI Director)
Methods to detect a "mole":
A. Use index cards (special file) — never use computers to save this information!
Prepare a file on each officer and mark there the signs of a "mole" — has or spends too much money, asks too many extra questions; uses professional skills to check for physical and technical surveillance; has discreet contacts with foreigners; discreet copying of top secret documents; attempts to get a job in most secret departments; talks with close friends and family members about the possibility of making money as a "mole"; behavior deviations — extra suspiciousness, excitement, depression, drugs or alcohol addiction. Three signs are enough to start an investigation — the "triangulation" principle.
B. Use provocation. If a prospective "mole" is looking for a contact with the enemy and is ready to betray, and you have exact information, organize such a "meeting" for him. Do not arrest the person right away — play along, as he may give you connections to other people who are ready to betray. There’s one more provocation method: you supply the suspects with "highly classified information" and just watch what they do.
C. Use "filter" or "narrowing the circle. " Include all the officers you suspect in a "circle" and narrow it until one name is left as the most likely suspect.
D. Make a "model" of a "mole, " judging by information you have on him.
E. Recruit an insider. Recruit a "mole" inside your enemy’s intelligence service and he’ll help you to find the one inside yours (it’s called "grabbing the other end of a thread").
F. Don’t trust anybody.
What to do if you’ve detected a "mole"
– assess the damage
– restrict his access to classified information and start "feeding" him with fake data
– stop all operations he was involved in and create the illusion they are still in progress
– bring home officers and agents who work abroad and had contacts with him and those to whose files he had access
– start 24/7 surveillance if you’ve decided to play the game and look into his contacts
– arrest the "mole" discreetly (if you want to continue the game)
Effective methods to prevent treason do not exist.
How to cover your "mole"
There are special methods to cover your own "mole" and a "switch" is the most effective — it’s when you "switch" counterintelligence to other, innocent persons who work with the "mole. " You can try information "leaks" through a "double agent" — it looks like you receive top secret information through another traitor or by breaking the electronic security systems. Or you can try information "leak" through publications in big newspapers — it looks like information is not secret and is known to many people or there’s another "mole. "
Special Strategies
Every operation demands a set of original methods, especially if we are talking about strategic intelligence. I give you a few examples.
1. "Domino" or "chain reaction. " A coup, revolution or civil war in one country provokes the same actions in other countries (neighbors). It doesn't matter what country is going to be next, most important – what country is a target.
2. "False flag". The planned, but never executed, 1962 Operation Northwoods plot by the U. S. administration for a war with Cuba involved scenarios such as hijacking a passenger plane and blaming it on Cuba.
3. "Sliding" strategy. Transformation of a secret operation into an open one: support of illegal opposition/coup.
4. "Restriction. " You damage (limit) international and economic connections (projects) of the enemy.
5. "Monopoly. " Special operation to keep country’s monopoly or status as economic leader or special (nuclear) holder, or high tech producer. Includes actions to restrict the attempts of other countries to get strategic raw materials and modern weapons and technologies.
6. "Reverse effect. " The government declares a certain goal and launches a military or special operation, but the result is something quite different, possibly opposite. Examples: instead of separating (ethnic) group "A" from group "B" both of them are being exterminated; instead of peace and democracy in a certain region, power is being concentrated in one group and the opposition is being exterminated.
7. "Clash. " You "clash" the government and opposition of a target country and support civil war until the country is ruined and you get it for free.
8. "Salami-slice strategy". It’s a process of threats and alliances used to overcome opposition. It includes the creation of several factions within the opposing political party, and then dismantling that party from inside, without causing the "sliced" sides to protest.
9. "Positive shock. " A domestic operation; to save the government during a crisis, special service provokes artificial civil conflict or sabotage, imitation (terror), and the government takes care of the "problem. "
10. "Controlled crisis export" (see "Foreign Policy")
11. "Sanitation border. " "Fencing" the target country by enemies (neighbors).
12. "Alibi. " You build a "chain" of evidence (witnesses) and move the investigation to a dead end.
13. "Passive sabotage. " A very effective strategy used to cover up a major action like the assassination of a President or the destruction of several office towers. You just "do not see the bad guys" who are going to kill the President or blow up the city. In any case you win — the perpetrators are not sure you are watching them; you can arrest them if the object survives or liquidate them once the object is dead. You don’t need a big conspiracy, you just give the order to ignore certain people until their plan materializes.
14. "Special tour. " You help the target country to "build democratic institutions" (the government and local administrations) by sending official crews to help. Actually, they rule the country and that’s a "hidden occupation. "
15. "Mask. " You mask your actual global plans (reforms) by another big action (war).
16. Illegal espionage operations. Very dangerous, because illegal spy is playing born American and can make career in business, becoming #1 Pentagon supplier or in the government, getting to the Congress or even White House.
Chapter 6. Counterespionage management
"Golden rules"
1. Don’t die a hero – that’s bad planning, poor training and lack of experience; the dead man goes to a hall of shame and stupidity. Bad planning is an operational failure; once things have gone off track it is far more complicated to achieve the objective. Multi-step complex operations come from the fantasies of bureaucrats who watch too many movies. Keep it simple if you want to get it right.
2. Never provoke people to break the law – that’s not professional.
3. Always look for insider if it’s about sophisticated operation (bank robbery, etc. ).
Investigation
Stages:
– secure and examine carefully the crime scene (every person who enters the scene is a potential destroyer of physical evidence)
– record the scene (make photos, sketches, notes with detailed written description of the scene with the location of evidences recovered)
– collect physical evidences (blood, semen, saliva, hair, documents, drugs, weapons and explosives, poisonous substances, fingerprints, traces, soils and minerals, fiber) and package everything
– collect confessions and eyewitnesses accounts and then
– make a plan of investigation and correct it later
– research similar crimes and criminals involved
– make a model (profile) of the suspect
– analyze expertise data
– work with secret sources
– cooperate with other divisions (abroad, if needed)
– make arrest
– interrogate
Arrest
In daytime arrest people discreetly – don’t inflame extra public irritation. There’s a general rule: more arrests – less crime prevention (after being in jail people, engage in more sophisticated and secret criminal activity). After mass arrests at certain places (buildings) repeat the action in a day or two.
Procedure:
– chasing the object, block the area into circles (follow the plan for a certain area) and try to "push" him to a certain place where your team is waiting
– taking the object in the street: look around for his partner(s), who could shoot you from behind
– be on the alert if anybody tries to talk to you in the street – it could be an attempt to divert your attention
– arresting a crew, shoot and disarm any people with guns first
– never hesitate to shoot terrorists – some of them have mental problems and won’t think a second before shooting you
– arrest a dangerous object while he’s relaxed (drugs, alcohol, sex, sleep) and don’t let him kill himself, eliminate evidences or warn his partners. (Most people feel more relaxed when traveling abroad. ) To take the object alive, scream, shoot over his head, use smoke and light grenades.
– camouflage your team (as ambulance workers, construction workers, vendors, etc. )
– if there’s a crowd around the object, shoot in the air and order everybody to lie down— the object has no choice
– if the object is well armed and very dangerous (and you have intelligence information on that), you have to shoot him even in a very crowded area as you never know what he’s going to do next — take hostages, shoot people or blow up a bomb (three wounded people is a better score than three hundred dead).
Interrogation
Interrogation is a conversational process of information gathering. The intent of interrogation is to control an individual so that he will either willingly supply the requested information or, if someone is an unwilling participant in the process, to make the person submit to the demands for information.
Remember, people tend to:
–talk when they are under stress and respond to kindness and understanding.
–show deference when confronted by superior authority, This is culturally dependent, but in most areas of the world people are used to responding to questions from a variety of government and quasi-government officials.
–operate within a framework of personal and culturally derived values. People tend to respond positively to individuals who display the same value system and negatively when their core values are challenged.
–respond to physical and, more importantly, emotional self-interest.
–fail to apply or remember lessons they may have been taught regarding security if confronted with a disorganized or strange situation
–be more willing to discuss a topic about which the interrogator demonstrates identical or related experience or knowledge
–appreciate flattery and exoneration from guilt
Tricks:
a) "good cop / bad cop"
b)"story under a story" (after intense interrogation the object tells a different story — which is not true, either)
c) "bombing" with questions
d) pressure by not interrogating
e) "silence makes your situation worse" trick
f) "admit one small episode and that’s it" trick
g) "I help you — you help me" trick
h) "shift" – try to shift the blame away from the suspect to some other person or set of circumstances that prompted the subject to commit the crime. That is, develop themes containing reasons that will justify or excuse the crime. Themes may be developed or changed to find one to which the accused is most responsive.
Methods to detect a "mole":
A. Use index cards (special file) — never use computers to save this information!
Prepare a file on each officer and mark there the signs of a "mole" — has or spends too much money, asks too many extra questions; uses professional skills to check for physical and technical surveillance; has discreet contacts with foreigners; discreet copying of top secret documents; attempts to get a job in most secret departments; talks with close friends and family members about the possibility of making money as a "mole"; behavior deviations — extra suspiciousness, excitement, depression, drugs or alcohol addiction. Three signs are enough to start an investigation — the "triangulation" principle.
B. Use provocation. If a prospective "mole" is looking for a contact with the enemy and is ready to betray, and you have exact information, organize such a "meeting" for him. Do not arrest the person right away — play along, as he may give you connections to other people who are ready to betray. There’s one more provocation method: you supply the suspects with "highly classified information" and just watch what they do.
C. Use "filter" or "narrowing the circle. " Include all the officers you suspect in a "circle" and narrow it until one name is left as the most likely suspect.
D. Make a "model" of a "mole, " judging by information you have on him.
E. Recruit an insider. Recruit a "mole" inside your enemy’s intelligence service and he’ll help you to find the one inside yours (it’s called "grabbing the other end of a thread").
F. Don’t trust anybody.
What to do if you’ve detected a "mole"
– assess the damage
– restrict his access to classified information and start "feeding" him with fake data
– stop all operations he was involved in and create the illusion they are still in progress
– bring home officers and agents who work abroad and had contacts with him and those to whose files he had access
– start 24/7 surveillance if you’ve decided to play the game and look into his contacts
– arrest the "mole" discreetly (if you want to continue the game)
Effective methods to prevent treason do not exist.
How to cover your "mole"
There are special methods to cover your own "mole" and a "switch" is the most effective — it’s when you "switch" counterintelligence to other, innocent persons who work with the "mole. " You can try information "leaks" through a "double agent" — it looks like you receive top secret information through another traitor or by breaking the electronic security systems. Or you can try information "leak" through publications in big newspapers — it looks like information is not secret and is known to many people or there’s another "mole. "
President's protection (instruction for Secret Service)
The top priority in protecting the President’s life must be organized and complete intelligence. Any information from any person from any country concerning the President’s personal security has to be immediately analyzed, and immediate action has to be performed. This is the first priority for intelligence and counter-intelligence agencies and police as well as the Secret Service. If the system is organized properly, nobody could even get in a position to try to shoot. Of course, the safest thing is to restrict the President’s routes to government buildings only; but he has to travel and he has to travel abroad, too. Still, the President should leave his Office only when he really has to.
Since the President has to be let out from time to time, the newer technique is to restrict where the onlookers may congregate, especially those who wish to take the opportunity to express dismay with Presidential policies. Thus we now see the evolution of "free speech corners" so that demonstrators are confined to specific areas far from the actual event where the President is appearing or the route he is transiting.
Practical protection during presidential appearances
1. The Secret Service must have a top-secret plan of all visits, because the advance group has to come to the place at least a week ahead and cooperate with the field FBI offices and police (foreign special services if it’s a visit abroad) paying attention to extremist groups and organizations. Officers and technicians search the place, looking for possible explosives, radioactive, biological and chemical dangerous or poisonous stuff and weapons; they check the walls, floors and ceilings; check air and water in the area; install weapons and explosives detectors and stay at the place 24/7, using night vision devices, too. (Dogs are good helpers if there is any question of explosives. ) You have to check nearby houses as well (there could be people with mental health problems or dangerous criminals. Remember, the President must not appear in open areas close to apartment buildings. And the President has to be able to reach the National Security Command Center at any time.
2. If the President has to make a speech in open area there should be at least 3 security circles around him:
– up to 50 ft (personal bodyguards, weapons and explosives technicians)
– up to 200 ft (fast reaction anti-terror group)
– up to 1000 ft (support groups, snipers, police)
The security system includes both "open" and undercover groups (obvious security and people who play the crowd or service — drivers, waiters, cleaners — terrorists don’t pay attention to them, as a rule). Each group follows its instructions strictly and avoids mess (personal bodyguards are in charge of immediate protection, anti-terror group has to fight and chase terrorists, etc. ). Extra people always mean extra danger, so the most secure situation is when extra people have no access to the President at all and can’t get into any of three circles. The guest list has to be triple checked to exclude anybody with criminal records who could compromise the leader. Reporters are there too and you have to tell them exactly where to wait (they have to be checked and kept separate after that), where to stand and what pictures (poses) to take; the President can’t look stupid or funny. Inside the building watch when people applaud, stand up and sit down — terrorists prefer these situations to shoot or blow explosives.
When President moves through or along the crowd, "cut" it into pieces, guard him in circles, watch people who are carrying any objects (no flowers! ) — they must not approach him; watch people with hands in their pockets, those who try to touch him, shake his hand, pass any object (gift, picture, photo). They must not be allowed to do that. If anybody behaves in a suspicious way, hold him tight (so he can’t take out a gun) and "screw" him out of the crowd. In case of any attempt push the President to the ground, cover him and shoot immediately. Then leave the place as soon as possible and bring him to the hospital for a check up (even if he’s OK).
The worst one – Secret Service and other agencies get inadequate intelligence information on a possible attempt or overlook important information, including anonymous letters and mail from psychos. (They must have information, even if it’s "inside" the White House conspiracy. Agents have to memorize pictures of all the most dangerous persons who are wanted in the United States and people who were involved in attempted attacks on top politicians worldwide. )
The next two — extraneous people are allowed access to the President or extraneous people stay in the area close enough to shoot the President. In 1997, a France Press reporter took a picture of the Clintons dancing during their vacation on the Virgin Islands — they were dressed for the Caribbean and were happy in their privacy. Luckily, it was just a reporter, but what if it had been a sniper? What was the Secret Service doing? Then the picture was published worldwide and Hillary Clinton was furious – she didn’t look attractive at all.
The last two major errors occur when (1) you can’t identify the potential terrorists in the crowd and (2) you react too slow or waste time evacuating the President.
Chapter 7. Military management
Commander-in-Chief.
American President loves war, not peace, because:
a) Successful military engagement enhances presidential popularity. All five Presidents who have run for re-election during a war have won.
b) A quick war improves the electoral fortunes of the president’s political party.
c) War is good business, at least if you win, and at least if it does not drag on too long. It stimulates demand for a variety of manufactured goods and services (even if they are all destined to go down the drain) and is a powerful stimulus to all fields of scientific endeavor.
d) War provides opportunities to direct lucrative contracts to companies and individuals who helped get the President elected, or who can help in the future; and to the constituents of select Senators and Congressmen for the same reasons.
e) War usually pleases the Joint Chiefs (and their full support is important politically).
f) War keeps down the unemployment figures.
g) War is just one detail in a vast ongoing game of international strategy for domination; it is as much a financial operation as anything else.
h) War unifies the country, and keeps the public’s attention away from issues that might be controversial.
i) War provides a rationale for the implementation of tighter legislation and the removal of certain freedoms that would never be tolerated in peacetime America.
At the same time, war is limited by political decisions and by public opinion. Initially the use of US forces spurs a "rally around the flag" effect that lifts the President’s popularity and builds up support for the troops. But the American people are casualty averse and the positive effect lasts only until the number of casualties and the length of the engagement begin to wear on the public. Continued military action will then have a deleterious effect on presidential approval ratings as the war becomes increasingly unpopular.
In the long run, the destruction of such vast quantities of resources, and the diversion of so much of the nation’s productive capacity away from actual goods and services for the real economy, are obviously immensely deleterious. Eventually, these downside effects will begin to dawn on even the best-manipulated electorate.
Sniper
"Golden" rules
1. Train your muscles to snap to the standard position for shooting, to squeeze the trigger straight back with the ball of your finger to avoid jerking the gun sideways.
Train yourself to shoot while you stand, sit, lie, walk, run, jump, fall down; shoot at voices, shoot in a dark room, different weather and distance, day and night; shoot one object and a group; use one gun, two guns, gun and submachine gun (some doctrines train a sniper to breathe deeply before shooting, then hold their lungs empty while he lines up and takes his shot; other go further, teaching a sniper to shoot between heartbeats to minimize barrel motion)
2. Camouflage yourself ten times before you make a single shot. Position yourself in a building (no rooftops or churches! ), which offers a long-range fields of fire and all-round observation. Don’t stay in places with heavy traffic! Use unusual angles of approach and frequent slow movement to prevent accurate counter-attacks.
3. Move slowly to prevent accurate counter-attack, don’t be a mark yourself
4. Kill officers and military leaders first (Attention, officers: don’t walk in front of your soldiers! )
5. Use suppressive fire to cover a retreat
6. Use rapid fire when the squad attempts a rescue
7. Shoot helicopters, turbine disks of parked jet fighters, missile guidance packages, tubes or wave guides of radar sets
8. At distances over 300 m attempt body shots, aiming at the chest; at lesser distances attempt head shots (the most effective range is 300 to 600 meters). Police snipers who generally engage at much shorter distances may attempt head shots to ensure the kill (in instant-death hostage situations they shoot for the cerebellum, a part of the brain that controls voluntary movement that lies at the base of the skull).
9. Shoot from flanks and rear
10. Never approach the body until you shoot it several times
11. Careful: the object could be wearing a bulletproof vest
12. It’s important to get to the place, but it’s more important to get out alive
13. Remember, in hot weather bullets travel higher, in cold — lower; a silencer reduces the maximum effective range of the weapon. Wind poses the biggest problem — the stronger the wind, the more difficult it is to hold the rifle steady and gauge how it will affect the bullet’s trajectory. (You must be able to classify the wind and the best method is to use the clock system. With you at the center of the clock and the target at 12 o’clock, the wind is assigned into three values: full, half and no value. Full value means that the force of the wind will have a full effect on the flight of the bullet, and these winds come from 3 and 9 o’clock. Half value means that a wind at the same speed, but from 1, 2, 4, 5, 7, 8, 10 and 11 o’clock, will move the bullet only half as much as a full-value wind. No value means that a wind from 6 or 12 o’clock will have little or no effect on the flight of the bullet). Shooting uphill or downhill can require more adjustment due to the effects of gravity. For moving targets, the point of aim is in front of the target ( it’s called "Leading" the target, where the amount of lead depends on the speed and angle of the target’s movement. For this technique, holding over is the preferred method. Anticipating the behavior of the target is necessary to accurately place the shot).
14. NEVER fire from the edge of a wood line – you should fire from a position inside the wood line (in the shade of shadows).
15. DO NOT cause overhead movement of trees, bushes or tall grasses by rubbing against them; move very slowly.
16. Do not use trails, roads or footpaths, avoid built-up and populated areas and areas of heavy enemy guerrilla activity.
17.. If you work in terrain without any natural support, use your rucksack, sandbag, a forked stick, or you may build a field-expedient bipod or tripod. The most accurate position though is prone, with a sandbag supporting the stock, and the stock’s cheek-piece against the cheek.
18. The sniper has a tendency to watch the target instead of his aiming point.
Counter-sniper tactics
1. Active: direct observation by posts equipped with laser protective glasses and night vision devices; patrolling with military working dogs; calculating the trajectory; bullet triangulation; using decoys to lure a sniper; using another sniper; UAV (unmanned aerial vehicles); directing artillery or mortar fire onto suspected sniper positions, the use of smoke-screens; emplacing tripwire-operated munitions, mines, or other booby-traps near suspected sniper positions( you can improvise booby-traps by connecting trip-wires to fragmentation hand grenades, smoke grenades or flares. Even though these may not kill the sniper, they will reveal his location. Booby –traps devices should be placed close to likely sniper hides or along the probable routes used into and out of the sniper’s work area). If the squad is pinned down by sniper fire and still taking casualties, the order may be given to rush the sniper’s position. If the sniper is too far for a direct rush, a "rush to cover" can also be used. The squad may take casualties, but with many moving targets and a slow-firing rifle, the losses are usually small compared to holding position and being slowly picked off. If the sniper’s position is known, but direct retaliation is not possible, a pair of squads can move through concealment (cover) and drive the nipper toward the group containing the targets. This decreases the chances that the sniper will find a stealthy, quick escape route.
2. Passive: limited exposure of the personnel (use concealed routes, avoid plazas and intersections, stay away from doorways and windows, move along the side of the street and not down the center, move in the shadows, move dispersed, avoid lighted areas at night, move quickly across open areas, avoid wearing obvious badges of rank, adapt screens on windows, use armored vehicles); use Kevlar helmet and bulletproof vest.
Military tricks
1. Use rapid dominance: technology + speed + information domination.
2. Use artillery preparation. It is the artillery fire delivered before an attack to destroy, neutralize, or suppress the enemy’s defense and to disrupt communications and disorganize the enemy’s defense.
3. Use deception especially before the first strike (air strike + artillery). Deception plays a key part in offensive operations and has two objectives: the first objective is to weaken the local defense by drawing reserves to another part of the battlefield. This may be done by making a small force seem larger than it is. The second objective is to conceal the avenue of approach and timing of the main attack.
4. Imitate assault to make the enemy expose his positions and fire system.
5. Mines, mines, mines. There are four types of minefield : the tactical large-area minefield, usually laid by engineers, for tactical use on the battlefield(i. e. to canalize the enemy into killing areas); the protective minefield, the sort that you will plant in front of your position for defensive purposes; the nuisance minefield, designed to hamper and disrupt enemy movement ; and the dummy minefield – a wired off area suitably marked can be as effective as the real thing.
6. Don’t touch anything in the places the enemy just left – check for mines first. A minefield is a mortal surprise and you have to know how to breach and cross it: remove your helmet, rucksack, watch, belt, and anything else that may hinder movement or fall off, leave your rifle and equipment with another soldier in the team, get a wooden stick about 30 cm (12 in) long for a probe and sharpen one of the ends (do not use a metal probe), place the unsharpened end of the probe in the palm of one hand with your fingers extended and your thumb holding the probe, and probe every 5 cm (2 in) across a 1-meter area in front of you and push the probe gently into the ground at an angle less than 45 degrees, kneel (or lie down) and feel upward and forward with your free hand to find tripwires and pressure prongs before starting to probe, put enough pressure on the probe to sink it slowly into the ground and if the probe does not go into the ground, pick or chip the dirt away with the probe and remove it by hand, stop probing when a solid object is touched, remove enough dirt from around the object to find out what it is. If you found a mine, remove enough dirt around it to see what type of mine it is, mark it and report its exact location to your leader. Once a footpath has been probed and the mines marked, a security team should cross the minefield to secure the far side. After the far side is secure, the rest of the unit should cross.
7. Visual indicators. Pay attention to the following indicators : trip wires, signs of road repair (new fill or paving, road patches, ditching), dead animals, damaged vehicles, tracks that stop unexplainably, wires leading away from the side of the road (they may be firing wires that are partially buried), mounds of dirt, change of plants color,, pieces of wood or othr debris on a road. Remember, mined areas, like other obstacles are often covered by fire. Keep also in mind, that local civilians try to avoid certain (mined) areas.
8. Use phony minefields to simulate live minefields. For example, disturb the ground so that it appears that mines have been emplaced and mark boundaries with appropriate warnings.
9. Make a real minefield appear phony, or camouflage it. For example, once a real minefield is settled, a wheel or a specially made circular wooden tank track marker can be run through the field, leaving track or tire marks to lure the enemy onto live mines. Antipersonnel mines should not be sown in such a field until the track marks have been laid. Another method is to leave gaps in the mechanically laid field, run vehicles through the gaps, and then close them with hand-laid mines without disturbing the track marks.
10. Use feint attack to draw defensive action towards the point under assault (it’s usually used as a diversion and to force the enemy to concentrate more manpower in a given area so that the opposing force in another area is weaker).
11. Issue false orders over the radio, imitate a tanks’, fighters’ and bombers’ assault while preparing to retreat.
12. Use dummy units and installations, phony radio traffic, movement and suppressive fires in other areas timed to coincide with the real attack
13. Use force multiplication by using decoy vehicles and use small convoys to generate dust clouds. Move trucks into and out of the area giving it the appearance of being a storage facility or logistic base.
14. Simulate damage to induce the enemy to leave important targets alone. For example, ragged patterns can be painted on the walls and roof of a building with tar and coal dust, and covers placed over them.
15. Stack debris nearby and wire any unused portions for demolition. During an attack, covers are removed under cover of smoke generators, debris scattered and demolitions blown. Subsequent enemy air photography will disclose a building that is too badly damaged to be used.
16. Change positions at night time only.
17. Use dispersal to relocate and spread out forces to increase their chances of survival.
18. Imitate fake ballistic missiles divisions and military headquarters to entrap enemy’s intelligence and sabotage groups.
19. Use "sack" strategy ("cutting" enemy’s army into separate groups).
20. Use strategic bombing (the massive attack on cities, industries, lines of communication and supply).
21. Simulate bombing of minor objects and attack important ones.
22. Use counter-battery fire (detecting with counter-battery radars the source of incoming artillery shells and firing back), using mobile artillery pieces or vehicles with mounted rocket launchers to fire and then move before any counter-battery fire can land on the original position.
23. Use airborne operations, when helicopters transport troops into the battle and provide fire support at battle sites simultaneously with artillery fire, keeping enemy off guard.
24. Helicopters are extremely important as they can be sent everywhere: to kill tanks and other helicopters, for aerial mine laying, for electronic warfare, for naval operations (anti-submarine and anti-ship patrols), to correct artillery and tactical fighters fire, for reconnaissance, command, control and communications, to insert special forces, to evacuate casualties (this helps maintain the morale of the troops), to carry supplies (missile systems, ammunition, fuel food, to escort convoys, for navigational help, to destroy battlefield radars, communications and radio relay systems, to seal gaps and protect flanks, for rear-area security, counter — penetration, rapid reinforcement of troops under pressure, raids and assaults behind enemy lines, air assault in offensive and defensive operations, to strengthen anti-tank defenses by inserting infantry anti-tank teams. Helicopters offer a strong tactical surprise and take a ground conflict into the third dimension, making the enemy’s ground maneuvers impossible.
25. When fighting an insurgency: once you get intelligence, you have to bomb the area to "soften" insurgents and then send helicopters with special forces teams right away. Helicopters suppress and cut-off by fire insurgents trying to escape and the teams clear-up the remains. Transport helicopters must bring in troops rapidly from different bases and build-up numerically superior force which insurgents cannot match.
26. Use joint bombers/fighters flights to bomb transportation, supply, bridges, railroads, highways, antiaircraft and radar sites. To gain surprise, attack with the sun behind you. Remember, enemy will try to saturate the airspace through which the aircraft will fly with fire.
27. Watch out for the tank ambushes!
Storming the City
Procedure
1. Effective intelligence is 90% of success. Use sources like agents among the enemy’s high ranking officers, prisoners of war, captured documents and maps, enemy’s activity, local civilians (agents). Use intelligence and sabotage groups (through them you can deliver your fake plans and maps). You must know how the enemy usually defends a built-up area and the approaches to it, critical objectives within the built-up area that provide decisive tactical advantages, tactical characteristics of the built-up area and its structure. Information about the population will assist in determining where to attack, what firepower restrictions may be imposed, and what areas within the urban complex must be avoided to minimize destruction of life-support facilities and civilian casualties.
2. Make the enemy attack you if possible, because if you attack first the victims calculation is 5:1.
3. Train your troops to storm this certain city.
4. Blockade the city completely.
5. Attack the city from different points ( flanks and rear! ) at the same time after intense artillery fire and bombing (that’s a very strong psychological blow. Its intensity is determined by the strength of defensive forces, the type of building construction, and the density of fires required to suppress observation and fires. You must destroy command posts, heavy weapons positions, communications, troop emplacements, tall structures that permit observation. Then engineers move forward under the cover of smoke and high explosives to neutralize barriers and breach minefields on routes into the city). Field artillery, attack helicopters and offense air support must disrupt the enemy command and control network and destroy his support units ( field artillery mostly creates breaches in buildings, walls and barricades. Mortars cover avenues of enemy troop movements, such as street intersections and alleys; mortars firing positions are placed behind walls or inside buildings close to their targets). A hasty attack is conducted when the enemy has not established strong defensive positions and attacking forces can exploit maneuver to overwhelm the defense – locate a weak spot or gap in enemy defenses, fix forward enemy elements, rapidly move through or around the gap or weak spot to be exploited. A deliberate attack is necessary when enemy defenses are extremely prepared, when the urban obstacle is extremely large or severely congested., or when the advantage of surprise has been lost. It’s divided into three basic phases: isolation from reinforcement and resupply by securing dominating terrain and utilizing direct and indirect fires; assault to rupture the defenses and secure a foothold on the perimeter of the built-up area from which attacks to clear the area may be launched (an envelopment, assaulting defensive weaknesses on the flanks or rear of the built-up area, is preferred, however, a penetration may be required; and clearance, a systematic building-by-building, block-by-block advance through the entire area..
6. Target vital bridges, transportation facilities that are required to sustain future combat operations, strategic industrial or vital communications facilities. Attacks against built-up areas will be avoided when the area is not required to support future operations, bypassing is tactically feasible, the built-up area has been declared an "open city" to preclude civilian casualties or to preserve cultural or historical facilities, sufficient combat forces are not available to seize and clear the built-up area.
7. Don’t use tanks on narrow streets! Tanks can be decisive in city fighting, with the ability to demolish walls and fire medium and heavy machine guns in several directions simultaneously. However, tanks are especially vulnerable in urban combat. It’s much easier for enemy infantry to sneak behind a tank or fire at its sides, where it is vulnerable. In addition, firing down from multi-story buildings allows shots at the soft upper turret armor and even basic weapons like Molotov cocktails, if aimed at the engine air intakes, can disable a tank.
8. Use 3 groups at each point.
1st. A "dead" group plus tanks moves fast to the center, again, after intense artillery fire and bombing (otherwise you’ll have heavy casualties).
2nd. The group follows the first one and inside the city goes like a "fan" in all directions enveloping the defender’s flanks and rear.
3rd. The group is on reserve in case the enemy counterattacks.
The first phase of the attack should be conducted when visibility is poor. Troops can exploit poor visibility to cross open areas, gain access to rooftops, infiltrate enemy areas and gain a foothold. If the attack must be made when visibility is good, units should consider using smoke to conceal movement. The formation used in attack depends on the width and depth of the zone to be cleared, the character of the area, anticipated enemy resistance, and the formation adopted by the next higher command. Lead companies may have engineers attached for immediate support. Tasks given to engineers may include preparing and using explosives to breach walls and obstacles, finding and exploding mines in place or helping remove them, clearing barricades and rubble, cratering roads.
9. Use paratroopers to capture important objects (airport, government buildings, military headquarters, port, railway station).
10. Capture high buildings and place machine gunners and snipers on upper floors (buildings provide excellent sniping posts for defenders, too).
11. Get all important cross-roads to maneuver troops and tanks.
12. Block highways!
13. Watch out – there are mines everywhere (alleys and rubble-filled streets are ideal for planting booby traps). Be alert for booby traps in doors, windows, halls, stairs, and concealed in furniture.
14. Watch underground communications – the enemy could stay in subway tunnels, sewage system.
15. Don’t waste time storming the buildings – blow up the walls and move forward.
16. Soldiers in an urban environment are faced with ground direct fire danger in three dimensions — not just all-round fire but also from above (multi-story buildings) and from below (sewers and subways) and that’s why, here, the most survivable systems, like tanks, are at great risk. Also, there are increased casualties because of shattered glass, falling debris, rubble, ricochets, urban fires and falls from heights. Stress-related casualties and non-battle injuries resulting from illnesses or environmental hazards, such as contaminated water, toxic industrial materials also increase the number of casualties.
17. In the streets use artillery and mortars to "soften" the enemy up before assault.
Special forces
Maximum damage, minimum loss.
Special military operations have special requirements:
1. Detailed planning and coordination that allow the special unit to discern and exploit the enemy’s weakness while avoiding its strength.
2. Decentralized execution, individual and unit initiative.
3. Surprise, achieved through the units ability to move by uncommon means, along unexpected routes, over rough terrain, during poor weather and reduced
visibility. Survivability, achieved by rapid mission accomplishment and a prompt departure from the objective area.
4. Mobility, speed, and violence of execution (the speed at which events take place confuses and deceives the enemy as to the intent of the unit, and
forces the enemy to react rather than to take the initiative).
5. Shock effect, which is a psychological advantage achieved by the combining of speed and violence. The special unit strives to apply its full combat
power at he decisive time and place, and at the point of the greatest enemy weakness.
6. Multiple methods of insertion and attack, trying not to repeat operations thus decreasing the chance the enemy will detect a pattern. Deception, achieved by feints, false insertions, electronic countermeasures, and dummy transmissions.
7. Audacity, achieved by a willingness to accept a risk.
Any special team member has to have experience in sniping, underwater swimming, conducting high-altitude, low-opening parachute operations, demolition, using all kinds of weapons, including man-portable air-defense system weapons. And there are some limitations, like limited capability against armored or motorized units in open terrain and no casualty evacuation capability.
Use special forces for:
a) establishing a credible American presence in any part of the world
b) conducting limited combat operations under conditions of chemical, nuclear
or biological contamination
c) surveillance and intelligence gathering using recruited agents too (local citizens who support your war or just work for money). To get to the area you have to use infiltration, the movement into the territory occupied by enemy troops, the contact is avoided.
d) raids on the enemy’s defense system
Raids are normally conducted in the following phases: the team inserts or infiltrates into the objective area; the objective area is sealed off from outside support or reinforcement, to include the enemy air threat; any enemy force at or near the objective is overcome by surprise and violent attack, using all available firepower for shock effect; the mission is accomplished quickly before any surviving enemy can recover or be reinforced; the ranger force quickly withdraws from the objective area and is extracted. (The team can land on or near the objective and seize it before the enemy can react. Thus you avoid forced marches over land carrying heavy combat loads. If there is no suitable landing area near the objective, or the enemy has a strong reaction force nearby, the team has to land unseen far from the objective. It then assembles and moves to the objective).
e) ambush.
Depending on terrain ambushes are divided into near (less than 50 meters, in jungle or heavy woods) and far (beyond 50 meters, in open terrain).
Raids consist of clandestine insertion, brief violent combat, rapid disengagement, swift deceptive withdrawal. The raid is used mostly to destroy command posts, communication centers and supply dumps, shipyards, electrical generation facilities, water pumping stations, phone lines, oil or natural gas pipelines, radio and TV stations, mountain passes or routes in restricted terrain, capture supplies and personnel, rescue friendly forces, distract attention from other operations, steal plans and code books, rescue prisoners of war, create havoc in the enemy’s rear areas, blow railroads and bridges. By blowing bridges you block and delay the movement of personnel and supplies and by making railroads and certain routes temporary useless you change enemy’s movement on to a small number of major roads and railway lines where it is more vulnerable to attack by other forces (especially air strikes).
Stages of an ambush
1. Planning.
You have to identify a suitable killing zone (a place where the ambush will be laid). It’s a place where enemy units are expected to pass
and which gives reasonable cover for the deployment execution and extraction phases of the ambush patrol. Ambush includes 3 main elements: surprise, coordinated fire of all weapons to isolate the killing zone and to inflict maximum damage and control (early warning of target approach, opening fire at the proper time, timely and orderly withdrawal). You can also plan a mechanical ambush, which consists of the mines set in series. Preparation. You have to deploy into the area covertly, preferably at night and establish secure and covert positions overlooking the killing zone. Then you send two or more cut off groups a short distance from the main ambushing group into similarly covert positions they have to give you early warning of approaching enemy by radio and, when the ambush is initiated, to prevent any enemy from escaping. Another group will cover the rear of the ambush position and thus give all-round defense to the ambush patrol. No smoking! Attention: you have to occupy the ambush site as late as possible as this reduces the risk of discovery. (While choosing and ambush site pay attention to natural cover and concealment for your team, routes of entry and withdrawal, good observation and fields of fire, harmless-looking terrain, few enemy escape routes, terrain that will canalize enemy into the killing zone, and natural obstacles to keep him there).
2. Execution.
You must give a clear instruction for initiating the ambush. It should be initiated with a mass casualty producing weapon (mortars and machine guns) to produce a maximum shock effect and break the enemy’s spirit to fight back (shock effect can cover unexpected defects in ambush, like ambushing a much larger force that expected). Then, after the firefight has been won, the ambush patrol has to clear the zone by checking bodies for intelligence and taking prisoners. After that you have to leave the area as soon as possible, by a pre-determined route.
3. Disruption of the government functions: recruitment of informants; terror and murders of political leaders and federal and local government chiefs, provoking strikes and mass disobedience; publishing illegal newspapers and literature; anti-government propaganda through illegal radio stations; involving locals in the guerrilla campaign.
4. Counter-guerrilla.
Guerrilla warfare
Guerrilla warfare is the unconventional warfare and combat with which a small group use mobile tactics (ambushes, raids, etc) to fight a larger and
less mobile regular army. THIS IS ABSOLUTELY WRONG – they sabotage the rear! Same mistake Soviet guerrillas did during World War II, though Chechnya is an example.
Guerrilla tactics are based on intelligence, ambush, deception, sabotage, undermining an authority through long, low-intensity confrontation. A
guerrilla army may increase the cost of maintaining an occupation above what the foreign power may wish to bear. Against a local regime, the guerrillas may make governance impossible with terror strikes and sabotage, and even combination of forces to depose their local enemies in conventional battle. These tactics are useful in demoralizing an enemy, while raising the morale of the guerrillas. In many cases, a small force holds off a much larger and better equipped army for a long time, as in Russia’s Second Chechen War. Guerrilla operations include attacks on transportation routes, individual groups of police and military, installations and structures, economic enterprises and targeted civilians, politicians included. Attacking in small groups, using camouflage and captured weapons of that enemy, the guerrilla force can constantly keep pressure on its foes and diminish its numbers, while still allowing escape with relatively few casualties. The intention of such attacks is not only military but political, aiming to demoralize target populations or governments, or goading an overreaction that forces the population to take sides for or against the guerrillas. Ambushes on key transportation routes are a hallmark of guerrilla operations, causing both economic and political disruption.
Whatever the particular tactics used, the guerrillas primarily fight to preserve his forces and political support, not capture or hold specific territory as a conventional force would.
Guerrilla warfare resembles rebellion, yet it is a different concept. Guerrilla organization ranges from small, local, rebel groups of a few dozen guerrillas, to thousands of fighters, deploying from cells to regiments. In most cases, the leaders have clear political aims for the warfare they wage.
Typically, the organization has political and military wings, to allow the political leaders a plausible denial for military attacks. Guerrillas operate with a smaller logistical footprint compared to conventional formations. A primary consideration is to avoid dependence on fixed bases and depots which are comparatively easy for conventional units to locate and destroy. Mobility and speed are the keys and wherever possible, the guerrilla must live off the land, or draw support from the civilian population in which he is embedded. Financing of operations ranges from direct individual contributions (voluntary or not), and actual operation of business enterprises by insurgent operatives, to bank robberies, kidnappings and complex financial networks based on kin, ethnic and religious affiliation (such as used by Jihad organizations). Permanent and semi-permanent bases form part of the guerilla logistical structure, usually located in remote areas or in cross-border sanctuaries sheltered by friendly regimes. Guerrilla warfare is often associated with a rural setting (mujahedeen and Taliban in Afghanistan, the Contras of Nicaragua). Guerrillas however successfully operate in urban settings (as in Jerusalem, Israel or Baghdad,
Iraq). Rural guerrillas prefer to operate in regions providing plenty of cover and concealment, especially heavily forested and mountainous areas. Urban guerrillas blend into the population and are also dependent on a support base among the people.
Intelligence is very important; collaborators and sympathizers will usually provide a steady flow of information.
Public sources of information and Internet serve very well, too. Intelligence is concerned also with political factors such as occurrence of an election or the impact of the potential operation on civilian and enemy morale.
Able to choose the time and place to strike, guerrillas possess the tactical initiative. Many guerrilla strikes are not undertaken unless clear numerical superiority can be achieved in the target area. Individual suicide bomb attacks offer another pattern, involving only one individual bomber and his support team. Whatever approach is, guerrillas hold the initiative and can prolong their survival through varying the intensity of combat. This means that attacks are spread out over quite a range of time, from weeks to years. During interim periods, the guerrilla can rebuild, resupply, train, provide propaganda indoctrination, gather intelligence, infiltrate into army, police, political parties and community organizations,
Relationships with civil population are influenced by whether the guerrillas operate among a hostile or friendly population. A friendly population is of huge importance to guerrillas, providing shelter, supplies, financing, intelligence and recruits. Popular mass support in a confined local area or country however is not always strictly necessary. Guerrillas can still operate using the protection of a friendly regime, drawing supplies, weapons, intelligence, local security and diplomatic cover. The Al-Qaeda is an example of the latter type, drawing sympathizers and support primarily from the wide-ranging Arab world.
Foreign support (soldiers, weapons, sanctuary or statements of sympathy for the guerrillas can greatly increase the chances of an insurgent victory. Foreign diplomatic support may bring the guerrilla cause to international attention, putting pressure on local opponents to make concessions, or garnering sympathetic support and material assistance. Foreign sanctuaries can add heavily to guerrilla chances, furnishing weapons, supplies, materials and training bases. Such shelter can benefit from international law, particularly if the sponsoring government is successful in concealing its support and in claiming a plausible denial for attacks by operatives based on its territory. Al-Qaeda, for example, made effective use of remote territories, such as Afghanistan under the Taliban regime, to plan and execute its operations.
Terror is used by guerrillas to focus international attention on the guerrilla cause, kill opposition leaders, extort money from targets, intimidate the general population, create economic losses, and keep followers and potential defectors in line. Such tactics may backfire and cause the civil population to withdraw its support, or to back countervailing forces against the guerrillas. Such situations occurred in Israel, where suicide bombings encouraged most Israeli opinion to take a harsh stand against Palestinian attackers, including general approval of targeted killings to kill enemy cells and leaders. Civilians may be attacked or killed for alleged collaboration, or as a policy of intimidation and coercion operations are sanctioned by the guerrilla leaders if they see a political benefit. Attacks may be aimed to weaken civilian morale so that support for the guerrilla opponents decreases. The use of attacks against civilians to create atmosphere of chaos ( and thus political advantage where the atmosphere causes foreign occupiers to withdraw or offer concessions), is well established in guerrilla and national liberation struggles.
Examples of successful guerrilla warfare against a native regime include the Cuban Revolution, Chinese Civil War, Sandinista Revolution in Nicaragua. Many coups and rebellions in Africa reflect guerrilla warfare, with various groups having clear political objectives and using the above mentioned tactics (Uganda, Liberia). In Asia, native or local regimes have been overthrown by guerrilla warfare (Vietnam, China, Cambodia). Unsuccessful examples include Portuguese Africa (Angola, Mozambique and Guinea-Bissau), Malaysia (then Malaya), Bolivia, Argentina and the Philippines. The Liberation Tigers of Tamil Eelam, fighting for an independent homeland in the north and east of Sri Lanka, achieved significant military successes against the Sri Lankan military and the government itself for twenty years. It was even able to use these tactics effectively against the peace keeping force sent by India.
Insurgency
1. Leadership
Insurgency is not simply random political violence; it is directed and focused political violence. It requires leadership to provide vision, guidance, coordination and organizational coherence. The leaders of the insurgency must make their cause known to people. They must gain popular support, and their key tasks are to break the ties between the people and the government and to establish their movement’s credibility. They must replace the government’s legitimacy with that of their own. Their education, background, family, social connections and experience shape how they think, what they want, and how they fulfill their goals. Leadership is both a function of organization and of personality. Some organizations de-emphasize individual personalities and provide mechanisms for rebundancy and replacement in decision making; these mechanisms produce collective power and do not depend on specific leaders or personalities to be effective. They are easier to penetrate but more resilient to change. Other organizations may depend on a charismatic personality to provide cohesion, motivation, and a rallying point for the movement. Leadership organized in this way can produce decisions and initiate new actions rapidly, nut it is vulnerable to disruption if key personalities are removed or co-opted.
2. Ideology.
To win, insurgency must have a program that justifies its actions and explains what is wrong with society. It must promise great improvement after the government is overthrown. Ideology guides the insurgents in offering society a goal. The insurgents often express this goal in simple terms for ease of focus. The insurgent leader can use ideology to justify the use of violence and extralegal action in challenging the current social order, and to form a framework of the program for the future. Ideology identifies those sectors of society which the insurgency targets. Ideology may suggest probable objectives and tactics. It greatly influences the insurgents’perception of his environment. The combination of the insurgents’ ideology and his perception of his environment shapes the movement’s organizational and operational methods.
3. Objectives.
The strategic objective is the insurgents’ desired end state and that is how the insurgent will use power once he has it.
Operational objectives are those which the insurgents pursue as part of the overall process of destroying government legitimacy and progressively establishing their desired end state. The following are examples of operational objectives:
–isolation of the government from diplomatic and material support, and increased international support for the insurgency
–destruction of the self-confidence of the government’s leaders, cadre and armed forces, causing them to abdicate or withdraw
–establishment of civil cervices and administration ion areas under insurgent control
–capture of the support (or neutrality) of critical segments of the population
Tactical objectives are the immediate aims of insurgent acts, for example, the dissemination of a psychological operation product or the attack and seizure of a key facility. These actions accomplish tactical objectives which lead to operational goals.
4. External support.
There are four types of external support:
– moral acknowledgement of the insurgent cause as just and admirable
– political active promotion of the insurgents strategic goals in international forums
– resources money, weapons, food, advisors, training
– sanctuary secure training, operational and logistic bases
5. Organizational and operational patterns.
a)Subversive.
Subversive insurgents penetrate the political structure to control it and use it for their own purposes. They seek elective and appointed offices. They
employ violence selectively to coerce voters, intimidate officials, disrupt and discredit the government. Violence shows the system is incompetent. It
may also provoke the government to an excessively violent response which further undermines its legitimacy. A subversive insurgency most often appears in a permissive political environment in which insurgents can use both legal and illegal methods. The typical subversive organization consists of a legal party supported by a clandestine element operating outside the law. Subversive insurgencies can quickly shift to the critical-cell pattern
when conditions dictate. The Nazi rise to power in the 1930s is an example of this model. Subversive insurgencies primarily present a problem for police and counter-intelligence.
b)Critical-cell.
In the critical-cell, the insurgents also infiltrate government institutions. Their object is to destroy system from within. The moles operate both covertly and overtly. Normally, the insurgents do not reveal their affiliation or program. They seek to undermine institutional legitimacy and convince or coerce others to assist them. Their violence remains covert until the institutions are so weakened that the insurgency’s superior organization seizes power, supported by armed force. The Russian October, 1917 revolution followed this pattern.
There are variations of the critical-cell pattern, too. The first is the co-opting of an essentially leaderless, mass popular revolution. The Sandinistas takeover of the Nicaraguan revolution is a case of point. The insurgent leadership permits the popular revolution to destroy the existing government. The insurgent movement then emerges, activating its cells to guide reconstruction under its direction. It provides a disciplined structure to control the former bureaucracy. The mass popular revolution then coalesces around the structure.
A second variation of the critical-cell pattern is the foco (or Cuban model) insurgency. A foco is a single, armed cell which emerges from hidden strong holds in an atmosphere of disintegrating legitimacy. In theory, this cell is the nucleus around which mass popular support rallies. The insurgents erect new institutions and establish control on the basis of that support. The foco insurgencies are often made up predominantly of guerrilla fighters operating initially from remote enclaves. The Cuban revolution occurred in this manner. The Cuban experience spawned over 200 subsequent imitative revolutionary attempts patterned on it, principally in Latin America and Africa they all failed, but that does not discredit foco theory. It does emphasize the importance of a particular set of circumstances to this model. Legitimacy must be near total collapse, timing is critical. The Nicaraguan insurgency for example, combined the foco with a broad-front political coalition.
c) Mass oriented.
The mass-oriented insurgency aims to achieve the political and armed mobilization of a large popular movement. They emphasize creating a political and armed legitimacy outside the existing system. They challenge that system and then destroy or supplant it. These insurgents patiently build a large armed force of regular and irregular guerrillas. They also construct a base of active and passive political supporters. They plan a protracted campaign of increasing violence to destroy the governments and its institutions from the outside. They organize in detail. Their political leadership normally is distinct from their military leadership. Their movement establishes a rival government which openly proclaims its own legitimacy. They have a well-developed ideology and decide on their own objectives only after careful analysis. Highly organized and using propaganda and guerrilla action, they mobilize forces for a direct military and political challenge to the government. Once established, mass-oriented insurgencies are extremely resilient because of their great depth of organization. Examples of this model include the communist revolution in China, the Vietcong insurgency, the Sendero Luminoso (Shining Path) in Peru.
d)Traditional.
The traditional insurgency normally grows from very specific grievances and initially has limited aims. It springs from tribal, radical, religious or other similarly identifiable groups. These insurgents perceive that the government has denied the rights and interests of their group and work to establish or restore them. The frequently seek withdrawal from government control through autonomy or semi-autonomy. They seldom seek specifically to overthrow the government or to control the whole society. They generally respond in kind to government violence. Their use of violence can range from strikes and street demonstrations to terrorism or guerrilla warfare. These insurgencies may cease if the government accedes to the insurgentsdemands. The concessions of insurgents demands, however, are usually so great that the government concedes its legitimacy along with them. Examples of this model include the Mujahideen in Afghanistan, the Ibo revolt in Nigeria (Biafra), the Tami separatists in Sri Lanka.
No insurgency follows one pattern exclusively.
Typical missions which guerrillas conduct to accomplish their goals include: destroying or damaging vital installations, equipment or supplies; capturing supplies, equipment, or key governmental or military personnel; diverting government forces from other operations; creating confusion and weakening government morale. Remember: guerrilla is a political war, and asymmetric warfare.
Guerrillas are not normally organized or equipped for stand-and-fight type defensive operations. They prefer to defend themselves by moving, by dispersing into small groups, or by diverting the opponent’s attention while they withdraw. Whenever possible, these operations are accomplished by offensive operations against the opponent’s flank or rear. One of the most important needs of guerrilla forces is support, which can come from different sources – food can be stolen or supplied by political sympathizers, weapons can be gathered from raids on government installations or provided by a foreign power (as well as secret training and indoctrination).
Guerrillas strength:
– highly motivated leadership and simple organization. The basic guerrilla organization is an independent three- to five-men cell. The cells can be brought together for larger operations and dispersed later. Guerrillas are organized into cells for two reasons: first, it’s security, second, it’s for support (guerrillas must live off the land to a large degree, and small cells easier support themselves).
– strong belief in a political, religious, or social cause (most of them are fanatics)
– ability to blend with local population and perfect knowledge of environment
– strong discipline
– effective intelligence through penetration into the government agencies
– limited responsibilities (the guerrillas usually don’t have the responsibility to maintain normal governmental obligations toward society)
– the ability to utilize a broad range of tactics, from terror and sabotage through conventional warfare. They don’t hesitate to use bombings, kidnappings, murders, torture, blackmail to press local authorities or provoke overreaction on the part of the government forces, so that the population will be alienated by the government forces actions (it happens when they target government leaders). In cities guerrillas can disrupt public utilities and services by sabotage and the government may lose control of the situation; they can widely use snipers and explosives there. They can generate widespread disturbances, attack government offices, create incidents or massing crowds in order to lure the government forces into a trap.
– mobility. Guerrillas usually disperse during their movements and unite near the target area. The most common techniques employed by them are the ambush, raid and small-scale attacks against security posts, small forces, facilities and lines of communication, using mining, booby trapping and sniping. Targets are selected by the guerrilla based on an analysis of how much the elimination of the target will disrupt the government, what the effect on the populace will be, the risk of being killed or captured, and the amount of weapons or supplies which can be used (this analysis calls for timely intelligence, which is gained by active patrolling).
Guerrilla Weaknesses:
– mental and physical stress, caused by long periods of isolation in an unstable environment
– fear of criminal prosecution by the government, or of reprisals against friends and family
– feeling of numerical and technological inferiority of counter-guerrilla forces
– limited personnel and resources, and uncertain public base of support
– security problems about their base camps (they are usually not more than one day march from a village or town). If guerrillas receive support from external sources, they are faced with a problem of security for supply lines, transport means and storage facilities. Besides, you have to know their organization and plans, resources (arms, ammunition, food and medicine supply), leaders and their personalities, lines of communications, relations with civilian population, vulnerabilities. (Again, recruit, recruit and recruit! ). You have to evaluate also the effects of terrain (including landing and pickup zones) and the weather effect on men, weapons, equipment, visibility and mobility.
Urban guerrilla warfare has its own peculiarities. Cities and towns arevulnerable to urban guerrilla because they are the focus of economic and political power. In many cases, public utilities can be disrupted and the government may appear to have lost control of the situation. The concentration of a large number of people in a relatively small area provides cover for the guerrilla. However, the insurgent may find support only in a certain areas of a town or a city. Anyway, the urban guerrilla lives in a community that is friendly to him or is too frightened to withhold its support or betray him. In a city the snipers and explosive devices can be placed everywhere. The availability of large numbers of people ensures that crowds can be assembled and demonstrations manipulated easily. The presence of women and children restricts counter-guerrilla force reactions, and excessive force may ensure a major incident that provides the guerrilla with propaganda. Publicity is easily achieved in an urban area because no majorincident can be concealed from the local population even if it is not widely reported by the news media. Every explosion may be exploited to discredit the ability of the government to provide protection and control.
Urban guerrilla tactics:
– disrupting industry and public services by strikes and sabotage
– generating widespread disturbances designed to stretch the resources of the counter-guerrilla force
– creating incidents or massing crowds in order to lure the counter-guerrilla into a trap
– provoking the counter-guerrilla force in the hope that it may overreact (to provide hostile propaganda after that)
– fomenting interfactional strife
– sniping at roadblocks, outposts and sentries
– attacking buildings with rockets and mortars
– planting explosive devices, either against specific targets or indiscriminately, to cause confusion and destruction, and to lower public morale
–ambushing patrols and firing on helicopters
COUNTER-GUERRILLA WARFARE
1. Since many insurgents rely on the population for recruits, food, shelter, financing, you must focus your efforts on providing physical and economic
security for that population and defending it against insurgent attacks and propaganda.
2. There must be a clear political program that can neutralize the guerrilla program this can range from granting political autonomy to economic development measures in the affected region + an aggressive media campaign.
3. You have to clean and re-build all levels of the government structure usually insurgents talk about corrupted politicians a lot and that’s why they have support from population.
4. You don’t have to overreact to guerrilla actions, because this is what they are looking for.
5. Use big military operations only to break up significant guerrilla concentrations and split them into small groups.
6. Keep insurgents on run constantly with aggressive patrols, raids, ambushes, sweeps, cordons, roadblocks, prisoner snatches. Intelligence and
recruitment of informants is the key to success. (KGB in post WWII period used bogus guerrilla groups in Western Ukraine that helped reveal real insurgents).
7. An ink spot clear and hold strategy must be used to divide the conflict area into sectors and assign priorities between them. Control must
expand outward like an ink spot on paper, systematically neutralizing and eliminating the insurgents in one sector of the grid, before proceeding to the next. It may be necessary to pursue holding or defensive actions elsewhere, while priority areas are cleared and held.
8. Mass forces, including village self-defense groups and citizen militias organized for community defense can be useful in providing civic mobilization and local security.
9. Use special units and hunter-killer patrols.
10. The limits of foreign assistance must be clearly defined and carefully used. Such aid should be limited either by time, or as to material and technical, and personnel support, or both. While outside aid or even troops can be helpful, lack of clear limits, in terms of either a realistic plan for
victory or exit strategy, may find the foreign helper taking over the local war, and being sucked into a lengthy commitment, thus providing the guerrillas with valuable propaganda opportunities as the stream of dead foreigners mounts. Such scenario occurred with United States in Vietnam and
since 2003 in Iraq.
11. A key factor in guerrilla strategy is a drawn-out, protracted conflict, which wears down the will of the opposing counter-insurgent forces. Democracies are especially vulnerable to the factor of time, but the counter-insurgent force must allow enough time to get the job done.
Tactical counter-guerrilla operations
1. Encirclement, which is designed to cut off all ground routes for escape and reinforcement of the encircled force (darkness recommended) combined with combined with air assault, artillery and airborne troops. And it’s good to divide the enemy while encircling.
Encirclement offers the best chance to fix guerrilla forces in position and achieve decisive results. The battalion and larger units will usually plan and conduct encirclements. The company and smaller units normally do not have the manpower and command and control capability to execute encirclements except as part of a larger force. Encirclements require accurate intelligence on the location of guerrilla elements. Since it requires a major portion of the counterguerrilla force to execute this maneuver, it is usually targeted against large guerrilla forces or guerrilla base complexes, a series of smaller base camps clustered within area. Planning, preparation and execution are aimed at encircling the guerrilla force rapidly. Maximum security and surprise can be gained by occupying the initial encirlclement positions during darkness. In large operations, air assault and airborne troops add speed and surprise to the operation. Positions are occupied simultaneously in order to block escape. If simultaneous occupation is not possible, probable escape routes are covered first. Initial occupation is the most critical period of the operation. When the guerrillas become aware that they are being encircled, they will probably probe for gaps or attack weak points and attempt to break out.
Encircling units provide strong combat patrols far to their front to give early warning of attempted breakouts. Mobile reserves are positioned to counter a breakout and to reinforce difficult areas such as broken terrain or areas with caves, tunnels or fortification complexes. Indirect fire support can serve to cloak an encirclement by gaining and holding the guerrillas attention. Fires are planned in detail to support the encirclement. Following completion of the encirclement, the circle is contracted to capture or destroy the guerrilla force. AS the circle is contracted, units may be removed from the line and added to the reserve. Against small guerrilla forces, the encircled area may be cleared by contraction and a final sweep. Against larger guerrilla forces, however, at some point, some action other than contraction will be required. One technique consists of driving a wedge through the guerrilla force to divide it and then destroying the guerrillas in each subarea. Another technique, employed after some degree of contraction, is to employ a blocking force on one or more sides of the perimeter while the remainder of the encircling force drives the guerrillas against blocking force. Either element may accomplish the actual destruction.
The technique is effective when the blocking force can be located on, or immediately in the rear of, a natural terrain obstacle.
2. Search (of a village), which might be done in different ways:
– assemble inhabitants in a central location (if they are hostile) and then start the operation
– restrict inhabitants to their homes or control the heads of households (and take other family members to a central location) and then start the convoy security operation, which is one of your top priorities.
Think about ambushes and mines on the route all the time and place a strong attack element at the rear of the convoy where it has maximum flexibility in
moving forward to attack guerrillas attempting to ambush the head or center of the convoy. At the first indication of an ambush vehicles have to move out of the killing zone (do not drive to roadsides or shoulders, which may be mined). A security team immediately returns fire from inside vehicles to cover dismounting personnel (if you have to stop) and then dismounts last under cover of the fire by those who dismounted first. Upon dismounting, personnel caught in a killing zone open fire and immediately assault toward the ambush force. Any movements of the troops and supplies are planned and conducted as tactical operations with effective front, flank and rear security.
Search techniques in built-up areas are required when you search either a few isolated huts or buildings, or for searching well-developed urban sections.
Procedure :
a) divide the area to be searched into zones, and assign a search party to each. A search party consists of a search element (to conduct the search), a security element (to encircle the area and prevent entrance and exit, and to secure open areas), and a reserve element (to assist, as required). Then the search element conducts the mission assigned for the operation. Normally it is organized into special teams. The security element surrounds the area while the search element moves in. Members of the security element orient primarily upon evaders from the populated area; however, they can cut off any insurgents trying to reinforce. Checkpoints and roadblocks are established. Subsurface routes of escape, such as subways and sewers, must be considered when operating in cities. The reserve element is a mobile force within a nearby area. Its specific mission is to assist the other two elements should they meetresistance they cannot handler. In addition, it is capable of replacing or reinforcing either of the other two elements should the need arise.
b)consider any enemy material found, including propaganda signs and leaflets, to be booby-trapped until inspection proves it is safe.
c) thoroughly search underground and underwater areas. Any freshly excavated ground can be a hiding place. Use mine detectors to locate metal objects underground and underwater.
d) deploy rapidly, especially when a guerrilla force is still in the area to be searched. The entire area to be searched is surrounded simultaneously. If this is not possible, observed fire must cover that portion not covered by soldiers.
3. Ambush.
An ambush is a surprise attack from a concealed position upon a moving or temporary halted target. Ambushes give the counter-guerrilla force several advantages:
a) an ambush does not require ground to be seized or held
b) smaller forces with limited weapons and equipment can harass or destroy larger, better armed forces
c) guerrillas can be forced to engage in decisive combat at unfavorable times and places
d) guerrillas can be denied freedom of movement and deprived of weapons and equipment that are difficult to replace.
Well-planned and well-executed ambushes is the most successful operational technique employed against guerrillas. It is an effective technique to interdict movement guerrilla forces within an area. Selection of the site is a key step in developing a well-organized ambush.
Ambushes are executed to reduce the guerrillas overall combat effectiveness. Destruction is the primary purpose of an ambush since guerrillas killed or captured, and equipment and supplies destroyed or captured, critically affect the guerrilla force. Harassment, the secondary purpose, diverts guerrillas from other missions. A series of successful ambushes causes the guerrilla force to be less aggressive and more defensive, to be apprehensive and overly cautious, and to be reluctant to go on patrols and move in convoys or in small groups.
There are three types of ambushes.
A point ambush involves patrol elements deployed to support the attack of a single killing zone. An area ambush involves patrol elements deployed as multiple, related, point ambushes. An ambush is categorized as either hasty or deliberate.
A hasty ambush is an immediate action drill, an action of a combat patrol with little or no information. When information does not permit detailed planning required for a deliberate ambush, a hasty ambush is planned. In this case, ambush patrol plans and prepares to attack the first suitable guerrilla force. A deliberate ambush is planned as a specific action against a specific target. Detailed information of the guerrilla force is required: size, nature, organization, armament, equipment, route and direction of movement, and time the force will reach or pass certain points on its route. Deliberate ambushes are planned when reliable information is received on the intended movement of a specific force; patrols, convoys, carrying parties or similar forces establish patterns of size, time and movement sufficient to permit detailed planning for the ambush.
Basic elements of an ambush are:
1. Surprise. It has to be achieved or else the attack is not an ambush. Surprise, which distinguishes an ambush from other forms of attack, allows
the ambush force to seize and retain control of the situation. Surprise is achieved by careful planning, preparation and execution. Guerrillas are attacked in a manner they least expect.
2. Coordinated fires. All weapons, including mines and demolitions, are positioned, and all direct and indirect fires are coordinated to achieve
isolation of the kill zone to prevent escape or reinforcement; surprise delivery of a large volume of concentrated fires into the kill zone to inflict maximum damage so the target can be assaulted and destroyed.
3. Control. Close control is maintained during movement to, occupation of, and withdrawal from the ambush site. The ambush commander’s control of all
elements is critical at the time of target approach. Control measures provide for early warning of target approach, withholding fire until the target moves into the kill zone, opening fire a the proper time, initiating appropriate actions if the ambush is prematurely detected, lifting or shifting supporting fires when the ambush includes assault of the target, timely and orderly withdrawal to an easily recognized rallying point.
Planning
Planning provides for simplicity, type of ambush and deployment. The attack may be by fire only (harassing ambush) or may include assault of the target (destruction ambush). The force is tailored for its mission. Two men may be adequate for a harassing ambush. A destruction ambush may require the entire unit (squad, platoon, company).
An ambush patrol is organized in the same manner as other combat patrols to include headquarters, an assault element, a support element and a security element. The assault and support are the attack force; the security element is the security force. When appropriate, the attack force is further organized to provide a reserve force. When an ambush site is to be occupied for an extended period, double ambush forces may be organized. One ambush force occupies the site while the other rests, eats and tends to personal needs at the objective rallying point or other concealed location. They alternate after a given time, which is usually 8 hours. If the waiting period is over 24 hours, three ambush forces may be organized.
The selection of equipment and supplies needed is based on the mission, size of guerrilla force, means of transportation, distance and terrain, weight and bulk of equipment. A primary route is planned which allows the unit to enter the ambush site from the rear. The kill zone is not entered if entry can be avoided. If the kill zone must be entered to place mines or explosives, care is taken to remove any tracks or signs that might alert the guerrillas and compromise the ambush. If mines, mantraps or explosives are to be placed on the far side, or if the appearance of the site might cause the guerrillas to check it, then a wide detour around the killing zone is made. Here, too, care is taken to remove any traces which might reveal the ambush.
Also, an alternate route from the ambush site is planned.
Maps and aerial photos are used to analyze the terrain. As far as possible, so-called ideal ambush sites are avoided. Alert guerrillas are suspicious of these areas, avoid them and increase vigilance and security when they must be entered. Considering this, an ambush site must provide fields of fire, concealed positions, canalization of the guerrillas into the killing zone, covered routes of withdrawal ( to enable the ambush force to break contact and avoid pursuit), no-exit route for the guerrilla force.
Ambush force, as a rule occupies the ambush site at the latest possible time permitted by the tactical situation and the amount of site preparation required. This not only reduces the risk of discovery but also reduces the time that soldiers must remain still and quiet in position.
The unit moves into the ambush site from the rear. Security elements are positioned first to prevent surprise while the ambush is being established.
Automatic weapons are then positioned so that each can fire along the entire killing zone. If this is not possible, they are given overlapping sectors of
fire so the entire killing zone is covered. The unit leader then selects his position, located where he can see when to initiate the ambush. Claymore mines, explosives and grenade launchers may be used to cover any dead space left by the automatic weapons. All weapons are assigned sectors of fire to provide mutual support. The unit leader sets a time by which positions are to be prepared. The degree of preparation depends on the time allowed. All men work at top speed during the allotted time. Camouflage is very important each soldier must be hidden from the target and each one has to secure his equipment to prevent noise. At the ambush site, positions are prepared with minimal change in the natural appearance of the site. All debris resulting from preparation of positions is concealed. Movement is kept to a minimum and the number of men moving at a time is closely controlled. Light discipline is rigidly enforced at night.
Point ambush
A point ambush, whether independent or part of an area ambush, is positioned along the expected route of approach of the guerrilla force.
Formation is important because, to a great extent, it determines whether a point ambush can deliver the heavy volume of highly concentrated fire necessary to isolate, trap and destroy the guerrillas. The formation to be used is determined by carefully considering possible formations and theadvantages and disadvantages of each in relation to terrain, conditions of visibility, forces, weapons and equipment ease or difficulty of control, force to be attacked and overall combat situation.
1. Line formation.
The attack element is deployed generally parallel to the guerrilla forces route of movement (road, trail, stream). This positions the attack element parallel to the long axis of the killing zone and subjects the guerrilla force to heavy flanking fire. The size of the force that can be trapped in the killing zone is limited by the area which the attack element can effectively cover with highly concentrated fire. The force is trapped in the killing zone by natural obstacles, mines, demolitions, and direct and indirect fires. A disadvantage of the line formation is the chance that lateral dispersion of the force may be too big for effective coverage. The line formation is appropriate in close terrain that restricts guerrilla maneuver and in open terrain where one flank is restricted by mines, demolitions or mantraps. Similar obstacles can be placed between the attack element and the killing zone to provide protection from guerrilla counter-ambush measures. When a destruction ambush is deployed in this manner, access lanes are left so that the force in the killing zone can be assaulted. The line formation can be effectively used by a rise from the ground ambush in terrain seemingly unsuitable for ambush. An advantage of the line formation is its relative ease of control under all conditions of visibility.
2. L-formation.
The L-formation is a variation of the line formation. The long side of the attack element is parallel to the killing zone and delivers flanking fire.
The short side of the attack element is at the end of, and at right angles to, the killing zone and delivers enfilading fire that interlocks with fire from the other leg. This formation is flexible. It can be established on a straight stretch of a trail or stream or at a sharp bend in a trail or
stream. When appropriate, fire from the short leg can be shifted to parallel the long leg if the guerrilla force attempts to assault or escape in the opposite direction. In addition, the short leg prevents escape in that direction or reinforcement from that direction.
3. Z-formation.
The Z-shaped formation is another variation of the L-formation. The attack force is deployed as in the L-formation but with an additional side so that the formation resembles the letter Z. The additional side may serve to engage a force attempting to relieve or reinforce the guerrillas, restrict a flank, prevent envelopment (of the ambush force), seal the end of the killing zone.
4. T-formation.
The attack element is deployed across, and at right angles to, the route of movement of the hostile force so that the attack element and the target form
the letter T. This formation can be used day or night to establish a purely harassing ambush, and at night to establish an ambush to interdict movement through open, hard-to-seal areas (such as rice paddies). A small unit can use the T-formation to harass, slow and disorganize a larger force. When the lead guerrilla elements are engaged, they will normally attempt to maneuver right or left to close with the ambush force. Mines, mantraps and other obstacles
placed to the flanks of the killing zone slow the guerrillas movement and permit the unit to deliver heavy fire and then withdraw without becoming decisively engaged. The T-formation can be used to interdict small groups attempting night movement across open areas. For example, the attack element may be deployed along a rice paddy dike with every second member facing in the opposite direction. The attack of a force approaching from either direction requires only that every second member shift to the opposite side of the dike. Each member fires only to his front and only when the target is at a close range. Attack is by fire only, and each member keeps the guerrilla force under fire as long as it remains to his front. If the force attempts to
escape in either direction along the dike, each member takes it under fire as it comes into his vicinity. The T-formation is effective at halting infiltration. It has one chief disadvantage: there is a possibility that while spread out the ambush will engage a superior force. Use of this formation must, therefore, fit the local enemy situation.
5. V-formation.
The V-shaped attack element is deployed along both sides of the guerrilla route of movement so that it forms a V. Care is taken to ensure that neither group (or leg) fires into the other. This formation subjects the guerrilla to both enfilading and interlocking fire. The V-formation is suited for fairly open terrain but can also be used in the jungle. When established in the jungle, the legs of the V close in as the lead elements of the guerrilla force approach the apex of the V, elements then open fire from close range. Here, even more than in open terrain, all movement and fire is carefully coordinated and controlled to ensure that the fire of one leg does not endanger the other. Wider separation of the elements makes this formation difficult to control, and there are fewer sites that favor its use. Its main advantage is that it is difficult for the guerrilla to detect the ambush until well into the killing zone.
6. Triangle formation.
Closed triangle. The attack element is deployed in 3 groups, positioned so they form a triangle (or closed V). An automatic weapon is placed at each
point of the triangle and positioned so that it can be shifted quickly to interlock with either of the others. Elements are positioned so that their fields of fire overlap. Mortars may be positioned inside the triangle. When deployed in this manner, the triangle ambush becomes a small unit strongpoint which is used to interdict night movement through open areas, when guerrilla approach is likely to be from any direction. The formation provides all-round security, and security elements are deployed only when they can be positioned so that, if detected by an approaching target, they will not compromise the ambush. Attack is by fire only, and the target is allowed to approach within close range before the ambush force opens fire. Advantages include ease of control, all-round security, and guerrillas approaching from any direction can be fired on by at least two automatic weapons. Disadvantages include the requirement for an ambush force of platoon size or larger to reduce the danger of being overturn by a guerrilla force; one or more legs of the triangle may come under guerrilla enfilade fire; and lack of dispersion, particularly at the points, increases danger from guerrilla mortar fire.
Open triangle (harassing ambush).
This variation of the triangle ambush is designed to enable a small unit to harass, slow, and inflict heavy casualties upon a larger force without being decisively engaged. The attack group is deployed in 3 elements, positioned so that each element becomes a corner of a triangle containing the killing zone. When the guerrillas enter the killing zone, the element to the guerrillas front opens fire on the lead guerrillas. When the guerrillas counterattack, the element withdraws and an assault element to the flank opens fire. When this group is attacked, the element to the opposite flank opens fire. This process is repeated until the guerrillas are pulled apart. Each element reoccupies its position, if possible, and continues to inflict maximum damage without becoming decisively engaged.
Open triangle (destruction ambush).
The attack group is again deployed in 3 elements, positioned so that each element is a point of the triangle, 200 to 300 meters apart. The killing zone is the area within the triangle. The guerrillas are allowed to enter the killing zone; the nearest element attacks by fire. As the guerrillas attempt to maneuver or withdraw, the other elements open fire. One or more assault elements, as directed, assault or
maneuver to envelop or destroy the guerrillas. As a destruction ambush, this formation is suitable for platoon-size or larger units; a unit smaller than a platoon would be in danger of being overrun. Also, control in assaulting or maneuvering is difficult. Close coordination and control are necessary to ensure that assaulting or maneuvering elements are not fired by another party; and the ambush site must be a fairly level, open area that provides (around its border) concealment for the ambush elements (unless it is a rise from the ground ambush).
7. Box formation.
This formation is similar in purpose to the open triangle ambush. The unit is deployed in 4 elements positioned so that each element becomes a corner of a square or rectangle containing the killing zone. It can be used as a harassing ambush or a destruction ambush in the same manner as the two variations of the open triangle ambush.
Area ambush
Killing zone. A point ambush is established at a site having several trails or other escape routes leading away from it. The site may be a water hole, guerrilla campsite, or known rendezvous point, or a frequently traveled trail. This site is the central killing zone.
Area ambush multiple point.
Point ambushes are established along the trails or other escape routes leading away from the central killing zone. The guerrilla force, whether a single group or several parties approaching from different directions, is permitted to move to the central killing zone. Outlying ambushes do not attack (unless discovered). The ambush is initiated when the guerrillas move into the central killing zone. When the guerrillas break contact and attempt to disperse, escaping portions are intercepted and destroyed by the outlying ambushes. The multiple point ambush increases casualties and harassment and produces confusion.
This version of the area ambush is best suited in terrain where movement is largely restricted to trails. It provides best results when established as a deliberate ambush. When there is not sufficient intelligence for a deliberate ambush, an area ambush of opportunity (hasty ambush) may be established. The outlying ambushes are permitted to attack guerrillas approaching the central killing zone, if the guerrilla force is small. If it is too large for the particular outlying ambush, the guerrillas are allowed to continue and they are attacked in the central killing zone.
Area ambush: baited trap.
A variation of the area ambush. A central killing zone is established along the guerrillas route of approach. Point ambushes are established along the routes over which units relieving or reinforcing the guerrilla will have to approach. The guerrilla force in the central killing zone serves as a bait to lure relieving or reinforcing guerrilla units into the kill zones of the outlying ambushes. A friendly force can also be used as the bait. The outlying point ambushes need not be strong enough to destroy their targets. They may be small harassing ambushes that delay, disorganize and cause casualties by successive contacts.
This version can be varied by using a fixed installation as bait to lure relieving or reinforcing guerrilla units into the killing zone to overcome the installation or may use it as a ruse. These variations are best suited for situations where routes of approach for relieving or reinforcing guerrilla units are limited to those favorable for ambush.
Unusual ambush techniques
Spider hole ambush.
This point ambush is designed for open areas that lack cover and concealment and other features normally desirable in a good ambush site. The attack element is deployed in the formation best suited to the overall situation. The attack element is concealed in the spider hole type of covered foxhole. Soil is carefully removed and positions camouflaged. When the ambush is initiated, the attack element members throw back the covers and rise from the ground to attack. This ambush takes advantage of the tendency of patrols and other units, to relax in areas that do not appear to favor ambush. The chief advantage is that the ambush element is vulnerable if detected prematurely.
Demolition ambush.
Dual primed, electrically detonated mines or demolition charges are planted in the area over which a guerrilla force is expected to pass. This may be a portion of as road or trail, an open field, or any area that can be observed from a distance. Activating wires are run to a concealed observation point sufficiently distant to ensure safety of the ambush element. As large a force as desired or necessary can be used to mine the area. The ambush element remains to fire the charges, other personnel return to the unit. When a guerrilla force enters the mined area (killing zone), the element on site detonates the explosives and withdraws immediately to avoid detection and pursuit.
Special ambush situation.
Attacks against columns protected by armored vehicles depend on the type and location of armored vehicles in a column, and the weapons of the ambush force. If possible, armored vehicles are destroyed or disabled by fire or antitank weapons, landmines and Molotov cocktails, or by throwing hand grenades into open hatches. An effort is made to immobilize armored vehicles at a point where they are unable to give protection to the rest of the convoy and where they will block the route of other supporting vehicles. In alternate bounds, all except the first two vehicles keep their relative places in the column. The first two vehicles alternate as lead vehicles on each bound. Each covers the bound of the other. This method
provides more rapid advance than movement by successive bounds but is less secure it doers not allow soldiers in the second vehicle enough time to thoroughly observe the terrain to the front before passing the first vehicle. Security is obtained by the vehicle commander who assigns each soldier a direction of observation: to the front, flank(s) or rear. This provides each vehicle with some security against surprise fire from every direction and provides visual contact with vehicles to the front and rear. For maximum observation, all canvas is removed from the vehicles.
Action at danger areas.
The commander of the leading vehicle immediately notifies the unit leader when he encounters an obstacle or other danger area.
Designated soldiers reconnoiter these places under cover of the weapons in the vehicle. Obstacles are bypassed, if possible. When they cannot be bypassed, they are cautiously removed. Side roads intersecting the route of advance are investigated. Soldiers from one vehicle secure the road junction; one or two vehicles investigate the side road. The amount of reconnaissance of side roads is determined by the patrol leaders knowledge of the situation. Men investigating side roads do not, however, move past supporting distance of the main body of the patrol. Bridges, road junctions, defiles and curves (that deny observation beyond the turn) are danger areas. Soldiers dismount and take advantage of available cover and concealment to investigate these areas. The vehicle is moved off the road into a covered or concealed position; weapons from the vehicle cover the advance of the investigating personnel.
Ambush during darkness is difficult to control, bur darkness increases the security of the ambush party and the confusion of those being ambushed.
4. Roadblocks and checkpoints.
Element of the checkpoint force has to be positioned and concealed at appropriate distance from the checkpoint to prevent the escape of any vehicle or person attempting to turn back.
It’s necessary to maintain a continuous check on road movement to apprehend suspects and to prevent smuggling of controlled items. Since checkpoints cause considerable inconvenience and even fear, it’s important that the civil population understands that checkpoints are a preventive and not a punitive measure. Checkpoints may be deliberate or hasty. The deliberate checkpoint is positioned in a town or in the open country, often on a main road. It acts as a useful deterrent to unlawful movement. The hasty checkpoint is highly mobile and is quickly positioned in a town or in the open country. The actual location of the hasty checkpoint is designed to achieve quick success.
Concealment of a checkpoint is desirable, but often impossible. The location should make it difficult for a person to turn back or reverse a vehicle without being observed. Culverts, bridges or deep cuts may be suitable locations. Positions beyond sharp curves have the advantage that drivers do not see the checkpoint in sufficient time to avoid inspection. Safety disadvantages may outweight the advantages of such positions. A scarcity of good roads increases the effect of a well-placed checkpoint. A checkpoint requires adequate troops to prevent ambush and surprise by a guerrilla force.
5. Patrols.
Used to saturate areas of suspected guerrilla activity, control critical roads, maintain contact between villages and units, interdict guerrilla routes of supply and communication, provide internal security in rural and urban areas, locate guerrilla units and base camps. A patrol is a
detachment sent out by a larger unit to conduct a combat or reconnaissance operation. Patrolling is used when limited (or no) intelligence on guerrilla activity is available. Routes are planned carefully and coordinated with higher, lower and adjacent units, to include air and ground fire support elements and reserve forces. There are three key principles to successful patrolling: detailed planning, thorough reconnaissance, all-round security.
It often happens that the patrol has to break the contact with a larger enemy (to break contact use the clock system. the direction the patrol moves is
always 12 o’clock. When contact is made, the leader shouts a direction and distance to move (such as 7 o’clock, 400 meters. The leader can also use the system to shift or direct fire at a certain location).
Saturation patrolling is extremely effective patrols are conducted by many lightly armed, small, fast-moving units and provide thorough area coverage. Patrols move over planned and coordinated routes which are engaged frequently to avoid establishing patterns. Use of saturation patrolling results in the sustained denial of an area to guerrilla forces as they seek to avoid contact with the counter-guerrilla units. In addition to harassment and discovery of guerrilla tactical forces, this technique provides an opportunity to gain an intimate knowledge of the area of operations; a form of reassurance to the local population that the government is concerned about their protection and security; a means by which information about the guerrilla can be obtained.
Watch out: guerillas usually try to cut the lines of communications by mining roads, waterways and railways, or by ambushes located adjacent to them, blow up bridges and tunnels.
Psychological Operations
Psychological operations (PSYOP) in foreign internal defense include propaganda and other measures to influence the opinions, emotions, attitudes, and behavior of hostile, neutral, or friendly groups to support the achievement of national objectives. There are 5 major target groups for PSYOP:
1. Insurgents.
The major PSYOP objective here is to discredit the insurgents and isolate them from he population. The most important direction of attack
is against their morale. Themes should publicize and exploit differences between cadre, recruits, supporters, and the local population. Other themes might stress lack of support, isolation, homesickness, and hardship. Amnesty programs are often useful in neutralizing insurgents, and they are most effective when they are well publicized, directed against lower ranking members of the insurgency, and offer sufficient reason and benefits for quitting the unit. These programs do, however, have several disadvantages: they recognize the insurgents as a legitimate political force, they forgo punishment of anyone accepting amnesty, and they increase the image of the insurgents threat.
2. The population supporting the insurgents.
You have to achieve withdrawal of support for the insurgents and a total defection. Propaganda should highlight the insurgents shortcomings, ultimate government victory, government successes, and the practical advantages of surrendering or of accepting amnesty. Sometimes, displays of military might are used; invading forces may assemble and parade through the streets of conquered towns, attempting to demonstrate the futility of any further fighting. Thesedisplays may also include public executions of enemy soldiers, resistance fighters, and other conspirators. Particularly in antiquity, the death or imprisonment of a popular leader was sometimes enough to bring about a quick surrender. However, this has often had the unintended effect of creating martyrs around which popular resistance can rally.
3. The uncommitted population.
The major mission here is to build national morale, unity, and confidence in the government. There should also be a major
effort to win popular acceptance of the government force, and convince the people that government programs serve their interests, the government forces
can protect them, ultimate government victory is assured. This may be accomplished through re-education, allowing conquered citizens to participate in their government, or, especially in impoverished or besieged areas, simply by providing food, water and shelter.
4. Government personnel.
When targeting government personnel, seek to maintain loyalties and develop policies and attitudes which will result in
group members who will realize the importance of popular support, promote public welfare and justice, take action to eliminate the basic causes of the
subversive insurgency, and protect the population. You have to indoctrinate the host country security and military forces regarding the importance of the civilian population support. When government personnel interact with neutral and non-hostile elements of the population, the emphasis should be positive
and constructive.
5. Foreign audiences. There are two major groups to be addressed: neutral nations and hostile nations. For neutral nations, the purpose of
psychological operations is to achieve friendly neutrality or active support for your side. For hostile powers, the major objective of these operations is
to influence public opinion against involvement in supporting the insurgency. Besides, you have to use psychological operations to establish and maintain a
favorable image of our country. The themes most useful in establishing that image are that the US presence is requested by the host country government, it is legal and necessary, it is temporary, and it is advisory. Intelligence operations are facilitated by employing psychological operation media to inform the people that they should report to the proper authority information
pertaining to strangers, suspicious persons, and guerrilla activities. Posters and leaflets provide definite instruction as to persons and places that are available to receive the information (indicate what rewards are available).
Vietnam experience
The Viet Cong used hit and run attacks involving a small group, usually hiding in ambush and attacking a larger force, only to retreat
seconds later. This reduced the advantages of the conventional forces advanced weapon systems. It gave an ambushed squad no time to call in artillery or air strike. Booby traps ( like simple spikes, incorporated into various types of traps, for example, in camouflaged pit into which a man might fall) were another common tactic among guerrillas. Grenade traps (poised with the pin removed) were also used. Moving them would take the pressure off the lever, causing the grenades to explode. Camouflage was very important, and fighters travelled in small groups, often wearing civilian clothes to make it difficult for American soldiers to know who they were.
Often, they would in tunnels underground. Tunnels and spider holes were often used to spring ambushes on American troops. The Vietcong would wait for part of American formation to pass before coming out of the ground and opening fire. Before the Americans had a chance to realize where the fire
came from, the Vietcong would duck back into the trenches. This often caused fratricide (friendly fire incident) because soldiers who were ambushed would
fire back behind them, hitting other American patrols. American troops, usually assigned to Vietnam for a one-year tour of duty, found themselves
ill-trained to wage a war against a mostly invisible enemy.
Afghanistan experience
When the Stinger missile was introduced to Mujahideen, they began to ambush Soviet helicopters and fixed wing aircraft at airfields. The Stinger was
effective only up to 15, 000 feet (4, 600 m), so Mujahideen would attack aircraft as they were landing or taking off. Soviets modified their tactics:
helicopters stayed over friendly forces, fixed wing aircraft began flying higher, and armor and electronic defense systems were added to aircraft to help protectthem from Stinger. Also, Spetsnaz ( Special Forces) were used extensively. They would be flown into areas where Mujahideen often passed,
had been seen or were ambushing someone. Tanks and aircraft were of comparatively little use. The only technology with a significant impact on
Mujahideen were land mines and helicopters. As the Soviets got stalled, they began punishing the local population for supporting Mujahideen. It was not
uncommon for Soviet helicopters to raze an Afghan village in retaliation for an attack against Soviet soldiers. They also dropped mines from aircraft in
fields and pastures and shot livestock with machineguns. Another common tactic was to cordon off and search villages for Mujahideen.
Chechnya (Russia) experience
The conflict between Russia and Chechen terrorists has been mostly a guerilla war. Most fighting was done with the support of armored vehicles,
artillery and aircraft, rather than infantry. Russian soldiers were not prepared for urban warfare in Grozny (the capital of Chechnya). Terrorists would hide on the top floors and basements of buildings armed with small arms and anti-tank weapons. The Russians came in with convoys of armored vehicles which were unprepared for the tactics the terrorists would use. Chechenambush tactics were planned, and involved destroying the first and the last vehicle (armored personnel carrier or a tank) in the column. This was done by either rocket propelled grenade (RPG) or improvised explosive device. If the initial attack was successful, the rest of the convoy would be trapped in between. Later Russians used artillery and airstrikes more extensively.
Terrorists changed their urban combat tactics and used fire-teams of three fighters : a machine gunner, a sniper and a fighter armed with rocket propelled grenade. As a result, a very small and mobile fire-team could meet any potential sizable threat with great effectiveness. Chechen snipers used to wound Russian soldiers and pick off their rescuers. They also shot off antennas from the moving armored personnel carriers since this was often the only means of communication with the command center, the troops inside would end up isolated and attacked with RPG or by the sniper as they tried to repair the antenna. As Russia controlled more area, ambushes gave place to roadside bombings, and these usually involved modified mines and improvised explosive devices.
U. S. – Iraq war experience
Suicide bombers attack American soldiers at checkpoints, on patrols, on their bases and in convoys. Iraqis used the same tactics Chechen terrorists
used against convoys.
Book 5. TERROR AND COUNTERTERROR
By Mikhail Kryzhanovsky
Terrorism is the unlawful use of violence (t e r r o r) against people or property to coerce or intimidate governments or societies, often to achieve political, religious or ideological objectives. It’s also a form of unconventional and psychological warfare. The common strategy of terrorists is to commit acts of violence. Each act of terrorism is a violent act, devised to have a big national or international impact. Terrorism is a political tactic. “Red” terror is aimed against certain politicians; “black” refers more to mass murders. The two can be mixed.
Purposes: to scare the nation, neutralize the government and show its inability to rule the country; to make the government admit that terror organization is a real political power; to draw media and public (international) attention to a certain political problem, to provoke the government to use military force and start civil war; to prove some political or religious ideology; prevent or delay important political decisions or legislation; discourage foreign investments or foreign government assistance programs; change the government through revolution or civil war.
Types of terrorism.
Civil disorders.
Political terrorism – violent acts designed primarily to generate fear in the nation for political purposes. Civil disorders are very effective here..
Non-political terrorism – terrorism that is not aimed at political purposes but which exhibits conscious design to create and maintain high degree of fear for coercive purposes..
Official or state terrorism – referring to nations whose rule is based upon fear and oppression that reach similar to terrorism or such proportions.
Terrorist objectives.
1. Recognition
Groups seeking recognition require events that have high probability of attracting media attention. Specific incidents may be suicide bombing in public place (e. g. a green market), hijacking of an aircraft, the kidnapping of a politician or other prominent person, the seizing of occupied buildings (schools, hospitals) or other hostage barricade situations. Once they gain attention, the terrorists may demand that political statement be disseminated. Terrorist groups sometimes use organizational names or labels designed to imply legitimacy or widespread support. For example, a tiny isolated group may use “front”, “army”, or “brigade” in its name to achieve this effect.
2. Coercion.
Coercion is the attempt to force a desired behavior by individuals, groups, or governments. This objective calls for a strategy of a very selective targeting which rely on publicly announced bombings, destruction of property and other acts which are initially less violent than the taking of human life. Contemporary examples include the bombing of corporate headquarters and banking facilities with little or no loss of life.
3. Intimidation.
Intimidation attempts to prevent individuals or groups from acting: coercion attempts to force actions. Terrorists may use intimidation to reduce the effectiveness of security forces by making them afraid to act. Intimidation can discourage competent citizens from seeking or accepting positions within the government. The threat of violence can also keep the general public from taking part in important political activities such as voting. As in the case of coercion, terrorists use a strategy of selective targeting although they may intend the targets to look as though they were chosen indiscriminately.
4. Provocation.
Provoking overreaction on the part of government forces. The strategy normally calls for attacking targets symbolic of the government ( for example, the police, the military, and other officials). Attacks of this type demonstrate vulnerability to terrorist acts and contribute to a loss of confidence in the government’s ability to provide security. More important, if the security forces resort to a heavy-handed response, the resulting oppression can create public sympathy, passive acceptance, or active support for an insurgent or terrorist group.
5. Insurgency support.
Terrorism in support of an insurgency is likely to include provocation, intimidation, coercion and the quest for recognition.. Terrorism can also aid an insurgency by causing the government to overextend itself in attempting to protect all possible targets. Other uses of terrorist skills in insurgencies include acquiring funds, coercing recruits, obtaining logistical support, and enforcing internal discipline.
The media is a valuable “helper” by giving terrorists international recognition and also to attract recruits, obtaining funds. Once they gain attention, the terrorists may demand that political statements be disseminated. The danger is that this kind of attention tends to incite acts of violence by other terrorist groups. Terrorists use different methods and taking hostages, bombing, arson (low risk action) assassinations, ambushes and hijacking are the most popular ones.
Factors that may contribute to terrorism:high population growth rates, high unemployment, weak economies, extremism, ethnic, religious or territorial conflict.
Organization and tactic
Organized terror is “organized construction”:
–search and recruitment of people (active and passive supporters), including informants and supporters in government agencies, counterintelligence and police
–getting money (robberies, illegal operations with drugs and weapons, legal business, searching for donors with the same political views)
–security system, including a system of “cells” or small groups (some groups may organize multifunctional cells that combine several skills into one tactical unit). Preparing places where members can hide, relax, get medical care; keep weapons, money, special literature. System also includes fake IDs and counter-intelligence (detection of traitors, preventing collapse of the group and uncontrolled criminal activity (robberies)
–training camps (shooting, working with explosives). If the group is state supported or directed, the leadership usually includes one or more members who have been trained and educated by the sponsoring state
–“brainwashing” sessions (the group may include professional terrorists for hire who are not necessarily ideologically motivated)
–planning the actions
–making special connections with other groups and mafia
The typical terrorist organization is pyramidal. This format takes more people to support operations than to carry them out. Therefore, the majority of people who work in terrorist organizations serve to keep terrorists in the field. The most common job in terrorist groups is support, not combat.
Usually, organization is divided into 4 levels:
1st level. Command level. The smallest, most secret group at the top.
2nd level. Active cadre. Responsible for carrying out the mission of the terrorist organization..
3rd level. Active supporters. The active supporters are critical to terrorist operations. Any group can carry out a bombing, but to maintain a campaign of bombings takes support. Active supporters keep the terrorists in the field. They maintain communication channels, provide safe houses, gather intelligence. This is the largest internal group in the organization, and one which can be effectively countered by economic measures.
4th level. Passive supporters.
Most terrorist groups number fewer than 50 people and are incapable of mounting a long-term campaign. Under the command of only a few people, the group is divided according to specific tasks. Intelligence sections are responsible for assessing targets and planning operations. Support sections provides the means necessary to carry out the assault, and the tactical units are responsible for the actual terrorist action.
Terrorist organizations tend to have two primary types of subunits: a cell and a column.
The cell is the most basic type. Composed of 4 to 6 people, the cell usually has a mission specialty, but it my be a tactical cell or an intelligence section. In some organizations, the duties of tactical cells very with the assignment. Other cells may exist as support wing.
Sometimes groups of cells will form to create columns. Columns are semiautonomous conglomerations of cells with a variety of specialties and a separate command structure. As combat units, columns have questionable effectiveness. They are usually too cumbersome to be used in major operations, and the secrecy demanded by terrorism prevents effective inter-column cooperation. Hence, columns are most often found fulfilling a function of combat support.
Terrorist groups can be divided into three categories:
a. non-state supported groups which operate autonomously, receiving no support from any government
b. state supported groups, which operate alone but receive support from one or more governments
c. state directed groups, which operate as the agents of a government, receiving substantial intelligence, logistic, and operational support
Methods
Hostage-taking.
An overt seizure of one or more people to gain publicity, concessions, or ransom in return for the release of the hostage or hostages. While dramatic, hostage situations are risky for the terrorist in an unfriendly environment..
You must always negotiate if hostages have been taken. Negotiation produces some advantages for you. These advantages are: (a) the longer situation is prolonged, the more intelligence can be gathered on the location, motivation and identity, (b) the passage of time generally reduces anxiety, allowing the hostage taker to assess the situation rationally, (c) given enough time, the hostages may find a way to escape on their own, (c) the necessary resolve to kill or hold hostages lessens with timer, (d) terrorists may make mistakes. The negotiation team must have information to support negotiations (you get it from interviews with witnesses, escaped and released hostages, and captured suspects — it’s very important to get the identities, personalities, motives, habits and abilities of the offenders).
One of the complications facing you in a siege involving hostages is the Stockholm syndrome where sometimes hostages can develop a sympathetic rapport with their captors. If this helps keep them safe from harm, this is considered to be a good thing, but there have been cases where hostages have tried to shield the captors during an assault or refused to co- operate with the authorities in bringing prosecutions. (In Britain if the siege involves perpetrators who are considered by the government to be terrorists, then if an assault is to take place, the civilian authorities hand command and control over to military).
Bombing.
Advantage includes it’s attention-getting capacity and the terrorist’s ability to control casualties through time of detonation and placement of the device. The bomb is a popular weapon, because it is cheap to produce, easy to make, has variable uses, and is difficult to detect and trace after the action. In Iraq they usually use booby-trapped vehicles and car- bombs. A car bomb is an explosive device placed in a car or other vehicle and then exploded. It is commonly used as a weapon of assassination, terrorism or guerrilla warfare to kill the occupant(s) of the vehicle, people near the blast site, or to damage buildings or other property. Car bombs act as their own delivery mechanisms and can carry a relatively large amount of explosives without attracting suspicion. The earliest car bombs were intended for assassination. These were often wired to the car’s ignition system – to explode when the car was started. Ignition triggering is now rare, as it is easy to detect and hard to install – interfering with the circuitry is time-consuming and car alarms can be triggered by drains on the car’s electrical system. Also, the target may start the car remotely (inadvertently or otherwise), or the target may be a passenger a safe distance away when the car starts. It is now more common for assassination bombs to be affixed to the underside of the car and then detonated remotely or by the car motion. The bomb is exploded as the target approaches or starts the vehicle or, more commonly, after the vehicle begins to move, when the target is more likely to be inside. For
this reason, security guards have to check the underside of vehicles with a long mirror mounted on a pole.
The effectiveness of a car bomb is that an explosion detonated inside a car is momentarily contained. If the force of explosion were to double each fraction of a second and the car were to contain the explosion for one second before its chassis gave way, this would result in a much greater force then if the detonation took place outside the car. Therefore a greater amount of damage is obtained from a given amount of explosive. Car bombs are also used by suicide bombers who seek to ram the car into a building and simultaneously detonate it. Defending against a car bomb involves keeping vehicles at a distance from vulnerable targets by using Jersey barriers, concrete blocks or by hardening buildings to withstand an explosion. Where major public roads pass near government buildings, road closures may be the only option (thus, the portion of Pennsylvania Avenue immediately behind the White house is closed to traffic. These tactics encourage potential bombers to target unprotected targets, such as markets.
Suicide attack.
A major reason for the popularity of suicide attacks is tactical advantages over other types of terrorism. A terrorist can conceal weapons, make last-minute adjustments, infiltrate heavily guarded targets and he does not need a remote or delayed detonation, escape plans or rescue teams. Suicide attacks often target poorly- guarded, non-military facilities and personnel. Examples of different suicide attacks include:
–attempted suicide attack with a plane as target
–suicide car bomb
–suicide attack by a boat with explosives
–suicide attack by a woman
–suicide attack by a bicycle with explosives
–suicide attack by a hijacked plane with fuel: September 11, 2001 attacks
–suicide attack by diverting a bus to an abyss
–suicide attack with guns
Ambush
A well-planned ambush seldom fails. The terrorists have time on their side, and can choose a suitable place. Raid (armed attack) on facilities usually have one of three purposes: to gain access to radio or TV stations (to make a public statement); to demonstrate the government’s inability to guarantee the security of critical facilities; or to acquire money and weapons ( by bank pr armory robberies).
Assassination
Assassination is the oldest terrorist tactic. Targets mostly are government officials, as well as the defectors from the terrorist group.
Kidnapping
Kidnapping is usually a covert action and the perpetrators may not make themselves known for some time, while hostage
–takers seek immediate publicity. Because of the time involved, a successful kidnapping requires elaborate planning and logistics, although the risk to the terrorists is less than in a hostage situation.
Sabotage
Its objective is to demonstrate how vulnerable society is to the terrorists’ actions on utilities, communications and transportation systems. In the more developed countries they are so interdependent that a serious disruption of one affects all and gains immediate public attention. Sabotage of industrial, commercial or military facilities is a tool to show vulnerability of the target and the society while simultaneously making a statement or political, or monetary demand.
Hoaxes
A threat against a person’s life causes him and those around him to devote more time and effort to security measures.. A bomb threat can close down a commercial building, empty a theater, or disrupt a transportation system at no cost to the terrorist. The longer-term effects of false alarms on the security forces are more dangerous than the temporary disruption of the hoax. Repeated threats that do not materialize dull the analytical and operational effectiveness of security personnel.
COUNTERTERRORISM
FIRST, I HAVE TO ANSWER IDIOT KELLY
Homegrown terrorists
Homegrown terrorists are not easy targets, especially if you deal with a "lonely wolf" (individual) or a separate small group of 2-3 people. They are not connected to any terrorist groups, organizations, radical parties, mafia.
That's why you have to:
1. Recruit assets among illegal weapons dealers, they have to inform you about anybody, trying to buy a gun and a lot of ammunition, automatic weapons, explosives.
2. The assets have to inform you about any person with radical views and ready for radical action (to blackmail the government and make it change it's policy).
NSA has to fix all phone calls where you hear key words like "kill", "gun", "explosive", "explosion", "FBI", "surveillance", "kidnapping", "sniper", "torture", etc.
3. Detect people who search Internet, looking for instructions on "home made" explosives.
4. Watch terrorists in jail – they might keep contacts with with those outside. Watch terrorists who are out of jail.
5. Keep under control all shooting ranges in the country and people who try to get training as snipers.
6. ATTENTION: keep under control scientists who work with explosives. And companies which produce weapons, explosives, and sell them.
7. Watch army veterans with radical views, pay special attention to those who served in special forces and involved in war zones special operations.
Now comes my instruction
Responses to terrorism include:
–targeted laws, criminal procedures, deportations and enhanced police powers
–target hardening, such as locking doors or adding traffic barriers
–pre-emptive or reactive military action
–increased intelligence and surveillance activities
–pre-emptive humanitarian activities
–more permissive interrogation and detention policies
–official acceptance of torture as a valid tool
You must gather the following information:
1. Group information.
Names, ideology (political or social philosophy), history of the group, dates significant to the group, and dates when former leaders have been killed or imprisoned (terrorist groups often strike on important anniversary dates).
2. Financial information.
Source of funds, proceeds from criminal activities, bank accounts information (sudden influxes of funding or bank withdrawals indicate preparation for activity). It’s also important to determine the group’s legal and financial supporters. Generally, anyone who would write an official letter of protest or gather names on a petition for a terrorist is a legal supporter. Sometimes, an analysis of support will reveal linkages and mergers with other groups.
3. Personnel information.
List of leaders, list of members (and former members), any personnel connections with other groups of similar ideology. The skills of all group members (weapons expertise, electronics expertise) – knowing the skills of the group is an important part of threat assessment. If the philosophy revolves around one leader, it’s important to know what will occur if something happens to that leader. Often, the analysis of family background is useful to determine how radically a leader or member was raised. Group structure, particularly if the organizational pattern is cellular, determines who knows whom.
As a group, terrorists are very team-oriented and always prepared for suicide missions. They are well-prepared for their mission, are willing to take risks and are attack-oriented. If captured, they will usually not confess or snitch on others as ordinary criminals do. Traditional law enforcement are not that effective when it comes to the investigation or intelligence of terrorism.
4. Location information.
Location of group’s headquarters, location of group’s “safe” houses (where they hide from authorities) and location of the group’s “stash” houses (where they hide weapons and supplies). Regular attacks on “stash” houses is the most frequently used counterterrorism technique). It’ important to specify the underground that exists where terrorists can flee. Terrorists like to live in communal homes instead of living alone.
Remember this:
1. Knowing just the functions of terrorism is a fight. Since terrorists are usually trying to provoke government’s overreaction, anything the government can do to keep itself from overreacting works against them.
2. Since terrorists are usually trying to provoke government’s overreaction, anything the government can do to keep itself from overreacting works against them. Since terrorists are trying to gain control of the media, anything on the part of the media which stifles exposure also stiles terrorism. Bombings make the best pictures (watch TV! ), that’s why terrorists use them mostly.
3. Terrorists often demand to release political prisoners, but this is never a true objective. The real trick is politization of all prisoners, the winning over of new recruits among the prison population.
4. Go after financial supporters of terrorism, not the terrorists themselves. It’s only with narcoterrorism that this strategy fails, since the drug market doesn’t respond to simple supply-demand forces.
5. Terrorists are imitators, not innovators. They often wait until some other group makes the first move. Most of them do this because they are sorely trying to imitate military strategy, others do it because of standardized paramilitary training or textbook lessons in guerrilla tactics, and still others do it to throw off suspicion from themselves..
6. The Stockholm Syndrome works in the favor of anti-terrorist forces. The longer the hostages stay alive, the less likelihood harm will come to them. With this syndrome, the hostages come to think of their captors as protecting them from the police and soon start to identify with their captors. The captors themselves start to develop a parent/child relationship with their hostages. Other syndromes include the Penelope Syndrome, where women find violent criminals sexually attractive.
7. In assessing the threat of terrorism, it’s important to concentrate on counting the number of incidents, not the number of victims or the value of harm. The only true comparison is the number of attacks since terrorists often have no idea themselves about how many victims will be killed by their actions. Nationalist groups tend to seek a high number of fatalities while revolutionary groups tend to seek fewer deaths and more wounds or injuries. Splinter or spin-off groups seem more interested in death counts and fatalities. The point is that no matter how many victims are targeted, the group is only a threat via its number of attacks as a percent of total activity.
8. Do count the number of victims saved by any preventive action. If you manage through some leverage to get the terrorist leader to stop things with a cease-fire agreement, regardless of whether further negotiation follows or not, it will help your agency if you have calculated how many lives you’ve saved, and can report this information to policymakers. Everyone wins by a cease-fire – the terrorist leaders look good, your leaders look good too. After the cease-fire, it’s important to also measure the resumed level of violence and compare to pre-cease-fire levels.
9. Giving into terrorists’ demands for political change only changes the pattern of violence, not violence itself. Economic and political reforms aimed at helping a certain group and resolving its grievances will win over some supporters among the general population, but in the long-run, will create new problems and a new set of grievances over the precise implementation of policy and the degree of power sharing. A much better strategy is to initiate economic and political reforms for all nation. Economic development solutions have worked in Ireland, Uruguay andItaly.
10. Reduction of recruits, supplies and support. You have to reduce the number of active trainee members of the terrorist organization. Capture and imprisonment works (it has helped to keep Spain fairly terrorism-free), as well as preemptive strikes against training camps. The number of terrorists captured or killed should be counted, and this can be put as the denominator in a fraction with the number of government security forces killed in the numerator. You’ve also got to keep weapons, ammo and supplies out of hands of terrorists by destruction of their “stash” houses. Unfortunately, many religious terrorist groups operate under the cover of religion and blowing up religious buildings has a strong negative effect.
11. Terrorism does not respond to coalition-based sanctions which are intended to express the international community’s disregard for them. Terrorist actually want their enemies to wage a war on terrorism because this gives them some pseudo-legitimacy that they are soldiers-at war. If they are broken up from receiving any psychological rewards or sympathy from their social support groups, this strategy might work.
12. Sharing of information and intelligence by counter-terrorism agents is essential. But there’s always a threat, thata secret source might be “burnt out” during such“sharing”.
13. Terrorist groups with a cell structure are most likely to thwart human intelligence since the purpose of the cell structure is to prevent any members from knowing who is the immediate leader. This may or may not be true with some groups (like the IRA) which mix family with business, depending upon levels of fidelity. The best approach for such groups may electronic surveillance. However, groups with military or paramilitary organization might be easier to infiltrate or penetrate.
In November, 2011 more than a dozen spies working for the CIA in Iran and Lebanon have been caught and the U. S. government fears they will be or have been executed. The spies were paid informants recruited by the CIA for two distinct espionage rings targeting Iran and the Beirut-based Hezbollah organization.
In Beirut, two Hezbollah double agents pretended to go to work for the CIA. Hezbollah then learned of the Beirut Pizza Hut restaurant where multiple CIA officers were meeting with several agents, according to the four current and former officials briefed on the case. The CIA used the code word "PIZZA" when discussing where to meet with the agents. From there, Hezbollah's internal security arm identified at least a dozen informants, and the identities of several CIA case officers.
CIA officers ignored the rule that the operation could be compromised by using the same location for meetings with multiple assets. Idiots who loved free pizza paid by the U. S. government too much.
Use special influence methods against terrorists
Tortures
Torture is a category of methods of interrogation designed to shock, hurt and humiliate the object and get information or to make him do something (if used for blackmail). Points to remember:
–ongoing torture decreases pain sensitivity
–people with strong will power take torture as a test
–resistance to torture is often a form of hysterics after arrest
–the object could take himself as a martyr if you torture him too much
–torture could damage object’s psyche and you won’t be able to work with him (that’s why we keep terrorists in Guantanamo Bay without trial – we turn them into idiots)
–people usually trust "after torture information" more than voluntary confessions
–there are different types of torture and professionals often combine them
Techniques of psychological torture include:
– fake execution
– complete isolation ("wall therapy")
– daylight deprivation
– forcible narcotics addiction. Here you can use depressants, stimulants, opiates or hallucinogens : depressants (alcohol, barbiturates, antianxiety drugs
with effects of euphoria, tension reduction,, muscle relaxation, drowsiness; stimulants (cocaine, amphetamine, methamphetamine (crystal meth), with effects of fast
euphoria, exhilaration, high physical and mental energy, reduced appetite, perceptions of power, and sociability; hallucinogens with effects of euphoria, hallucinations, distorted perceptions and sensations
–making the object observe others being tortured (such as family members)
–abuse of object’s national, religious feelings or political views)
The effects of psychological torture are: anxiety, depression, fear, psychosis, difficulty concentrating, communication disabilities, insomnia, impaired memory, headaches, hallucinations, sexual disturbances, destruction of self-image, inability to socialize
Techniques of physical torture include:
–food, water, sleep deprivation
–damage to vital body organs (brain, lungs, kidneys, liver, private parts) plus electric shock. The brain is particularly dependent on a continuous and stable supply of oxygen and glucose.
–rape
–face deformation
–water cure ( the torturer pours water down the throat of the subject to inflict the terror of drowning. In another variation, the subject is tied or held don in a chair, his face is covered with a cloth or plastic sheet, and water is poured slowly or quickly over his face to encourage him to talk
The effects of physical torture are: extreme (unbearable) pain, hypertension, fatigue, cardiopulmonary and other disorders, brain atrophy.
Special psychology
1. "Brain washing" (implantation of new ideas). The process is: isolation from outside world ("information vacuum") — sleep and food limitation (very effective) — "bombing" with slogans – ideological aggression – achieving the result (brain is loaded). The object is now ready to brainwash newcomers.
2. "Behavior modification" (by placing into a group). The process is: initial contact — introduction to a group — mutual interests — mutual activity–mutual ideas — control and prevention of any negative contacts outside the group. No rush, no pressure.
3. Special psychotherapy methods: talk + drugs + blondes + alcohol (used for recruitment)
Attention: An alcoholic is more impulsive, untrustful and unreliable; he demonstrates a poverty of ideas and incapacity for attention. He usually has serious personality maladjustments. He’s immature, insecure, oversensitive and anxious. Without alcohol he’s unable to meet and enjoy people socially, and suffers from marked feeling of inferiority. Besides, alcoholics suffer from vitamin B1 deficiency, which leads to anatomic changes in the central nervous system and heart with symptoms like anorexia, fatigability, and sleep disturbances. Other common symptoms are irritability, poor memory, inability to concentrate, heart pain.
4. "Transfer" (the object is placed in a regular hospital and then he’s transferred to a mental health clinic or jail). In jail you can use such methods an accelerated work schedule (to exhaust the object), turning him into a number to traumatize his psyche, physical punishment or a threat of punishment to keep the object tense and depressed; senseless labor to destroy his personality. Remember: the lower the intellectual level of the object, the more aggressive he is and more sensitive to incentive or punishment.
You can actually re-organize any object’s behavior by combining rewards and punishments, exposing him to feared situations and teaching him an instinct of a total (political) obedience.
Imprisonment is a very strong (sometimes — ultimate) tool. My friend who spent 10 years in jail described the changes in his behavior like this:
1st year – aggression as self-defense method (to survive)
2nd year – less personal tension, attempts to adapt the mind and body to the new, isolated way of life
3rd, 4th, 5th – gaining some inside status
6th, 7th – life in jail looks like natural routine
10th – euphoria
3. Blackmail
Used to force a person to do something (or stop the action) against his will; it’s used also for recruitment. Blackmail methods include:
1. Leaking "dirt" on the object through media
2. Creating problems in his personal life and career
3. Straight blackmail (threatening to make public certain compromising facts about him)
4. Placing weapons, drugs, secret documents in object’s house or office, followed by search and arrest
5. Accusations of rape (robbery) (use hookers for that)
6. Blackmail by pressing family members. Careful, object may commit suicide after intense blackmail, especially if he is an intellectual. Physical surveillance
Methods
"One line" – officers follow the object forming a line behind him and passing him one by one.
"Two lines" – officers form two lines on both sides of the street.
"Circle" – officers block the area and start searching (used in case they lose the object).
"Fork" – one officer (a car) moves in front of the object, another one – behind, other officers (cars) move along parallel streets
"Box" – used when the object enters supermarket, hotel, restaurant. One or two officers follow the object, the others wait for him at the exits.
"Demonstration" – officers demonstrate their presence to press the object and lower his activity.
"Provocation" – officers attack the object, beat him, steal (secret) documents. Often used to lower his activity if he’s trying to play James Bond.
"Outstrip" – officers do not follow the object because they know exactly where he’s going.
"Football" – officers pass the object to each other (car — a group — bicyclist — car…)
"Movie" – the crew watches the object in stages: first day — to the subway only, second day — from subway to his office, etc. (used abroad). The crew has to have a female member if they are watching a woman (she could use the ladies room for a secret meeting) and members of various ethnicities (white, black, Latino) because the object could go to a specific ethnic area.
If you’re the object and you’ve noticed surveillance:
Don’t rush, move at the same speed.
Relax at the nearest bar (and relax the crew).
Don’t show how professional you are by trying to disappear, otherwise they could intensify surveillance or even neutralize you (smash your car, beat you up).
Postpone the operation you were engaged in.
Use a "draught" if you need to see your agent no matter what. Change lanes (if you are driving), stop the car and then drive left or right.
If you don’t see surveillance, that means either there’s no surveillance or you’ve failed in counter-surveillance. Discreetly watch the agent who’s coming to meet you and try to detect any possible surveillance; or you may have been "outstripped. "
Surveillance crew mistakes:
The same crew follows the object all day long.
The object "rules" the crew and calculates it (he moves faster — the crew moves faster).
A crew member is too noticeable (unusual dress, haircut, disabled parts of the body, too fat or too skinny, too ugly or too pretty).
The crew starts to search possible hiding places for espionage evidence right after the object leaves (and he may be watching).
The crew leaves traces after a secret search of the object’s house (office).
The crew does not report its mistakes or the fact that they’ve lost the object.
The crew is not professional (using childish tricks like jumping out of a subway train just before the doors close).
Technical Surveillance
1. Visual surveillance. Done through special holes in the ceilings and walls, through the windows from the opposite building (car) or by installing the camera inside the house (you can substitute something, like a clock, for the same thing but "stuffed" with a camera or recorder. ) You can use informant as well to watch the object outside his house (especially if you want to do a secret search).
2. Listening devices. The easiest thing is to listen to the object’s phone (record all calls, including those dialed "by mistake"). If you work inside his apartment, make sure you equip the room where he usually talks. Attention: avoid widespread mistake when your agent keeps the listening device on his body; install a miniature device in his clothes or shoes, because the object could try a test and ask the agent to take off his clothes or invite him to the sauna or pool.
3. If you are working abroad, listen 24/7 to local counterintelligence surveillance radiofrequencies.
4. Reading the mail. When you control the object’s mail, remember he could use multiple addresses and PO boxes. Open all the letters with no return address or PO box. Watch when you open the letter — the object could leave a tiny piece of paper, hair, etc. to check if anybody opened the letter. Analyze the text carefully — there could be a cipher or the words with double meaning (jargon), especially when you read mafia mail.
5. Combination of above-mentioned methods
Investigation
Stages:
– secure and examine carefully the crime scene (every person who enters the scene is a potential destroyer of physical evidence)
– record the scene (make photos, sketches, notes with detailed written description of the scene with the location of evidences recovered)
– collect physical evidences (blood, semen, saliva, hair, documents, drugs, weapons and explosives, poisonous substances, fingerprints, traces, soils and minerals, fiber) and package everything
– collect confessions and eyewitnesses accounts and then
– make a plan of investigation and correct it later
– research similar crimes and criminals involved
– make a model (profile) of the suspect
– analyze expertise data
– work with secret sources
– cooperate with other divisions (abroad, if needed)
– make arrest
– interrogate
Arrest
In daytime arrest people discreetly – don’t inflame extra public irritation. There’s a general rule: more arrests – less crime prevention (after being in jail people, engage in more sophisticated and secret criminal activity). After mass arrests at certain places (buildings) repeat the action in a day or two.
Procedure:
– chasing the object, block the area into circles (follow the plan for a certain area) and try to "push" him to a certain place where your team is waiting
– taking the object in the street: look around for his partner(s), who could shoot you from behind
– be on the alert if anybody tries to talk to you in the street – it could be an attempt to divert your attention
– arresting a crew, shoot and disarm any people with guns first
– never hesitate to shoot terrorists – some of them have mental problems and won’t think a second before shooting you
– arrest a dangerous object while he’s relaxed (drugs, alcohol, sex, sleep) and don’t let him kill himself, eliminate evidences or warn his partners. (Most people feel more relaxed when traveling abroad. ) To take the object alive, scream, shoot over his head, use smoke and light grenades.
– camouflage your team (as ambulance workers, construction workers, vendors, etc. )
– if there’s a crowd around the object, shoot in the air and order everybody to lie down— the object has no choice
– if the object is well armed and very dangerous (and you have intelligence information on that), you have to shoot him even in a very crowded area as you never know what he’s going to do next — take hostages, shoot people or blow up a bomb (three wounded people is a better score than three hundred dead).
Interrogation
Interrogation is a conversational process of information gathering. The intent of interrogation is to control an individual so that he will either willingly supply the requested information or, if someone is an unwilling participant in the process, to make the person submit to the demands for information.
Remember, people tend to:
–talk when they are under stress and respond to kindness and understanding.
–show deference when confronted by superior authority, This is culturally dependent, but in most areas of the world people are used to responding to questions from a variety of government and quasi-government officials.
–operate within a framework of personal and culturally derived values. People tend to respond positively to individuals who display the same value system and negatively when their core values are challenged.
–respond to physical and, more importantly, emotional self-interest.
–fail to apply or remember lessons they may have been taught regarding security if confronted with a disorganized or strange situation
–be more willing to discuss a topic about which the interrogator demonstrates identical or related experience or knowledge
–appreciate flattery and exoneration from guilt
Tricks:
a) "good cop / bad cop"
b)"story under a story" (after intense interrogation the object tells a different story — which is not true, either)
c) "bombing" with questions
d) pressure by not interrogating
e) "silence makes your situation worse" trick
f) "admit one small episode and that’s it" trick
g) "I help you — you help me" trick
h) "shift" – try to shift the blame away from the suspect to some other person or set of circumstances that prompted the subject to commit the crime. That is, develop themes containing reasons that will justify or excuse the crime. Themes may be developed or changed to find one to which the accused is most responsive.
BONUS. HOW I REMOVED HILLARY CLINTON
I made the biggest mistake in my life when I've helped Russian President Putin to steal the inevitable victory from people's presidential candidate 2016 – Hillary Clinton.
I was sure she was going to start World War III with Russia.
Instead, I brought to power American Hitler, Putin's close friend Donald Trump who's going to terminate the United States.
HILLARY IS BACK FOR THE ANTI-TRUMP REVOLUTION WITH HER NEW SLOGAN :"RESIST, INSIST, PERSIST, ENLIST". 03. 28. 2017
Now, she is back and I want to bring justice, democracy and truth back, and to help her with anti-Trump revolution. Let's do it.
Here's the story.
To: Vladimir Putin
President of the Russian Federation
Kremlin, Moscow
September 4, 2013
(via special form on Putin's personal site kremlin. ru)
Dear Mr. President,
The information I got recently from reliable sources indicates that Hillary Clinton, a former Secretary of State, is preparing for a very aggressive presidential campaign 2016. It's important that she's supported not only by the Rockefellers clan ($3 trln worth) but also by high-ranked neocons, hawks like a former VP Dick Cheney and also the the majority of Joint Chiefs of Staff.
That means that Hillary Clinton, in case she's elected the U. S. President in 2016, will start the World War III with Russia for Russian resources.
That's why I advise you, Mr. President to use your propaganda, political and technical possibilities (FSO and its division, FSO Special Communications and Information Service) to compromise Hillary Clinton and remove her from the presidential race 2016.
Thank you.
Mikhail Kryzhanovsky, a former KGB intelligence officer, a former CIA "Filament"
Earlier I've sent the same letter to Sergey Naryshkin, Russian Duma (the parliament) Speaker, KGB spy in 1978-1982, a former Putin's Executive Office Chief in 2008-2011.

Sergey Naryshkin
He sent the letter to FSB (Russian Counterespionage Service) Chief Alexander Bortnikov, because I've mentioned a possible threat of Putin's assassination by the Secret Service team.

Alexander Bortnikov, FSB Director
Secret Service killers (Klemm, Lieneman, Gurevich – see business cards below) were hunting me in New York in 2012, later Secret Service special agent Jason Pietramica asked me if I want to go to Moscow myself (to kill Putin, of course).
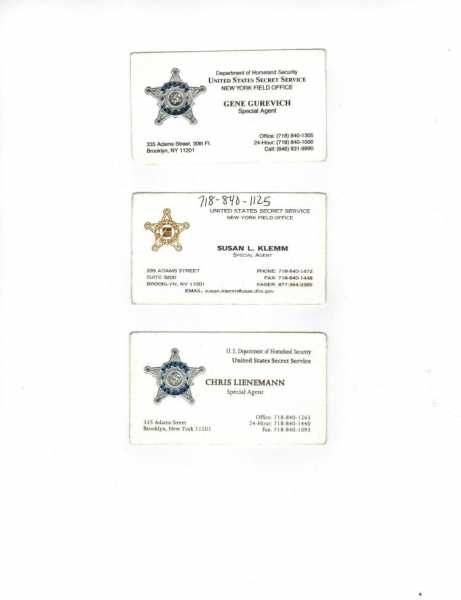
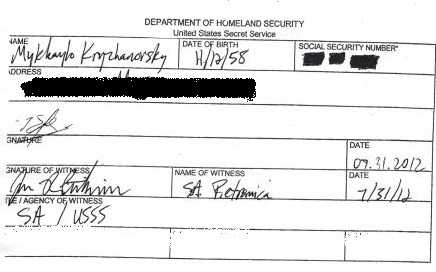
I can imagine how angry Putin was when Naryshkin showed him my letter – he had no doubt that Hillary Clinton, his personal enemy, was behind the Secret Service planned murder.
FSB answered me fast:
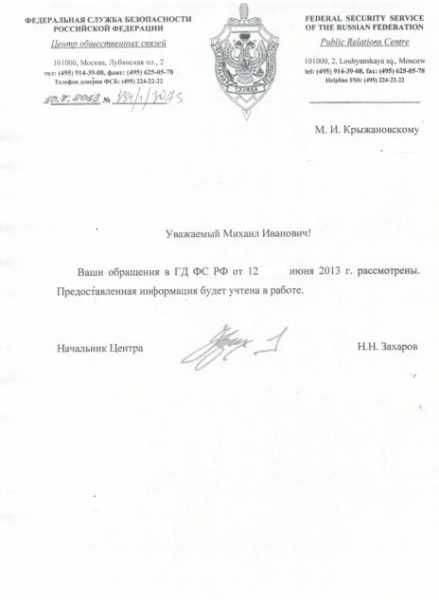
October 3, 2013
Federal Security Service of the Russian Federation
101100, 2 Lubyanskaya sq, Moscow
Dear Mikhail Ivanovich,
We received and looked into your letter to the Duma. We'll use the information you've provided.
N. N. Zakharov, Chief, Center of Public Relations
Remember FSB (a former KGB) have very well trained killers – I was a member (a sniper) of KGB "Nabat" anti-terror team and I know very well how they work. If Putin orders to kill Hillary Clinton, they'll do it no matter what.
Putin got my letter and answered fast, because Hillary Clinton was his personal enemy since 2008 presidential campaign when she said:" He [Putin] was a KGB agent. By definition he doesn’t have a soul, " He got very angry and punched her back saying that at a minimum, she should have a head, "
Besides, Putin knows me in person as the author of the White House Special Handbook and Espionage Handbook, and that's why took my warning very seriously.
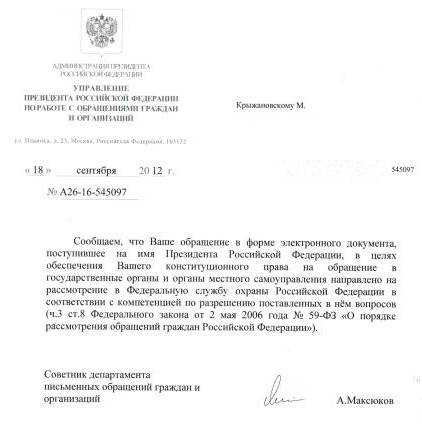
From: President of The Russian Federation
Executive Office
Directorate for Communication
Ilinka str, 23/16, Moscow
September 18, 2012
#A26-16-545097
To. M. Kryzhanovsky
We inform you the letter to you've sent via e-form was received by the President.
The letter has been sent to the Federal Protective Service.
A. Maksukov
Adviser, Directorate of Communication
Attention.
The Federal Protective Service (FSO) is a federal government agency concerned with the tasks related to the protection of several, mandated by the relevant law, high-ranking state officials, including the President of Russia, as well as certain federal properties. FSO includes the Russian Presidential Security Service. The FSO has roughly 50, 000 uniformed personnel plus several thousand plainclothed personnel and controls the Cheget that can be used in the event of global nuclear war.
It also operates a secure communications system for senior government officials. The FSO is a powerful institution with a range of rights and powers, including the right to conduct searches and surveillance without warrants, make arrests, and give orders to other state agencies.
FSO includes Special Communications and Information Service of Russia (Spetsviaz or SCID).
It is is a cryptologic intelligence agency of Russia responsible for the collection and analysis of foreign communications and foreign signals intelligence, as well as protecting Russian government communications and information systems, which involves information security and cryptanalysis/cryptography. It is the equivalent to the United States National Security Agency.
Putin appointed these two chiefs to be in charge of the "Hillary-2016" Project.

Dmitriy Kochnev, FSO Director

Alexey Mironov, the Special Communications and Information Director
Kochnev prepared the "Hillary" Project plan to be signed by Putin and executed by Mironov.
According to this plan SCID :
1. Had penetrated the servers of the Democratic National Committee and Debbie Wasserman Schultz, the DNC chair, Clinton campaign chairman John Podesta in person, whose private emails were published by WikiLeaks in the days leading up to the Democratic convention. Putin called the hacking and release of nearly 20, 000 emails from the DNC "a public service". The e-mails the DNC's favoritism of Hillary Clinton over Bernie Sanders published by Wikileaks compromised Dems' leaders and Hillary too.
2. Hacked Hillary Clinton's personal phone and computer. All information was transferred straight to Trump who got the possibility to correct his strategy. And leaked to the public.
3. Hacked the 2016 elections.
How?
First, the attackers probed election offices well in advance in order to find ways to break into their computers. Second, closer to the election, when it was clear from polling data which states would have close electoral margins, the attackers spreaded malware into voting machines in some of the states, rigging the machines to shift a few percent of the vote.
THE END
Комментарии
Книги автора
Автор: Kryzhanovsky
Монография / Детектив Документация История Мемуар Политика Приключения
Аннотация отсутствует
Объем: 4.903 а.л.
21:50 25.04.2024 | оценок нет
Автор: Kryzhanovsky
Монография / Политика
Аннотация отсутствует
Объем: 7.336 а.л.
19:40 20.04.2024 | оценок нет
Автор: Kryzhanovsky
Статья / Политика
Аннотация отсутствует
Объем: 0.065 а.л.
22:06 16.04.2024 | оценок нет
Автор: Kryzhanovsky
Монография / Детектив Политика
Аннотация отсутствует
Объем: 11.376 а.л.
00:02 13.04.2024 | оценок нет
Автор: Kryzhanovsky
Очерк / Политика
Аннотация отсутствует
Объем: 0.171 а.л.
22:24 11.04.2024 | оценок нет
Автор: Kryzhanovsky
Очерк / Политика
Аннотация отсутствует
Объем: 0.168 а.л.
22:21 11.04.2024 | оценок нет
Автор: Kryzhanovsky
Монография / Детектив История Мемуар Политика Приключения Психология
Аннотация отсутствует
Объем: 21.247 а.л.
23:28 26.12.2023 | оценок нет






